Spaces:
Sleeping
Sleeping
Upload 6 files
Browse files- GVA/LICENSE +21 -0
- GVA/MANIFEST.in +3 -0
- GVA/README.md +594 -0
- GVA/pyproject.toml +6 -0
- GVA/setup.cfg +18 -0
- GVA/setup.py +63 -0
GVA/LICENSE
ADDED
|
@@ -0,0 +1,21 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
MIT License
|
| 2 |
+
|
| 3 |
+
Copyright (c) 2023 morpheuslord
|
| 4 |
+
|
| 5 |
+
Permission is hereby granted, free of charge, to any person obtaining a copy
|
| 6 |
+
of this software and associated documentation files (the "Software"), to deal
|
| 7 |
+
in the Software without restriction, including without limitation the rights
|
| 8 |
+
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
|
| 9 |
+
copies of the Software, and to permit persons to whom the Software is
|
| 10 |
+
furnished to do so, subject to the following conditions:
|
| 11 |
+
|
| 12 |
+
The above copyright notice and this permission notice shall be included in all
|
| 13 |
+
copies or substantial portions of the Software.
|
| 14 |
+
|
| 15 |
+
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
|
| 16 |
+
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
|
| 17 |
+
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
|
| 18 |
+
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER
|
| 19 |
+
LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM,
|
| 20 |
+
OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE
|
| 21 |
+
SOFTWARE.
|
GVA/MANIFEST.in
ADDED
|
@@ -0,0 +1,3 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
include GVA/*.py
|
| 2 |
+
include GVA/commands/*.py
|
| 3 |
+
include GVA/*.txt
|
GVA/README.md
ADDED
|
@@ -0,0 +1,594 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
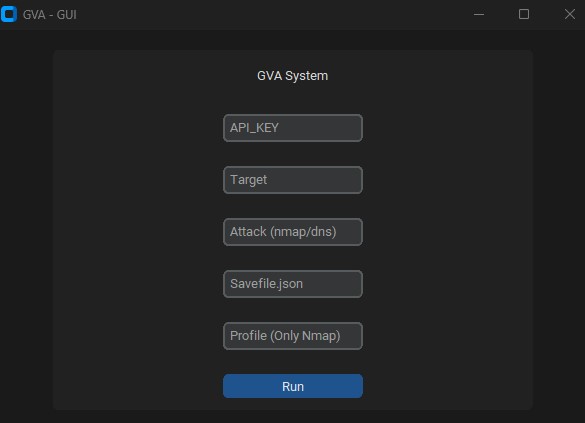
|
|
|
|
|
|
|
|
|
|
|
|
|
|
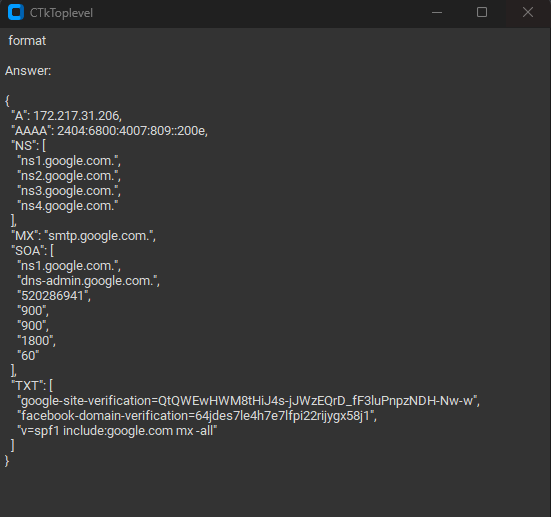
|
|
|
|
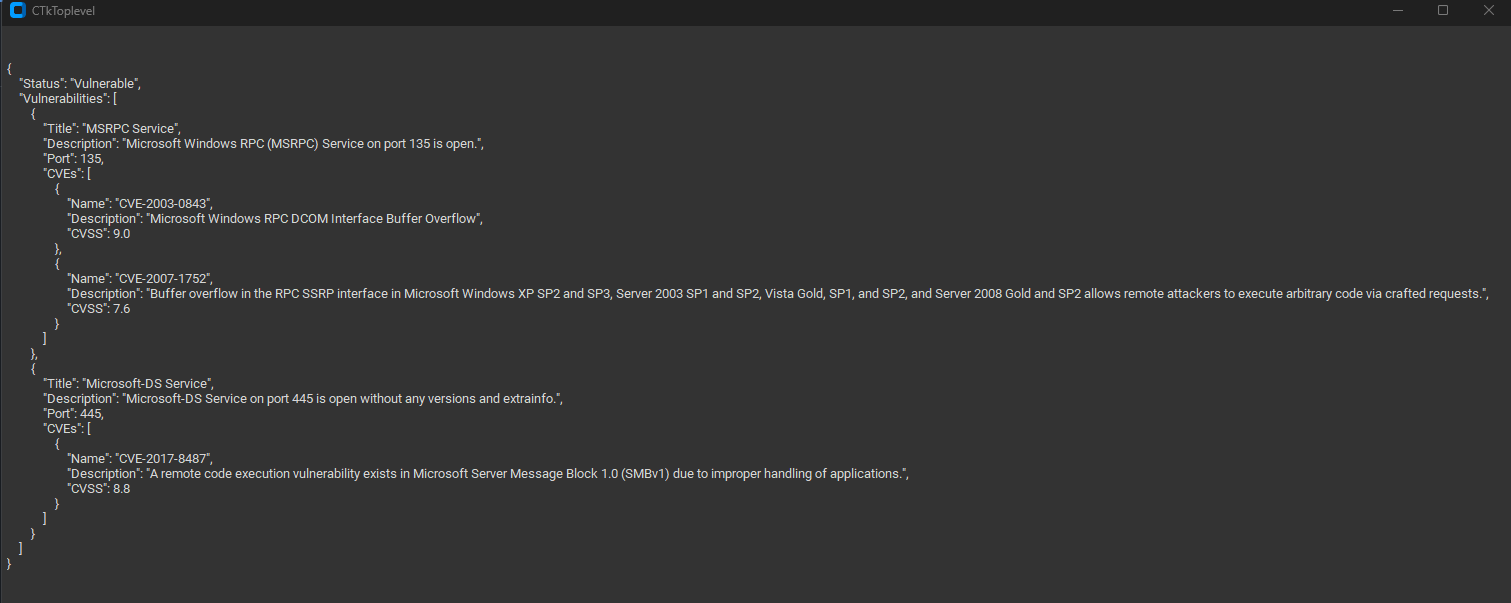
|
|
|
|
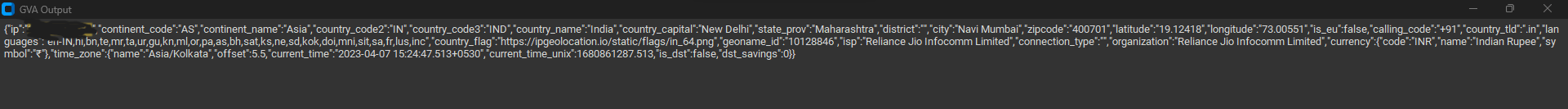
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
# GPT_Vuln-analyzer
|
| 2 |
+
|
| 3 |
+
This is a Proof Of Concept application that demostrates how AI can be used to generate accurate results for vulnerability analysis and also allows further utilization of the already super useful ChatGPT made using openai-api, python-nmap, dnsresolver python modules and also use customtkinter and tkinter for the GUI version of the code. This project also has a CLI and a GUI interface, It is capable of doing network vulnerability analysis, DNS enumeration and also subdomain enumeration.
|
| 4 |
+
|
| 5 |
+
## Requirements
|
| 6 |
+
|
| 7 |
+
- Python 3.10 or above
|
| 8 |
+
- All the packages mentioned in the requirements.txt file
|
| 9 |
+
- OpenAI API
|
| 10 |
+
- Bard API (MakerSuite Palm)
|
| 11 |
+
- HuggingFace token (with llama2 access )
|
| 12 |
+
- IPGeolocation API
|
| 13 |
+
- Wireshark and tshark (both added to path)
|
| 14 |
+
|
| 15 |
+
## Usage Package
|
| 16 |
+
|
| 17 |
+
### Import packages
|
| 18 |
+
|
| 19 |
+
```bash
|
| 20 |
+
cd package && pip3/pip install .
|
| 21 |
+
```
|
| 22 |
+
|
| 23 |
+
Simple import any of the 3 packages and then add define the variables accordingly
|
| 24 |
+
|
| 25 |
+
```python
|
| 26 |
+
from GVA.scanner import NetworkScanner
|
| 27 |
+
from GVA.dns_recon import DNSRecon
|
| 28 |
+
from GVA.geo import geo_ip_recon
|
| 29 |
+
from GVA.jwt import JWTAnalyzer
|
| 30 |
+
from GVA.menus import Menus
|
| 31 |
+
from GVA.packet_analysis import PacketAnalysis
|
| 32 |
+
from GVA.ai_models import NMAP_AI_MODEL
|
| 33 |
+
from GVA.ai_models import DNS_AI_MODEL
|
| 34 |
+
from GVA.ai_models import JWT_AI_MODEL
|
| 35 |
+
from GVA.assets import Assets
|
| 36 |
+
from GVA.subdomain import sub_enum
|
| 37 |
+
from GVA import gui
|
| 38 |
+
|
| 39 |
+
# The components defined
|
| 40 |
+
dns_enum = DNSRecon()
|
| 41 |
+
geo_ip = geo_ip_recon()
|
| 42 |
+
p_ai_models = NMAP_AI_MODEL()
|
| 43 |
+
dns_ai_models = DNS_AI_MODEL()
|
| 44 |
+
port_scanner = NetworkScanner()
|
| 45 |
+
jwt_analizer = JWTAnalyzer()
|
| 46 |
+
sub_recon = sub_enum()
|
| 47 |
+
asset_codes = Assets()
|
| 48 |
+
packet_analysis = PacketAnalysis()
|
| 49 |
+
|
| 50 |
+
# KEEP IT BLANK IF YOU HAVE NO CLUE THE MENU WILL ASK TO FILL IT ONCE ACTIVE
|
| 51 |
+
lkey = "LLAMA API KEY"
|
| 52 |
+
lendpoint = "LLAMA ENDPOINT"
|
| 53 |
+
keyset = "AI API KEY"
|
| 54 |
+
output_loc = "OUTPUT LOCATION FOR PCAP"
|
| 55 |
+
threads = 200 # Default INT 200 but can be increased.
|
| 56 |
+
target_ip_hostname_or_token = "TARGET IP, HOSTNAME OR TOKEN"
|
| 57 |
+
profile_num = "PROFILE FOR NMAP SCAN"
|
| 58 |
+
ai_set = "AI OF CHOICE"
|
| 59 |
+
akey_set = "OPENAI API KEY"
|
| 60 |
+
bkey_set = "BARD API KEY"
|
| 61 |
+
ai_set_args = "" # Keep it blank at any cost
|
| 62 |
+
llamakey = "LLAMA RUNPOD API KEY"
|
| 63 |
+
llamaendpoint = "LLAMA RUNPOD ENDPOINT"
|
| 64 |
+
|
| 65 |
+
Menus(
|
| 66 |
+
lamma_key=lkey,
|
| 67 |
+
llama_api_endpoint=lendpoint,
|
| 68 |
+
initial_keyset=keyset,
|
| 69 |
+
threads=threads,
|
| 70 |
+
output_loc=output_loc,
|
| 71 |
+
target=target_ip_hostname,
|
| 72 |
+
profile_num=profile_num,
|
| 73 |
+
ai_set=ai_set,
|
| 74 |
+
openai_akey_set=akey_set,
|
| 75 |
+
bard_key_set=bkey_set,
|
| 76 |
+
ai_set_args=ai_set_args,
|
| 77 |
+
llama_runpod_key=llamakey,
|
| 78 |
+
llama_endpoint=llamaendpoint
|
| 79 |
+
)
|
| 80 |
+
|
| 81 |
+
|
| 82 |
+
gui.application()
|
| 83 |
+
```
|
| 84 |
+
|
| 85 |
+
## Usage CLI
|
| 86 |
+
|
| 87 |
+
- First Change the "OPENAI_API_KEY", "GEOIP_API_KEY" and "BARD_API_KEY" part of the code with OpenAI api key and the IPGeolocation API key in the `.env` file
|
| 88 |
+
- For the `llama-api` option or specific the llama runpod serverless endpoint deployment option requires you to enter the `serverless endpoint ID` from runpod and also your `RUNPOD API KEY`
|
| 89 |
+
|
| 90 |
+
```python
|
| 91 |
+
GEOIP_API_KEY = ''
|
| 92 |
+
OPENAI_API_KEY = ''
|
| 93 |
+
BARD_API_KEY = ''
|
| 94 |
+
RUNPOD_ENDPOINT_ID = ''
|
| 95 |
+
RUNPOD_API_KEY = ''
|
| 96 |
+
```
|
| 97 |
+
|
| 98 |
+
- second install the packages
|
| 99 |
+
|
| 100 |
+
```bash
|
| 101 |
+
pip3 install -r requirements.txt
|
| 102 |
+
or
|
| 103 |
+
pip install -r requirements.txt
|
| 104 |
+
```
|
| 105 |
+
|
| 106 |
+
- run the code python3 gpt_vuln.py
|
| 107 |
+
|
| 108 |
+
```bash
|
| 109 |
+
# Regular Help Menu
|
| 110 |
+
python gpt_vuln.py --help
|
| 111 |
+
|
| 112 |
+
# Rich Help Menu
|
| 113 |
+
python gpt_vuln.py --r help
|
| 114 |
+
|
| 115 |
+
# Specify target with the attack
|
| 116 |
+
python gpt_vuln.py --target <IP/hostname/token> --attack dns/nmap/jwt
|
| 117 |
+
|
| 118 |
+
# Specify target and profile for nmap
|
| 119 |
+
python gpt_vuln.py --target <IP/hostname/token> --attack nmap --profile <1-13>
|
| 120 |
+
(Default:1)
|
| 121 |
+
|
| 122 |
+
# Specify target for DNS no profile needed
|
| 123 |
+
python gpt_vuln.py --target <IP/hostname/token> --attack dns
|
| 124 |
+
|
| 125 |
+
# Specify target for Subdomain Enumeration no profile used default list file
|
| 126 |
+
python gpt_vuln.py --target <HOSTNAME> --attack sub
|
| 127 |
+
|
| 128 |
+
# Specify target for Subdomain Enumeration no profile used custom list file
|
| 129 |
+
python gpt_vuln.py --target <HOSTNAME> --attack sub --list <PATH to FILE>
|
| 130 |
+
|
| 131 |
+
# Specify target for geolocation lookup
|
| 132 |
+
python gpt_vuln.py --target <IP> --attack geo
|
| 133 |
+
|
| 134 |
+
# Specify PCAP file for packet analysis
|
| 135 |
+
python gpt_vuln.py --target <PCAP FILE> --attack pcap --output <OUTPUT FILE LOCATION> --thread NUM of threads <200:default>
|
| 136 |
+
|
| 137 |
+
# Specify the AI to be used for nmap
|
| 138 |
+
python gpt_vuln.py --target <IP> --attack nmap --profile <1-5> --ai llama /llama-api /bard / openai <default>
|
| 139 |
+
|
| 140 |
+
# Specify the AI to be used for dns
|
| 141 |
+
python gpt_vuln.py --target <IP> --attack dns --ai llama /llama-api /bard / openai <default>
|
| 142 |
+
|
| 143 |
+
# Specify the AI to be used for JWT analysis
|
| 144 |
+
python gpt_vuln.py --target <token> --attack jwt --ai llama /llama-api /bard / openai <default>
|
| 145 |
+
|
| 146 |
+
# Interactive step by step cli interface
|
| 147 |
+
python gpt_vuln.py --menu True
|
| 148 |
+
```
|
| 149 |
+
|
| 150 |
+
#### CLI Interface Option
|
| 151 |
+
|
| 152 |
+
```bash
|
| 153 |
+
________________________
|
| 154 |
+
| GVA Usage in progress... |
|
| 155 |
+
========================
|
| 156 |
+
\
|
| 157 |
+
\
|
| 158 |
+
^__^
|
| 159 |
+
(oo)\_______
|
| 160 |
+
(__)\ )\/\
|
| 161 |
+
||----w |
|
| 162 |
+
|| ||
|
| 163 |
+
┏━━━━━━━━━┳━━━━━━━━━━━━━━━━┓
|
| 164 |
+
┃ Options ┃ Utility ┃
|
| 165 |
+
┡━━━━━━━━━╇━━━━━━━━━━━━━━━━┩
|
| 166 |
+
│ 1 │ Nmap Enum │
|
| 167 |
+
│ 2 │ DNS Enum │
|
| 168 |
+
│ 3 │ Subdomain Enum │
|
| 169 |
+
│ 4 │ GEO-IP Enum │
|
| 170 |
+
| 5 | JWT Analysis |
|
| 171 |
+
| 6 | PCAP Analysis |
|
| 172 |
+
│ q │ Quit │
|
| 173 |
+
└─────────┴────────────────┘
|
| 174 |
+
Enter your choice:
|
| 175 |
+
```
|
| 176 |
+
|
| 177 |
+
The CLI interface has a few things to note.
|
| 178 |
+
|
| 179 |
+
- The API keys must be provided manually.
|
| 180 |
+
- The ones defined in the `.env` files work with the args options
|
| 181 |
+
- The process is similar but more organized.
|
| 182 |
+
|
| 183 |
+
### My views on Bard
|
| 184 |
+
|
| 185 |
+
Its same as Openai GPT3.5 but faster. It can generate the same answer but in 2 times the speed.
|
| 186 |
+
|
| 187 |
+
### OS Supported
|
| 188 |
+
|
| 189 |
+
| Preview | Code | Name | Working Status | OpenAI Status | Bard Status | LLama2 Status |
|
| 190 |
+
| -------------------------------------------------------------------------------------------------------------------- | ---- | --------- | -------------- | ------------- | ----------- | ----------------- |
|
| 191 |
+
| ") | LIN | GNU/Linux | ✅ | ✅ | ✅ | ❌ [did not test] |
|
| 192 |
+
| ") | WIN | Windows | ✅ | ✅ | ✅ | ✅ |
|
| 193 |
+
|
| 194 |
+
## Understanding the code
|
| 195 |
+
|
| 196 |
+
Profiles:
|
| 197 |
+
|
| 198 |
+
| Parameter | Return data | Description | Nmap Command |
|
| 199 |
+
| :-------- | :---------- | :--------------------------------------------------- | :---------------------------------------------------- |
|
| 200 |
+
| `p1` | `json` | Effective Scan | `-Pn -sV -T4 -O -F` |
|
| 201 |
+
| `p2` | `json` | Simple Scan | `-Pn -T4 -A -v` |
|
| 202 |
+
| `p3` | `json` | Low Power Scan | `-Pn -sS -sU -T4 -A -v` |
|
| 203 |
+
| `p4` | `json` | Partial Intense Scan | `-Pn -p- -T4 -A -v` |
|
| 204 |
+
| `p5` | `json` | Complete Intense Scan | `-Pn -sS -sU -T4 -A -PE -PP -PY -g 53 --script=vuln` |
|
| 205 |
+
| `p6` | `json` | Comprehensive Service Version Detection | `-Pn -sV -p- -A` |
|
| 206 |
+
| `p7` | `json` | Aggressive Scan with OS Detection | `-Pn -sS -sV -O -T4 -A` |
|
| 207 |
+
| `p8` | `json` | Script Scan for Common Vulnerabilities | `-Pn -sC` |
|
| 208 |
+
| `p9` | `json` | Intense Scan, All TCP Ports | `-Pn -p 1-65535 -T4 -A -v` |
|
| 209 |
+
| `p10` | `json` | UDP Scan | `-Pn -sU -T4` |
|
| 210 |
+
| `p11` | `json` | Service and Version Detection for Top Ports | `-Pn -sV --top-ports 100` |
|
| 211 |
+
| `p12` | `json` | Aggressive Scan with NSE Scripts for Vulnerabilities | `-Pn -sS -sV -T4 --script=default,discovery,vuln` |
|
| 212 |
+
| `p13` | `json` | Fast Scan for Common Ports | `-Pn -F` |
|
| 213 |
+
|
| 214 |
+
The profile is the type of scan that will be executed by the nmap subprocess. The Ip or target will be provided via argparse. At first, the custom nmap scan is run which has all the crucial arguments for the scan to continue. Next, the scan data is extracted from the huge pile of data driven by nmap. the "scan" object has a list of sub-data under "tcp" each labelled according to the ports opened. once the data is extracted the data is sent to the openai API Davinci model via a prompt. the prompt specifically asks for a JSON output and the data also to be used in a certain manner.
|
| 215 |
+
|
| 216 |
+
The entire structure of request that has to be sent to the openai API is designed in the completion section of the Program.
|
| 217 |
+
|
| 218 |
+
```python
|
| 219 |
+
class NetworkScanner():
|
| 220 |
+
def scanner(self, AIModels, ip: Optional[str], profile: int, akey: Optional[str], bkey: Optional[str], lkey, lendpoint, AI: str) -> str:
|
| 221 |
+
profile_arguments = {
|
| 222 |
+
1: '-Pn -sV -T4 -O -F',
|
| 223 |
+
2: '-Pn -T4 -A -v',
|
| 224 |
+
3: '-Pn -sS -sU -T4 -A -v',
|
| 225 |
+
4: '-Pn -p- -T4 -A -v',
|
| 226 |
+
5: '-Pn -sS -sU -T4 -A -PE -PP -PY -g 53 --script=vuln',
|
| 227 |
+
6: '-Pn -sV -p- -A',
|
| 228 |
+
7: '-Pn -sS -sV -O -T4 -A',
|
| 229 |
+
8: '-Pn -sC',
|
| 230 |
+
9: '-Pn -p 1-65535 -T4 -A -v',
|
| 231 |
+
10: '-Pn -sU -T4',
|
| 232 |
+
11: '-Pn -sV --top-ports 100',
|
| 233 |
+
12: '-Pn -sS -sV -T4 --script=default,discovery,vuln',
|
| 234 |
+
13: '-Pn -F'
|
| 235 |
+
}
|
| 236 |
+
# The scanner with GPT Implemented
|
| 237 |
+
nm.scan('{}'.format(ip), arguments='{}'.format(profile_arguments.get(profile)))
|
| 238 |
+
json_data = nm.analyse_nmap_xml_scan()
|
| 239 |
+
analyze = json_data["scan"]
|
| 240 |
+
match AI:
|
| 241 |
+
case 'openai':
|
| 242 |
+
try:
|
| 243 |
+
if akey is not None:
|
| 244 |
+
pass
|
| 245 |
+
else:
|
| 246 |
+
raise ValueError("KeyNotFound: Key Not Provided")
|
| 247 |
+
response = AIModels.GPT_AI(akey, analyze)
|
| 248 |
+
except KeyboardInterrupt:
|
| 249 |
+
print("Bye")
|
| 250 |
+
quit()
|
| 251 |
+
case 'bard':
|
| 252 |
+
try:
|
| 253 |
+
if bkey is not None:
|
| 254 |
+
pass
|
| 255 |
+
else:
|
| 256 |
+
raise ValueError("KeyNotFound: Key Not Provided")
|
| 257 |
+
response = AIModels.BardAI(bkey, analyze)
|
| 258 |
+
except KeyboardInterrupt:
|
| 259 |
+
print("Bye")
|
| 260 |
+
quit()
|
| 261 |
+
case 'llama':
|
| 262 |
+
try:
|
| 263 |
+
response = AIModels.Llama_AI(analyze, "local", lkey, lendpoint)
|
| 264 |
+
except KeyboardInterrupt:
|
| 265 |
+
print("Bye")
|
| 266 |
+
quit()
|
| 267 |
+
case 'llama-api':
|
| 268 |
+
try:
|
| 269 |
+
response = AIModels.Llama_AI(analyze, "runpod", lkey, lendpoint)
|
| 270 |
+
except KeyboardInterrupt:
|
| 271 |
+
print("Bye")
|
| 272 |
+
quit()
|
| 273 |
+
self.response = response
|
| 274 |
+
text = str(self.response)
|
| 275 |
+
return text
|
| 276 |
+
|
| 277 |
+
```
|
| 278 |
+
|
| 279 |
+
# Regex
|
| 280 |
+
|
| 281 |
+
We use Regex to extract only the important information from the custom prompt provided this reduces the total amount of unwanted
|
| 282 |
+
data
|
| 283 |
+
|
| 284 |
+
```python
|
| 285 |
+
def extract_data(json_string):
|
| 286 |
+
# Define the regular expression patterns for individual values
|
| 287 |
+
critical_score_pattern = r'"critical score": \["(.*?)"\]'
|
| 288 |
+
os_information_pattern = r'"os information": \["(.*?)"\]'
|
| 289 |
+
open_ports_pattern = r'"open ports": \["(.*?)"\]'
|
| 290 |
+
open_services_pattern = r'"open services": \["(.*?)"\]'
|
| 291 |
+
vulnerable_service_pattern = r'"vulnerable service": \["(.*?)"\]'
|
| 292 |
+
found_cve_pattern = r'"found cve": \["(.*?)"\]'
|
| 293 |
+
|
| 294 |
+
# Initialize variables for extracted data
|
| 295 |
+
critical_score = None
|
| 296 |
+
os_information = None
|
| 297 |
+
open_ports = None
|
| 298 |
+
open_services = None
|
| 299 |
+
vulnerable_service = None
|
| 300 |
+
found_cve = None
|
| 301 |
+
|
| 302 |
+
# Extract individual values using patterns
|
| 303 |
+
match = re.search(critical_score_pattern, json_string)
|
| 304 |
+
if match:
|
| 305 |
+
critical_score = match.group(1)
|
| 306 |
+
|
| 307 |
+
match = re.search(os_information_pattern, json_string)
|
| 308 |
+
if match:
|
| 309 |
+
os_information = match.group(1)
|
| 310 |
+
|
| 311 |
+
match = re.search(open_ports_pattern, json_string)
|
| 312 |
+
if match:
|
| 313 |
+
open_ports = match.group(1)
|
| 314 |
+
|
| 315 |
+
match = re.search(open_services_pattern, json_string)
|
| 316 |
+
if match:
|
| 317 |
+
open_services = match.group(1)
|
| 318 |
+
|
| 319 |
+
match = re.search(vulnerable_service_pattern, json_string)
|
| 320 |
+
if match:
|
| 321 |
+
vulnerable_service = match.group(1)
|
| 322 |
+
|
| 323 |
+
match = re.search(found_cve_pattern, json_string)
|
| 324 |
+
if match:
|
| 325 |
+
found_cve = match.group(1)
|
| 326 |
+
|
| 327 |
+
# Create a dictionary to store the extracted data
|
| 328 |
+
data = {
|
| 329 |
+
"critical score": critical_score,
|
| 330 |
+
"os information": os_information,
|
| 331 |
+
"open ports": open_ports,
|
| 332 |
+
"open services": open_services,
|
| 333 |
+
"vulnerable service": vulnerable_service,
|
| 334 |
+
"found cve": found_cve
|
| 335 |
+
}
|
| 336 |
+
|
| 337 |
+
# Convert the dictionary to JSON format
|
| 338 |
+
json_output = json.dumps(data)
|
| 339 |
+
|
| 340 |
+
return json_output
|
| 341 |
+
|
| 342 |
+
|
| 343 |
+
def AI(key: str, data: Any) -> str:
|
| 344 |
+
openai.api_key = key
|
| 345 |
+
try:
|
| 346 |
+
prompt = f"""
|
| 347 |
+
Do a NMAP scan analysis on the provided NMAP scan information
|
| 348 |
+
The NMAP output must return in a JSON format accorging to the provided
|
| 349 |
+
output format. The data must be accurate in regards towards a pentest report.
|
| 350 |
+
The data must follow the following rules:
|
| 351 |
+
1) The NMAP scans must be done from a pentester point of view
|
| 352 |
+
2) The final output must be minimal according to the format given.
|
| 353 |
+
3) The final output must be kept to a minimal.
|
| 354 |
+
4) If a value not found in the scan just mention an empty string.
|
| 355 |
+
5) Analyze everything even the smallest of data.
|
| 356 |
+
|
| 357 |
+
The output format:
|
| 358 |
+
{{
|
| 359 |
+
"critical score": [""],
|
| 360 |
+
"os information": [""],
|
| 361 |
+
"open ports": [""],
|
| 362 |
+
"open services": [""],
|
| 363 |
+
"vulnerable service": [""],
|
| 364 |
+
"found cve": [""]
|
| 365 |
+
}}
|
| 366 |
+
|
| 367 |
+
NMAP Data to be analyzed: {data}
|
| 368 |
+
"""
|
| 369 |
+
# A structure for the request
|
| 370 |
+
completion = openai.Completion.create(
|
| 371 |
+
engine=model_engine,
|
| 372 |
+
prompt=prompt,
|
| 373 |
+
max_tokens=1024,
|
| 374 |
+
n=1,
|
| 375 |
+
stop=None,
|
| 376 |
+
)
|
| 377 |
+
response = completion.choices[0].text
|
| 378 |
+
return extract_data(str(response))
|
| 379 |
+
except KeyboardInterrupt:
|
| 380 |
+
print("Bye")
|
| 381 |
+
quit()
|
| 382 |
+
```
|
| 383 |
+
|
| 384 |
+
The AI code defines an output format and commands the AI to follow a few pre-determined rules to increase accuracy.
|
| 385 |
+
The regex extraction code does the extraction and further the main function arranges them into tables.
|
| 386 |
+
|
| 387 |
+
## Using Bard AI
|
| 388 |
+
|
| 389 |
+
For you to use Bard AI you must signup to the MakerSuit Palm API for developer access and generate your API key from there. For links and how this works you can use this video [MakerSuit](https://www.youtube.com/watch?v=Ce1AOchQMzA&t=128s)
|
| 390 |
+
|
| 391 |
+
Once the API is acquired just add it to the `.env` file and you are good to go.
|
| 392 |
+
|
| 393 |
+
## Using LLama2 AI
|
| 394 |
+
|
| 395 |
+
Using LLama2 is one of the best offline and free options out there. It is currently under improvement I am working on a prompt that will better incorporate cybersecurity perspective into the AI.
|
| 396 |
+
I have to thank **@thisserand** and his [llama2_local](https://github.com/thisserand/llama2_local) repo and also his YT video [YT_Video](https://youtu.be/WzCS8z9GqHw). They were great resources. To be frank the llama2 code is 95% his, I just yanked the code and added a Flask API functionality to it.
|
| 397 |
+
|
| 398 |
+
The Accuracy of the AI offline and outside the codes test was great and had equal accuracy to openai or bard but while in code it was facing a few issues may be because of the prompting and all. I will try and fix it.
|
| 399 |
+
The speed depends on your system and the GPU and CPU configs you have. currently, it is using the `TheBloke/Llama-2-7B-Chat-GGML` model and can be changed via the `portscanner` and `dnsrecon` files.
|
| 400 |
+
|
| 401 |
+
For now, the llama code and scans are handled differently. After a few tests, I found out llama needs to be trained a little to operate like how I intended it to work so it needs some time. Any suggestions on how I can do that can be added to the discussions of this repo [Discussions Link](https://github.com/morpheuslord/GPT_Vuln-analyzer/discussions). For now, the output won't be a divided list of all the data instead will be an explanation of the vulnerability or issues discovered by the AI.
|
| 402 |
+
|
| 403 |
+
### Output
|
| 404 |
+
|
| 405 |
+
#### JWT Output:
|
| 406 |
+
|
| 407 |
+
```
|
| 408 |
+
GVA Report for JWT
|
| 409 |
+
┏━━━━━━━━━━━━━━━━━━━━━┳━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┓
|
| 410 |
+
┃ Variables ┃ Results ┃
|
| 411 |
+
┡━━━━━━━━━━━━━━━━━━━━━╇━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┩
|
| 412 |
+
│ Algorithm Used │ HS256 │
|
| 413 |
+
│ Header │ eyJhbGciOiAiSFMyNTYiLCAidHlwIjogIkpXVCJ9 │
|
| 414 |
+
│ Payload │ eyJzdWIiOiAiMTIzNDU2Nzg5MCIsICJuYW1lIjogIkpvaG4gRG9lIiwgImlhdCI6IDE1MTYyMzkwMjJ9 │
|
| 415 |
+
│ Signature │ │
|
| 416 |
+
│ PossibleAttacks │ None identified │
|
| 417 |
+
│ VulnerableEndpoints │ Unable to determine without additional information │
|
| 418 |
+
└─────────────────────┴──────────────────────────────────────────────────────────────────────────────────┘
|
| 419 |
+
```
|
| 420 |
+
|
| 421 |
+
#### Nmap output:
|
| 422 |
+
|
| 423 |
+
##### OpenAI and Bard:
|
| 424 |
+
|
| 425 |
+
```table
|
| 426 |
+
┏━━━━━━━━━━━━━━━━━━━━┳━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┓
|
| 427 |
+
┃ Elements ┃ Results ┃
|
| 428 |
+
┡━━━━━━━━━━━━━━━━━━━━╇━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━���━━━━━━━━━━━━━━━━━━━━┩
|
| 429 |
+
│ critical score │ High │
|
| 430 |
+
│ os information │ Microsoft Windows 11 21H2 │
|
| 431 |
+
│ open ports │ 80, 22, 445, 902, 912 │
|
| 432 |
+
│ open services │ http, ssh, microsoft-ds, vmware-auth, vmware-auth │
|
| 433 |
+
│ vulnerable service │ OpenSSH │
|
| 434 |
+
│ found cve │ CVE-2023-28531 │
|
| 435 |
+
└────────────────────┴─────────────────────────────────────────────────────┘
|
| 436 |
+
```
|
| 437 |
+
|
| 438 |
+
##### LLama2
|
| 439 |
+
|
| 440 |
+
```table
|
| 441 |
+
╭───────────────────────────────────────────── The GVA LLama2 ──────────────────────────────────────────────╮
|
| 442 |
+
│ │
|
| 443 |
+
│ │
|
| 444 |
+
│ │
|
| 445 |
+
│ Based on the provided NMAP data, I have conducted a thorough analysis of the target system's open ports │
|
| 446 |
+
│ and services, vulnerabilities, and operating system information. Here is my findings: Critical Score: │
|
| 447 |
+
│ The critical score for this target system is 7 out of 10. The system has several open ports that could │
|
| 448 |
+
│ potentially be exploited, including port 80 (HTTP), port 135 (RPC), and port 445 (Microsoft DS). While │
|
| 449 |
+
│ These ports are not necessarily vulnerable, they do indicate that the system is running services that │
|
| 450 |
+
│ could be targeted by attackers. Additionally, the system has an outdated version of Microsoft IIS │
|
| 451 |
+
│ running on port 80, which could be a potential vulnerability. OS Information: The target system is │
|
| 452 |
+
│ running Microsoft Windows 10 1607. Open Ports and Services: The target system has the following open │
|
| 453 |
+
│ ports: │
|
| 454 |
+
│ │
|
| 455 |
+
│ • Port 80: HTTP (Microsoft IIS httpd) │
|
| 456 |
+
│ • Port 135: RPC (Microsoft Windows RPC) │
|
| 457 |
+
│ • Port 445: Microsoft DS │
|
| 458 |
+
│ • Port 8000: Splunkd httpd All of these ports are currently open and have a state of "open". │
|
| 459 |
+
│ Vulnerable Services: Based on the CVEs found in the NMAP data, there are several potential │
|
| 460 |
+
│ vulnerabilities in the target system's services. These include: │
|
| 461 |
+
│ • CVE-2019-1489: An elevation of privilege vulnerability in Microsoft IIS that could be exploited by │
|
| 462 |
+
│ an attacker to gain control of the system. This vulnerability is related to the outdated version of │
|
| 463 |
+
│ Microsoft IIS running on port 80. │
|
| 464 |
+
│ • CVE-2017-0143: A remote code execution vulnerability in Microsoft Windows RPC that could be │
|
| 465 |
+
│ exploited by an attacker to execute arbitrary code on the target system. This vulnerability is │
|
| 466 |
+
│ related to the outdated version of Microsoft Windows RPC running on port 135. │
|
| 467 |
+
│ • CVE-2020-1362: A remote code execution vulnerability in Microsoft DS that could be exploited by an │
|
| 468 |
+
│ attacker to execute arbitrary code on the target system. This vulnerability is related to the │
|
| 469 |
+
│ outdated version of Microsoft DS running on port 445. Found CVEs: The following C │
|
| 470 |
+
│ │
|
| 471 |
+
╰───────────────────────────────────────────────────────────────────────────────────────────────────────────╯
|
| 472 |
+
```
|
| 473 |
+
|
| 474 |
+
#### DNS Output:
|
| 475 |
+
|
| 476 |
+
target is jainuniversity.ac.in
|
| 477 |
+
|
| 478 |
+
```table
|
| 479 |
+
┏━━━━━━━━━━┳━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┓
|
| 480 |
+
┃ Elements ┃ Results ┃
|
| 481 |
+
┡━━━━━━━━━━╇━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┩
|
| 482 |
+
│ A │ 172.67.147.95", "104.21.41.132 │
|
| 483 |
+
│ AAA │ │
|
| 484 |
+
│ NS │ mia.ns.cloudflare.com.","paul.ns.cloudflare.com. │
|
| 485 |
+
│ MX │ 30 aspmx5.googlemail.com.","30 aspmx4.googlemail.com.","20 alt2.aspmx.l.google.com.","30 │
|
| 486 |
+
│ │ aspmx3.googlemail.com.","30 aspmx2.googlemail.com.","20 alt1.aspmx.l.google.com.","10 aspmx.l.google.com. │
|
| 487 |
+
│ PTR │ │
|
| 488 |
+
│ SOA │ mia.ns.cloudflare.com. dns.cloudflare.com. 2309618668 10000 2400 604800 3600 │
|
| 489 |
+
│ TXT │ atlassian-sending-domain-verification=5b358ce4-5ad3-404d-b4b4-005bf933603b","include:_spf.atlassian.net │
|
| 490 |
+
└──────────┴───────────────────────────────────────────────────────────────────────────────────────────────────────────────────┘
|
| 491 |
+
```
|
| 492 |
+
|
| 493 |
+
#### GEO Location output:
|
| 494 |
+
|
| 495 |
+
```table
|
| 496 |
+
┏━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┳━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┓
|
| 497 |
+
┃ Identifiers ┃ Data ┃
|
| 498 |
+
┡━━━━━━━━━━━━━━━━━━━━━━━━━━━━━╇━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┩
|
| 499 |
+
│ ip │ █████████████ │
|
| 500 |
+
│ continent_code │ AS │
|
| 501 |
+
│ continent_name │ Asia │
|
| 502 |
+
│ country_code2 │ IN │
|
| 503 |
+
│ country_code3 │ IND │
|
| 504 |
+
│ country_name │ India │
|
| 505 |
+
│ country_capital │ New Delhi │
|
| 506 |
+
│ state_prov │ Haryana │
|
| 507 |
+
│ state_code │ IN-HR │
|
| 508 |
+
│ district │ │
|
| 509 |
+
│ city │ Gurugram │
|
| 510 |
+
│ zipcode │ 122003 │
|
| 511 |
+
│ latitude │ 28.44324 │
|
| 512 |
+
│ longitude │ 77.05501 │
|
| 513 |
+
│ is_eu │ False │
|
| 514 |
+
│ calling_code │ +91 │
|
| 515 |
+
│ country_tld │ .in │
|
| 516 |
+
│ languages │ en-IN,hi,bn,te,mr,ta,ur,gu,kn,ml,or,pa,as,bh,sat,ks,ne,sd,kok,doi,mni,… │
|
| 517 |
+
│ country_flag �� https://ipgeolocation.io/static/flags/in_64.png │
|
| 518 |
+
│ geoname_id │ 9148991 │
|
| 519 |
+
│ isp │ Bharti Airtel Limited │
|
| 520 |
+
│ connection_type │ │
|
| 521 |
+
│ organization │ Bharti Airtel Limited │
|
| 522 |
+
│ currency.code │ INR │
|
| 523 |
+
│ currency.name │ Indian Rupee │
|
| 524 |
+
│ currency.symbol │ ₹ │
|
| 525 |
+
│ time_zone.name │ Asia/Kolkata │
|
| 526 |
+
│ time_zone.offset │ 5.5 │
|
| 527 |
+
│ time_zone.current_time │ 2023-07-11 17:08:35.057+0530 │
|
| 528 |
+
│ time_zone.current_time_unix │ 1689075515.057 │
|
| 529 |
+
│ time_zone.is_dst │ False │
|
| 530 |
+
│ time_zone.dst_savings │ 0 │
|
| 531 |
+
└─────────────────────────────┴─────────────────────────────────────────────────────────────────────────┘
|
| 532 |
+
```
|
| 533 |
+
|
| 534 |
+
#### PCAP OUTPUT
|
| 535 |
+
|
| 536 |
+
```
|
| 537 |
+
Collecting Json Data
|
| 538 |
+
Extracting IP details...
|
| 539 |
+
Extracting DNS details...
|
| 540 |
+
Extracting EAPOL details...
|
| 541 |
+
Extracting TCP STREAMS details...
|
| 542 |
+
TCP streams can take some time..
|
| 543 |
+
Total Streams combination: 252
|
| 544 |
+
Number of workers in progress: 250
|
| 545 |
+
Completed
|
| 546 |
+
GVA Report for PCAP
|
| 547 |
+
┏━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┳━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┓
|
| 548 |
+
┃ Identifiers ┃ Data ┃
|
| 549 |
+
┡━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━╇━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━┩
|
| 550 |
+
│ PacketAnalysis.Services │ ['49943', '49958', '49934', '49944', '49931', '443', '49957'] │
|
| 551 |
+
│ PacketAnalysis.TCP Streams │ ['1', '4', '5', '2', '0', '3'] │
|
| 552 |
+
│ PacketAnalysis.Sources Address │ ['█████████████', '1.1.1.1', '█████████████', '█████████████', '█████████████', '█████████████'] │
|
| 553 |
+
│ PacketAnalysis.Destination Address │ ['█████████████', '1.1.1.1', '█████████████', '█████████████', '█████████████', '█████████████'] │
|
| 554 |
+
│ PacketAnalysis.DNS Resolved │ [] │
|
| 555 |
+
│ PacketAnalysis.DNS Query │ ['oneclient.sfx.ms'] │
|
| 556 |
+
│ PacketAnalysis.DNS Response │ ['oneclient.sfx.ms.edgekey.net', 'e9659.dspg.akamaiedge.net', 'oneclient.sfx.ms'] │
|
| 557 |
+
│ PacketAnalysis.EAPOL Data │ [] │
|
| 558 |
+
│ PacketAnalysis. Total Streams Data │ 126 │
|
| 559 |
+
└────────────────────────────────────┴────────────────────────────────────────────────────────────────────────────────────────────────────┘
|
| 560 |
+
```
|
| 561 |
+
|
| 562 |
+
# Usage GUI
|
| 563 |
+
|
| 564 |
+
The GUI uses customtkinter for the running of the code. The interface is straight forward the only thing required to remember is:
|
| 565 |
+
|
| 566 |
+
- When using dns attack dont specify the profile
|
| 567 |
+
|
| 568 |
+
```bash
|
| 569 |
+
python GVA_gui.py
|
| 570 |
+
```
|
| 571 |
+
|
| 572 |
+
### main window
|
| 573 |
+
|
| 574 |
+
|
| 575 |
+
|
| 576 |
+
### output_DNS
|
| 577 |
+
|
| 578 |
+
|
| 579 |
+
|
| 580 |
+
### output_nmap
|
| 581 |
+
|
| 582 |
+
|
| 583 |
+
|
| 584 |
+
### oytput_geo
|
| 585 |
+
|
| 586 |
+
|
| 587 |
+
|
| 588 |
+
## Advantage
|
| 589 |
+
|
| 590 |
+
- Can be used in developing a more advanced systems completly made of the API and scanner combination
|
| 591 |
+
- Has the capability to analize DNS information and reslove Mustiple records it a more better format.
|
| 592 |
+
- Can increase the effectiveness of the final system
|
| 593 |
+
- Can also perform subdomain enumeration
|
| 594 |
+
- Highly productive when working with models such as GPT3
|
GVA/pyproject.toml
ADDED
|
@@ -0,0 +1,6 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
[build-system]
|
| 2 |
+
requires = [
|
| 3 |
+
"setuptools>=54",
|
| 4 |
+
"wheel"
|
| 5 |
+
]
|
| 6 |
+
build-backend = "setuptools.build_meta"
|
GVA/setup.cfg
ADDED
|
@@ -0,0 +1,18 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
[metadata]
|
| 2 |
+
name = GVA
|
| 3 |
+
version = 1.1.8
|
| 4 |
+
author = Chiranjeevi G
|
| 5 |
+
author_email = [email protected]
|
| 6 |
+
description = Vuln analyzer and other basic recon tools with AI capabilities
|
| 7 |
+
long_description = file: README.md
|
| 8 |
+
long_description_content_type = text/markdown
|
| 9 |
+
url = https://github.com/morpheuslord/GVA_package
|
| 10 |
+
classifiers =
|
| 11 |
+
Programming Language :: Python :: 3
|
| 12 |
+
License :: OSI Approved :: MIT License
|
| 13 |
+
Operating System :: OS Independent
|
| 14 |
+
|
| 15 |
+
[options]
|
| 16 |
+
packages = find:
|
| 17 |
+
python_requires = >=3.10
|
| 18 |
+
include_package_data = True
|
GVA/setup.py
ADDED
|
@@ -0,0 +1,63 @@
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| 1 |
+
import codecs
|
| 2 |
+
import os
|
| 3 |
+
|
| 4 |
+
from setuptools import find_packages
|
| 5 |
+
from setuptools import setup
|
| 6 |
+
|
| 7 |
+
here = os.path.abspath(os.path.dirname(__file__))
|
| 8 |
+
|
| 9 |
+
with codecs.open(os.path.join(here, "README.md"), encoding="utf-8") as fh:
|
| 10 |
+
long_description = "\n" + fh.read()
|
| 11 |
+
|
| 12 |
+
VERSION = '1.1.8'
|
| 13 |
+
DESCRIPTION = 'Python Project for GPT-Vuln_analyzer'
|
| 14 |
+
LONG_DESCRIPTION = """
|
| 15 |
+
This is a Proof Of Concept application that demostrates how AI can be used to generate accurate
|
| 16 |
+
results for vulnerability analysis and also allows further utilization of the already super
|
| 17 |
+
useful ChatGPT made using openai-api, python-nmap, dnsresolver python modules and also use
|
| 18 |
+
customtkinter and tkinter for the GUI version of the code. This project also has a CLI and a
|
| 19 |
+
GUI interface, It is capable of doing network vulnerability analysis, DNS enumeration and
|
| 20 |
+
also subdomain enumeration.
|
| 21 |
+
"""
|
| 22 |
+
|
| 23 |
+
# Setting up
|
| 24 |
+
setup(
|
| 25 |
+
name="GVA",
|
| 26 |
+
version=VERSION,
|
| 27 |
+
author="Chiranjeevi G",
|
| 28 |
+
author_email="[email protected]",
|
| 29 |
+
description=DESCRIPTION,
|
| 30 |
+
long_description_content_type="text/markdown",
|
| 31 |
+
long_description=long_description,
|
| 32 |
+
packages=find_packages(),
|
| 33 |
+
install_requires=['aiohttp == 3.8.4',
|
| 34 |
+
'aiosignal == 1.3.1',
|
| 35 |
+
'async-timeout == 4.0.2',
|
| 36 |
+
'attrs == 22.2.0',
|
| 37 |
+
'certifi == 2022.12.7',
|
| 38 |
+
'charset-normalizer == 3.0.1',
|
| 39 |
+
'frozenlist == 1.3.3',
|
| 40 |
+
'idna == 3.4',
|
| 41 |
+
'multidict == 6.0.4',
|
| 42 |
+
'openai == 0.27.0',
|
| 43 |
+
'python-nmap == 0.7.1',
|
| 44 |
+
'requests == 2.28.2',
|
| 45 |
+
'tqdm == 4.65.0',
|
| 46 |
+
'urllib3 == 1.26.14',
|
| 47 |
+
'yarl == 1.8.2',
|
| 48 |
+
'dnspython',
|
| 49 |
+
'rich',
|
| 50 |
+
'cowsay',
|
| 51 |
+
'tk',
|
| 52 |
+
'customtkinter'],
|
| 53 |
+
keywords=['python', 'GPT', 'vulnerability',
|
| 54 |
+
'ai', 'vulnerability-assessment', 'network-scanning'],
|
| 55 |
+
classifiers=[
|
| 56 |
+
"Development Status :: 1 - Planning",
|
| 57 |
+
"Intended Audience :: Developers",
|
| 58 |
+
"Programming Language :: Python :: 3",
|
| 59 |
+
"Operating System :: Unix",
|
| 60 |
+
"Operating System :: MacOS :: MacOS X",
|
| 61 |
+
"Operating System :: Microsoft :: Windows",
|
| 62 |
+
]
|
| 63 |
+
)
|